by Cody Dumont
Monitoring and maintaining SCAP compliance can be an overwhelming task for any organization. Teams need to locate non-compliant hosts, reconfigure them, and verify that the systems are compliant. The SCAP Audit Summary Dashboard is easy to reference and allows compliance teams to focus on increasing the compliance rate to meet regulatory needs.
The Security Content Automation Protocol (SCAP) is a mixture of community developed security specifications used by a variety of government organizations. With a vast depth of knowledge amongst the information security community, SCAP has gained strength within the security automation community by ensuring a broad range of use cases are reflected in the SCAP functionality. The NIST SCAP web site (http://scap.nist.gov) provides security professionals with information about existing SCAP specifications and emerging specifications relevant to NIST's security automation recommendations. Tenable Tenable.sc users are able to use the NIST security automation recommendations through efficient auditing of devices with SCAP audit file support while leveraging advanced reporting using the dashboards and reports native to Tenable.sc.
This dashboard requires access to the Tier IV SCAP content files hosted by NIST and Tenable.sc audit scan results. You may find the Tier IV SCAP content files at the National Vulnerability Database by filtering on Tier IV (link: https://web.nvd.nist.gov/view/ncp/repository?tier=4&startIndex=0 ). The maintaining authority of the Tier IV content is the USGCB (United States Government Configuration Baseline) project, which is dedicated to simplifying a wide array of system configurations across entities. The Tier IV audit files will deliver compliance checks based on the recommended best practices from USGCB for software and operating system configurations, as denoted in the file name. The compliance scan data returned will be able to be sorted and analyzed on a pass/fail/manual checks scale. The dashboard will allow compliance teams to be more effective in addressing compliance failures.
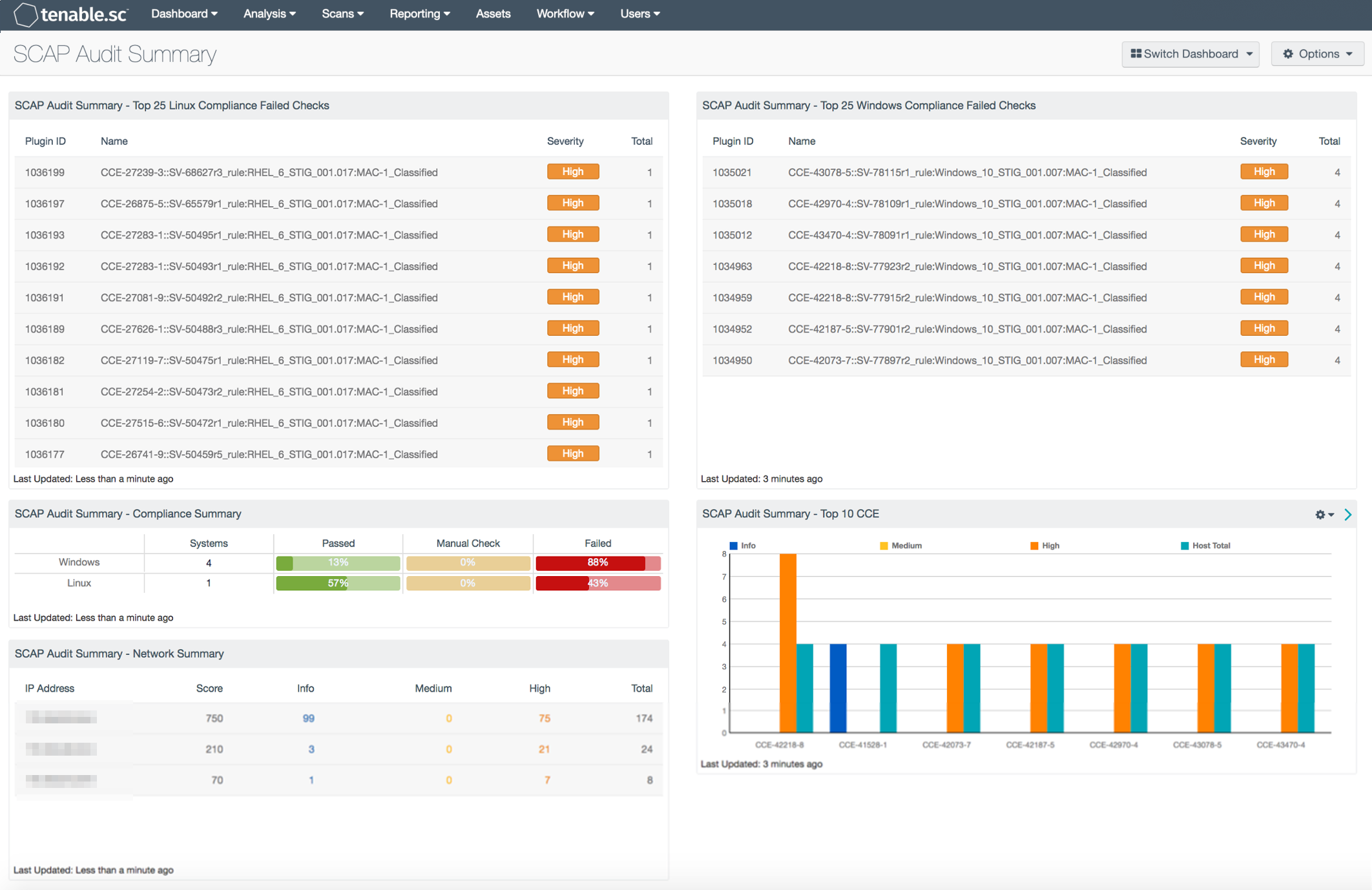
Immediate counts of the top 25 failed compliance checks on both Linux and Windows systems create an opportunity to remedy non-compliant hosts. Analysts can derive a better understanding of what checks need to have a passing value for each environment to meet the compliance standard. The top 25 Failed Checks data enables teams to ensure the compliance check is passed in the future. Compliance teams may also use the top 25 failed checks component to develop goals and milestones to present to management. The presented data will deliver a clear set of mission goals and will show progress as the goals are completed.
Compliance teams can easily identify and report on the successes and failures of the implemented SCAP Compliance program using the Tenable.sc data from the performance of the Tier IV compliance scans. Simple ratios provide information that enables clear communication of compliance status to stakeholders. This detailed data provides deeper analysis through standard data drill-down techniques as supported in Tenable.sc. By utilizing the SCAP Audit Summary dashboard, security teams will be able to isolate and identify network segments which need further attention to pass future compliance scans.
Identifying the most frequent Common Configuration Enumeration (CCE) checks allows security practitioners to see a high level view of compliance passes and failures, as well as hosts that require manual checks. By identifying checks that are frequently failed, compliance teams can identify problematic configuration settings and rapidly improve the compliance rate.
This dashboard is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The dashboard can be easily located in the Tenable.sc Feed under the category Compliance & Configuration Assessments. The dashboard requirements are:
- Tenable.sc 5.3.1
- Nessus 8.5.1
- NNM 5.9.1
Tenable's Tenable.sc Continuous View (CV) provides continuous network monitoring, vulnerability identification, and compliance monitoring. Tenable.sc is continuously updated with information about advanced threats and zero-day vulnerabilities, and new types of regulatory compliance configuration audit files. Active scanning examines the devices on the systems, running processes and services, detection of vulnerable software development applications, configuration settings, and additional vulnerabilities. With this information, analysts have greater insight to determine if supported software and systems are operating within the organization. Tenable.sc CV enables you to react to advanced threats, zero-day vulnerabilities and new forms of regulatory compliance.
This dashboard contains the following components:
- SCAP Audit Summary - Top 25 Linux Compliance Failed Checks: This component shows the top 25 Linux SCAP audits checks that have failed, and is sorted by the total number of checks found.
- SCAP Audit Summary - Compliance Summary: This matrix component provides a high level view of the compliance ratio using the total checks for each operating system type, to the number of checks that have passed, failed, or require manual verification.
- SCAP Audit Summary - Network Summary: This component displays a network summary table using a 24-bit mask to identify network segments. The table displays the number of checks performed and the results of said checks.
- SCAP Audit Summary - Top 25 Windows Compliance Failed Checks: This component shows the top 25 Windows SCAP audits checks that have failed, sorted by the total number checks found.
- SCAP Audit Summary - Top 10 CCE's: This bar chart provides a high level view into the Common Configuration Enumeration (CCE) as they pertain to SCAP audit checks.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success