A seven-year-old remote code execution vulnerability that is affecting Samba versions 3.5.0 and higher is making news this week. The vulnerability is billed as the WannaCry equivalent for *nix operating systems, and some are even calling it SambaCry since it affects the SMB protocol implementation and is potentially wormable. To be clear, this new vulnerability is unrelated to the SMB exploits that were used by the WannaCry ransomware. SambaCry is similar only because the vulnerability affects the SMB protocol. By leveraging data gathered by Tenable Nessus and the Tenable Passive Vulnerability Scanner (PVS), this dashboard is able to give security teams detailed insight into systems in their networks that may be vulnerable to exploitation.
The SambaCry vulnerability (CVE-2017-7494) is of concern for organizations due to the common use of Samba. Samba is a re-implementation of the SMB/CIFS networking protocol used by Microsoft Windows systems for *nix systems, including most Unix and Linux variants. Samba is commonly used in organizations to provide file and print services via Linux servers, and is standard in most distributions. The SambaCry vulnerability can be exploited with a single line of code. A malicious client can upload and cause the smbd server to execute a shared library from a writable share. Exploit modules are already available from Metasploit to exploit the vulnerability. Samba has released patches for versions 4.4 and newer, along with a mitigating workaround for systems that cannot be patched or upgraded for some reason.
In order to identify systems in the organization that may be vulnerable to exploitation via SambaCry, this dashboard discovers vulnerable systems based on active and passive scan data. Using filters for Linux OS local checks plugin families, the CVE ID and severities, the components in the dashboard are able to discover systems that may be vulnerable. Event data provides a list of connections between systems based on the standard SMB/CIFS port. Credentialed active scanning can be used to confirm instances of vulnerable Samba installations.
This dashboard is available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards and assets. The dashboard can be easily located in the SecurityCenter Feed under the category Threat Detection & Vulnerability Assessments. The dashboard requirements are:
- SecurityCenter 5.4.5
- Nessus 6.10.5
- PVS 5.3.0
- LCE 5.0.1
Tenable SecurityCenter is the market-defining continuous network monitoring solution, which assists organizations in securing their internal network. While SecurityCenter is continuously updated with information about advanced threats and zero-day vulnerabilities, there are several information plugins and collected events that help analysts anticipate systems that can be at risk to new threats such as SambaCry. Active scanning periodically examines systems to determine vulnerabilities and compliance concerns. Agent scanning enables scanning and detection of vulnerabilities on transient and isolated devices. SecurityCenter provides an organization with the most comprehensive view of risks within the network and the intelligence needed to support effective vulnerability remediation efforts.
The following components are included in this dashboard:
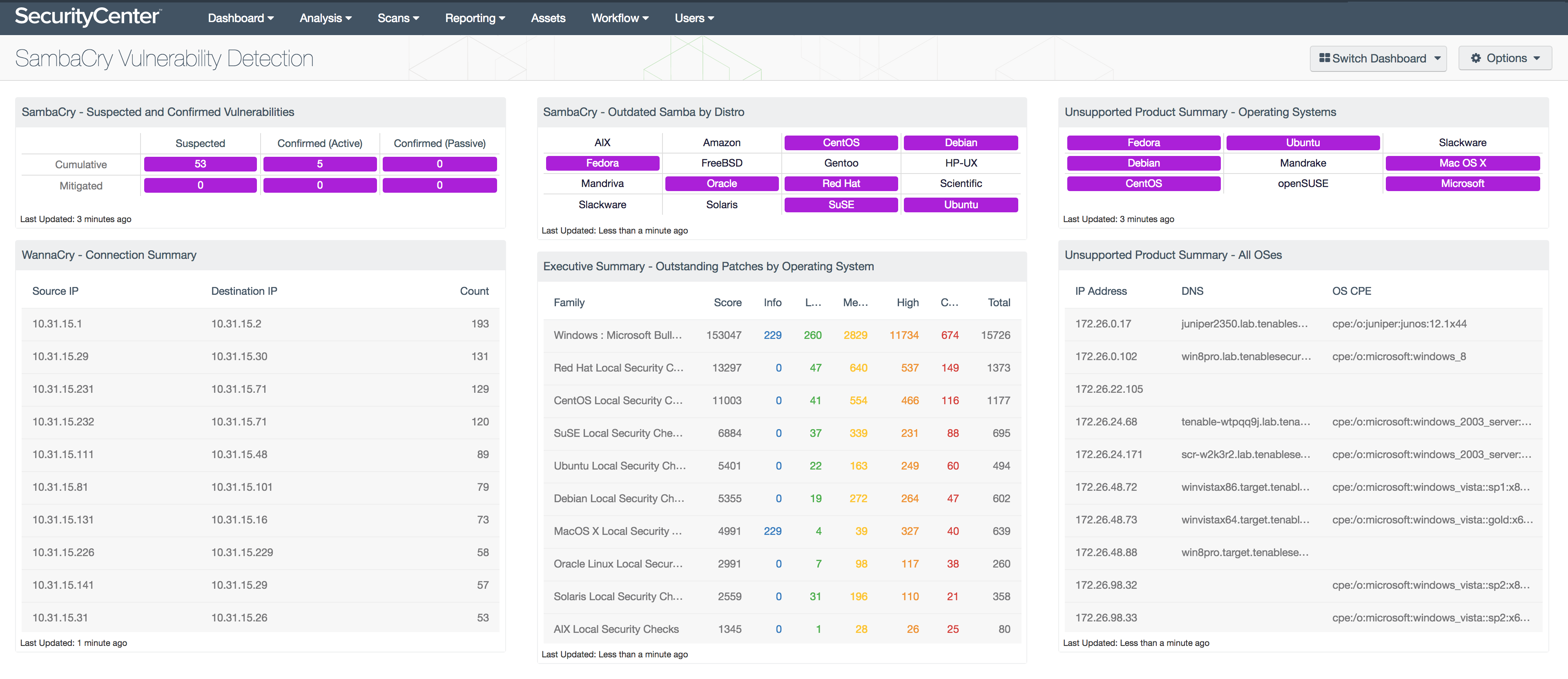
- SambaCry - Suspected and Confirmed Vulnerabilities: This matrix uses passive and active vulnerability data to provide a count of hosts that are or could be vulnerable to SambaCry exploitation.
- SambaCry - Outdated Samba by Distro: This matrix provides an indication of systems vulnerable to SambaCry based on Linux distribution.
- WannaCry - Connection Summary: This table shows a list of host-to-host communications that have had port 445 event logs generated, which indicates SMB related traffic.
- Executive Summary - Outstanding Patches by Operating System: This table shows counts of vulnerabilities based on the OS local security check plugins.
- Unsupported Product Summary - Operating Systems: This matrix indicates the presence of hosts determined to be running unsupported operating systems.
- Unsupported Product Summary - All OSes: This table lists the hosts determined to be running unsupported operating systems.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success