by Cody Dumont
Maintaining inventories and managing secure configurations are essential to protecting information systems. Default configurations for operating systems, applications, and devices tend to be geared for ease-of-use rather than security. If proper inventories are not maintained, hardware and software could be overlooked and not properly secured. Without change control processes in place, unauthorized changes may weaken network and system protections, and open up security holes. If system configurations are not locked down, attackers likely will find opportunities to exploit them.
The federal government relies heavily on external service providers and contractors to assist in carrying out a wide range of federal missions. Sensitive but unclassified federal information is routinely processed by, stored on, or transmitted through nonfederal information systems. Failing to properly protect this Controlled Unclassified Information (CUI) could impact the ability of the federal government to successfully carry out required missions and functions.
The National Institute of Standards and Technology (NIST) created Special Publication 800-171 "Protecting Controlled Unclassified Information in Nonfederal Information Systems and Organizations" to provide recommended requirements for protecting the confidentiality of CUI. Federal agencies should use these requirements when establishing contracts and agreements with nonfederal entities that process, store, or transmit CUI.
This dashboard aligns with the Configuration Management family of security requirements in NIST SP 800-171 (section 3.4). These requirements focus on establishing and maintaining inventories and the secure baseline configurations of information systems. Using this dashboard, an organization will be better able to monitor network system hardening practices and security policy enforcement. Several components within this dashboard display inventory and change information, in order to assist in inventory and change control processes. Additional components present compliance concerns, in order to assist in identifying misconfigurations and weak settings on internal hosts. This information will assist the organization in managing and securing the configurations of their information systems that process, store, or transmit CUI. Analysts can use this dashboard to easily drill down into the data presented and gain more detailed information. If necessary, assets or subnet filters can be used to narrow the focus of this dashboard to only those systems that process, store, or transmit CUI.
This dashboard is available in the Tenable Security Center Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The dashboard can be easily located in the Security Center Feed under the category Compliance & Configuration Assessment. The dashboard requirements are:
- Security Center 5.4.0
- Nessus 8.4.0
- Compliance data
Tenable Security Center is the market-defining continuous network monitoring solution, and can assist an organization in securing information systems.Security Center is continuously updated with information about advanced threats, zero-day vulnerabilities, and new regulatory compliance data. Active scanning periodically examines systems to find vulnerabilities, and can also make use of audit files to assess compliance. Passive listening provides real-time monitoring to collect information about systems and vulnerabilities. Host data and data from other security devices is analyzed to monitor policy and configuration settings activity. Security Center provides an organization with the most comprehensive view of the network and the intelligence needed to secure systems and safeguard sensitive information.
The following components are included in this dashboard:
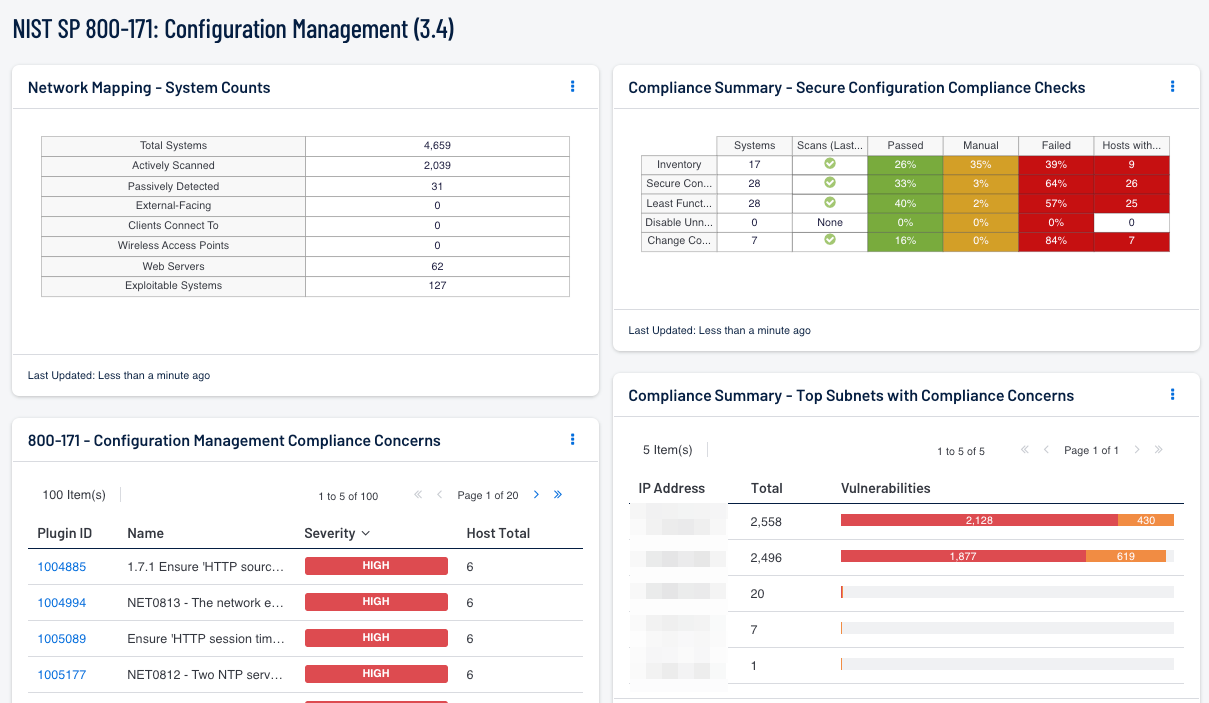
- Network Mapping - System Counts: This component presents the counts of systems detected on the network in various categories. The total number of systems is displayed, along with the counts of actively scanned systems detected by Nessus and passively detected systems discovered by NNM. For these, percentages of the total system count are displayed. The percentage bar color reflects coverage and will be red for a low percentage of total systems, yellow for a medium percentage, and green for a high percentage. In addition, counts of external-facing systems, systems that clients connect to (servers), admin systems, wireless access points, and web servers are also displayed. For each of these, percentages of the total system count are displayed with black bars. Finally, the count of exploitable systems on the network is displayed, along with a percentage bar displayed in red. Using this matrix, organizations will be able to gain a more complete picture of existing assets and high-valued systems on the network. Clicking on a highlighted indicator will bring up the analysis screen to display the specific systems and allow further investigation.
- Compliance Summary - Top Subnets with Compliance Concerns: This table presents the top Class C subnets with the most compliance concerns. High severity indicates compliance failures, and medium severity indicates compliance advisories or checks that must be performed manually. The table is ordered so the subnet with the most compliance concerns is at the top. This information will help an analyst to identify which subnet needs the most attention in terms of compliance.
- Compliance Summary - Secure Configuration Compliance Checks: This component presents the results of compliance audits to verify the secure configuration of systems, including least functionality, disabling unnecessary services, and change control. Each row includes the system count, whether scans were performed in the last 7 days, and the percentage of checks that passed, failed, or require manual verification. Passed checks are displayed in green, failed checks are in red, and checks that require manual verification are in orange. Clicking on a highlighted indicator will bring up the vulnerability analysis screen to display details on the compliance checks and allow further investigation. In the vulnerability analysis screen, setting the tool to IP Summary will display the systems on which the compliance checks are present. Setting the tool to Vulnerability Detail List will display the full details on each compliance check, possibly including further information such as the expected and actual policy values and the specific sections of the various standards to which the compliance check relates.
- 800-171 - Configuration Management Compliance Concerns: This table presents the top compliance concerns that specifically reference the NIST SP 800-171 Configuration Management family of requirements (section 3.4). High severity indicates compliance failures, and medium severity indicates compliance advisories or checks that must be performed manually. Each compliance concern also displays the number of hosts that the concern is found on. This information will help an analyst to determine the top NIST SP 800-171 configuration management compliance concerns that need to be address.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success