Vulnerabilities are present in all organizations, but each organization addresses risk in a different manner. Threats exist in user productivity software, hardware devices, and many other devices that are frequently used by the organization. Without having a clear and continuous view of existing vulnerabilities, organizations will struggle to identify and respond to threats in a timely manner. Information presented within this dashboard will provide organizations with the actionable intelligence needed to improve overall security posture and protect critical assets.
The Communications Security Establishment Canada (CSEC) developed a series of guidelines for security practitioners in managing information technology (IT) security risks for Government of Canada (GC) information systems. The ITSG-33, IT Security Risk Management: A Lifecycle Approach provides a comprehensive set of security controls that are used to support a wide variety of business requirements. To support interoperability needs, the ITSG-33 guide is consistent with controls published in the U.S. National Institute of Standards and Technology (NIST) Special Publication 800-53. Data presented within this dashboard aligns with ITSG-33 security controls that support vulnerability management, risk assessment, and risk remediation efforts. This dashboard aligns with the following controls:
- Flaw Remediation (SI-2)
- Risk Assessment (RA-3)
- Vulnerability Scanning (RA-5)
There are many vendors with patch management solutions that can manage and deploy patches to specific kinds of systems and/or software in the environment. Modern organizations have a variety of software that needs to be patched on a regular basis. For example, the organization may use Microsoft Office on Microsoft Windows and deploy their websites on Apache web servers running on virtual Linux systems. To maintain all of those systems, organizations may use multiple patch management solutions to ensure that vulnerabilities across all software products are kept up to date.
Analysts need a way to ensure that patch management solutions are providing consistent and reliable information about patched systems. Although this will address some operating system or security-based vulnerabilities, many of these solutions do not address other vulnerabilities present within the network. The information from patch management solutions and Tenable's Security Center will help to close this gap in providing information on vulnerabilities that may have been missed by these solutions.
The components in this dashboard cover vulnerability data reported from patch management solutions. Tenable supports a variety of patch management solutions, including Microsoft System Center Configuration Manager (SCCM), Windows Server Update Services (WSUS), Dell KACE, IBM BigFix, and Symantec Altiris. When Security Center correlates all of the information, analysts can see where vulnerability remediation efforts can best pay off for the organization such as identifying specific vulnerabilities posing the greatest risk. When comparing two critical vulnerabilities, it may not always be clear which vulnerability should be remediated first. While both critical vulnerabilities need to be addressed, this dashboard provides clear information about all vulnerabilities in the environment. Having the best information to confidently address which vulnerabilities are exploitable and what hosts are the most vulnerable will quickly assist the analyst to secure the organization.
This dashboard is available in the Security Center Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The dashboard can be easily located in the Security Center Feed under the category Compliance & Configuration Assessment. The dashboard requirements are:
- Security Center 5.4.2
- Nessus 8.5.1
- NNM 5.9.0
- complianceData
Tenable's Security Center is the market-defining continuous network monitoring solution, and assists in securing an organization’s internal network. Security Center is continuously updated with information about advanced threats, zero-day vulnerabilities, and new regulatory compliance data such as ITSG-33. Active scanning periodically examines systems to detect vulnerabilities within operating systems, software applications, and hardware. Agent scanning enables scanning and detection of vulnerabilities on transient and isolated devices. Passive listening provides real-time discovery of vulnerabilities on operating systems, protocols, network services, wireless devices, web applications, and critical infrastructure. Host data and data from other security products is analyzed to monitor activity from patch management solutions and services. Security Center provides an organization with the most comprehensive view of the network and the intelligence needed to fully understand the impact of vulnerabilities on the network.
The components in this dashboard include:
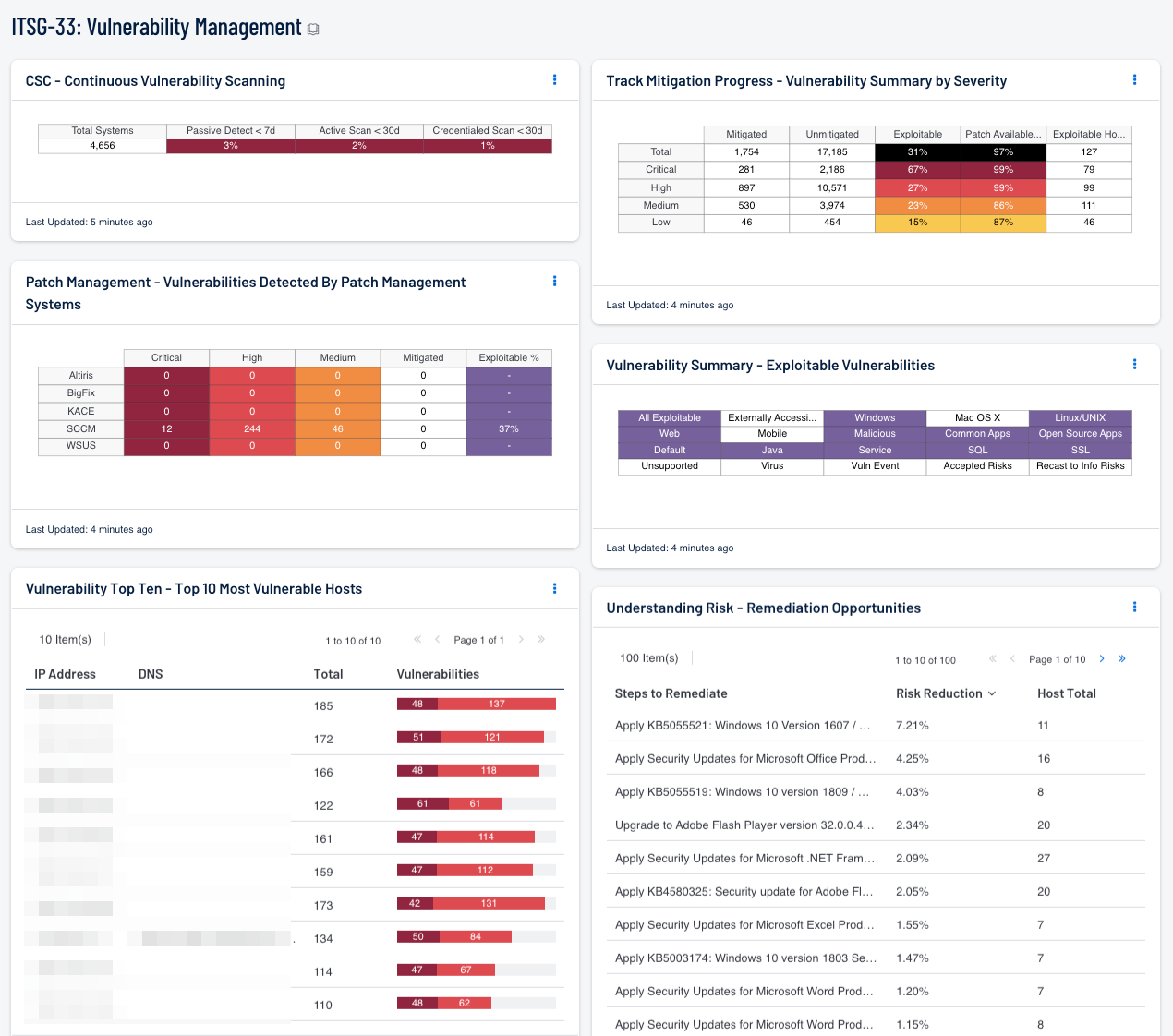
- Vulnerability Top Ten - Top 10 Most Vulnerable Hosts: This component shows the top ten hosts with exploitable vulnerabilities of high or critical severity
- CSC - Continuous Vulnerability Scanning: This matrix assists in monitoring the vulnerability detection and scanning performed by the Tenable Nessus Network Monitor (NNM) and Tenable Nessus
- Patch Management - Vulnerabilities Detected By Patch Management Systems: This matrix presents an overview of detected vulnerabilities reported by patch management systems
- Understanding Risk - Remediation Opportunities: This table displays the top remediations for the network
- Track Mitigation Progress - Vulnerability Summary by Severity: This component assists in tracking vulnerability mitigations
- Vulnerability Summary - Exploitable Vulnerabilities: This matrix displays warning indicators for exploitable vulnerabilities actively and passively detected on the network, including vulnerabilities by OS, web vulnerabilities, application vulnerabilities, and vulnerabilities by keywords such as "Java" and "unsupported"
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success