by Cesar Navas
With the growing number of threats against network infrastructures, many organizations still do not have an adequate patch management system in place. This can leave critical systems unpatched and vulnerable for a significant period of time. Particularly, the next patch cycle, or till a manual patch is applied. The ISO/IEC27000 Vulnerability Management dashboard provides security teams information on outstanding vulnerabilities, mitigation progress, and opportunities to reduce risk.
The ISO/IEC 27002:2013 framework is a global security standard that provides best practice solutions in support of the controls found in Annex A of ISO/IEC 27001:2013. The framework establishes guidelines and general principles for initiating, implementing, maintaining, and improving Information Security Management Systems (ISMS). Each security control and objective provided within the standard can be tailored to specific business and regulatory objectives, and assist with maintaining overall compliance. This dashboard focuses on the ISO/IEC 27002 12.6.1 control, which can be used to strengthen an organization’s vulnerability and patch management procedures.
Traditional vulnerability scanning tools provide a large amount of information that can make it difficult to assess and prioritize risk. Vulnerability scans provide a snapshot of a system’s security status. A long period of time between vulnerability scans can provide opportunities for attackers to gain access to an organization’s network. An organization first needs to have a comprehensive asset management program in place in order to identify existing devices on the network. The ISO/IEC 27000: Asset Management dashboard will provide information on existing hardware devices and software applications in use on a network. Having an accurate, and up-to-date view of network assets will provide the foundation security teams need to detect, respond, and remediate vulnerabilities quickly and effectively. Security teams should identify any security issues to the organization, and test patches to ensure that business operations and systems are not impacted. Testing and verifying patches will help to standardize and ensure that systems can be patched in a timely and efficient manner. Performing continuous vulnerability scans will assist organizations in making faster, and more informed risk decisions, and will help to reduce potential exposure to threats.
This dashboard assists organizations in detecting critical severity vulnerabilities, exploitable vulnerabilities, remediation progress, and vulnerability related events. Several components provide information on outstanding vulnerabilities, which security teams can use to target remediation efforts. Indicators will detect exploitable vulnerabilities from common applications, web servers, cloud services, and more. The information provided within this dashboard will help organizations stay up to date with the latest vulnerabilities, but will also aid in reducing windows of opportunity an attacker may have to gain access to network resources.
The dashboard and its components are available in the Security Center Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The dashboard can be easily located in the Security Center Feed under the category Compliance & Configuration Assessment. The dashboard requirements are:
- Security Center 5.3.1
- Nessus 8.5.1
- NNM 5.9.1
Security Center is the market-defining continuous network monitoring platform. Nessus Network Monitor (NNM) provides deep packet inspection to continuously discover and track users, applications, cloud infrastructure, trust relationships, and vulnerabilities. Nessus is continuously updated with information about advanced threats and zero-day vulnerabilities, and new types of regulatory compliance configuration audits. Security Center CV, Nessus, and NNM scales to meet future demand of monitoring virtualized systems, cloud services, and the proliferation of devices.
This dashboard contains the following components:
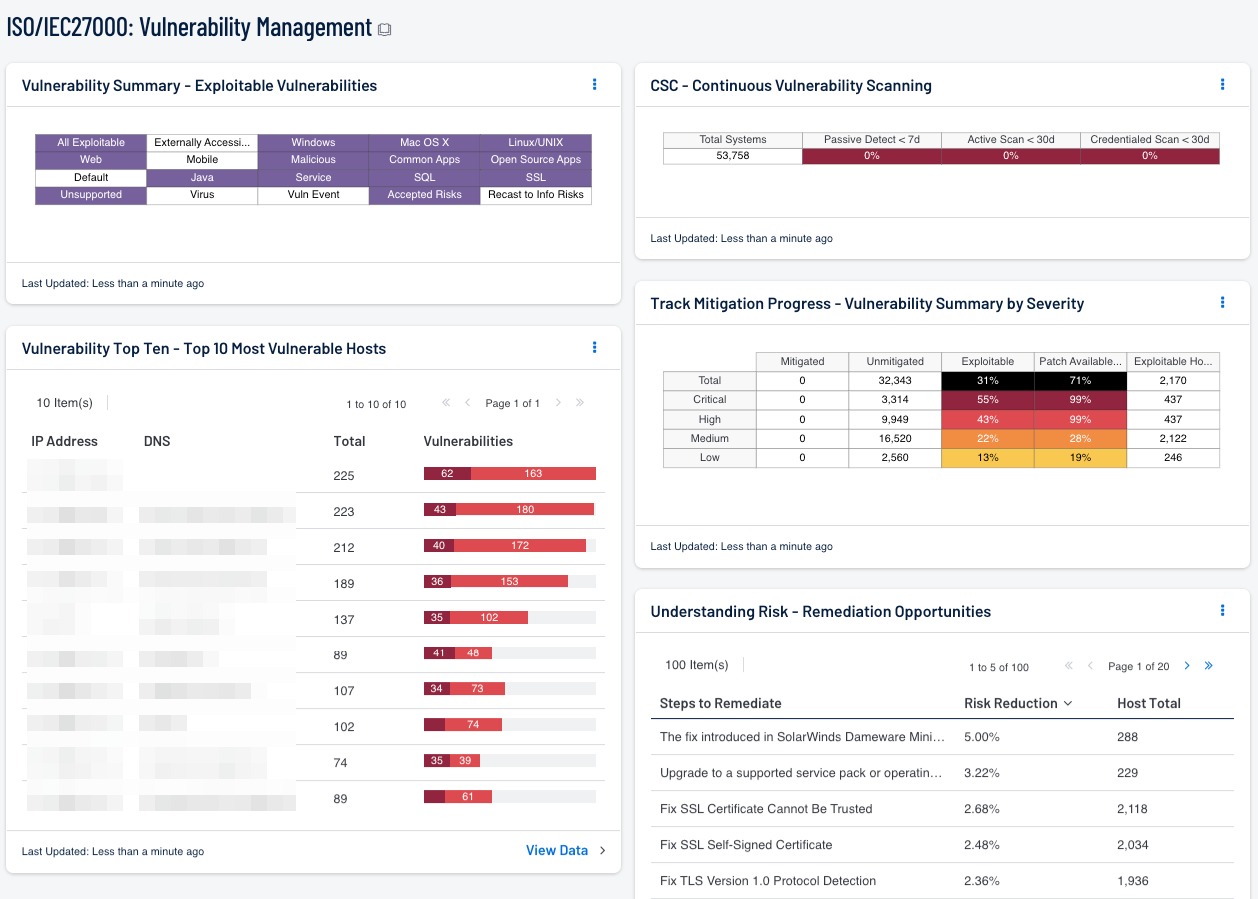
- Vulnerability Top Ten - Top 10 Most Vulnerable Hosts: This table displays the 10 hosts on the network that have the greatest number of exploitable critical and high severity vulnerabilities. The list is sorted so that the most vulnerable host is at the top of the list. For each host, a bar graph of its critical and high severity vulnerabilities are shown.
- Vulnerability Summary - Exploitable Vulnerabilities: This matrix displays warning indicators for exploitable vulnerabilities actively and passively detected on the network, including Windows vulnerabilities, web vulnerabilities, open source application vulnerabilities, and vulnerabilities by keywords such as "Java" and “unsupported”. Vulnerabilities that can be exploited by Metasploit are very dangerous and must be remediated as soon as possible. Exploitable vulnerabilities that have been marked as accepted risks or recast to Informational within Security Center are also noted. Clicking on a highlighted indicator will bring up the vulnerability analysis screen to display details for the vulnerabilities and allow further investigation. In the analysis screen, setting the tool to IP Summary will display the systems on which the vulnerabilities are present. Setting the tool to Vulnerability Details will display the full details for each vulnerability, including a description, the solution to fix the vulnerability, and in some cases, links to more information.
- Track Mitigation Progress - Vulnerability Summary By Severity: Security Center records when vulnerabilities are discovered, when patches are issued, and when vulnerabilities are mitigated. This component assists in tracking vulnerability mitigations. The matrix presents vulnerability summary information by severity. In the matrix, the row with red is critical severity vulnerability information, the row with orange is high severity, the row with yellow is medium severity, and the row with green is low severity. The Mitigated column displays the total number of mitigated vulnerabilities. The Unmitigated column displays the total number of vulnerabilities that have not yet been mitigated. The Exploitable column displays the percentage of those unmitigated vulnerabilities that are known to be exploitable. The Patch Available column displays the percentage of the unmitigated, exploitable vulnerabilities that have had a patch available for more than 30 days. Ideally, both of these percentages should be 0%, because all exploitable vulnerabilities and all vulnerabilities with patches available should have been mitigated already. The Exploitable Hosts column displays the number of hosts on the network that have unmitigated, exploitable vulnerabilities. The Common Vulnerability Scoring System (CVSS) is an open industry standard for assessing the severity of computer system security vulnerabilities; it attempts to establish a measure of how much concern a vulnerability warrants, compared to other vulnerabilities, so efforts can be prioritized. The Tenable severity levels correspond to the CVSS scores as follows: Critical severity = CVSS score 10.0, High = 9.9-7.0, Medium = 6.9-4.0, and Low = 3.9-0.0.
- CSC - Continuous Vulnerability Scanning: The Continuous Vulnerability Scanning matrix compares the total number of systems is checked against Nessus plugins to determine the percentages that have been scanned over the last 7 days. You may alter this time value if you need to extend or reduce the amount of time you would like report when systems are scanned.
- Understanding Risk - Remediation Opportunities: This table displays the top remediations for the network. For each remediation, the risk reduction for the network if the remediation is implemented is shown, along with the number of hosts affected. The table is sorted so that the highest risk reduction is at the top. Implementing the remediations will decrease the overall vulnerability of the network.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success