by Josef Weiss
A good vulnerability management program requires that an organization also know the software installed on its systems. This dashboard and its components provide information to analysts about software that is discovered on the network. According to the Center for Internet Security (CIS), Critical Security Control (CSC) Control 2 (CSC 2) is the Inventory of Authorized and Unauthorized Software.
CSC 2: Actively manage (inventory, track, and correct) all software on the network so that only authorized software is installed and can execute, and that unauthorized and unmanaged software is found and prevented from installation or execution.
Maintaining a detailed list of software used on computers in the network can be a very difficult task. However, using Tenable's Tenable Security Center, security professionals can collect information about software installed on a network using two distinct methods. The first method is active scanning with credentials. This allows the analyst to analyze each computer to collect the information about installed software. The second method is to passively monitor the network, and text software by analyzing live traffic on the network.
The dashboard and its components are available in the Security Center Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The dashboard can be easily located in the Security Center Feed under the category Discovery & Detection.
The dashboard requirements are:
- Tenable Security Center 5.0.0
- Nessus 8.6.0
- NNM 5.9.0
Tenable Security Center enables the organization to react to advanced threats, zero-day vulnerabilities, and new forms of regulatory compliance. The Tenable Nessus Network Monitor (NNM) performs deep packet inspection enabling discovery and assessment of operating systems, network devices, hypervisors, databases, tablets, phones, web servers, cloud applications, and critical infrastructure. Security Center provides a unique combination of detection, reporting, and pattern recognition utilizing industry recognized algorithms and models.
The dashboard contains the following components:
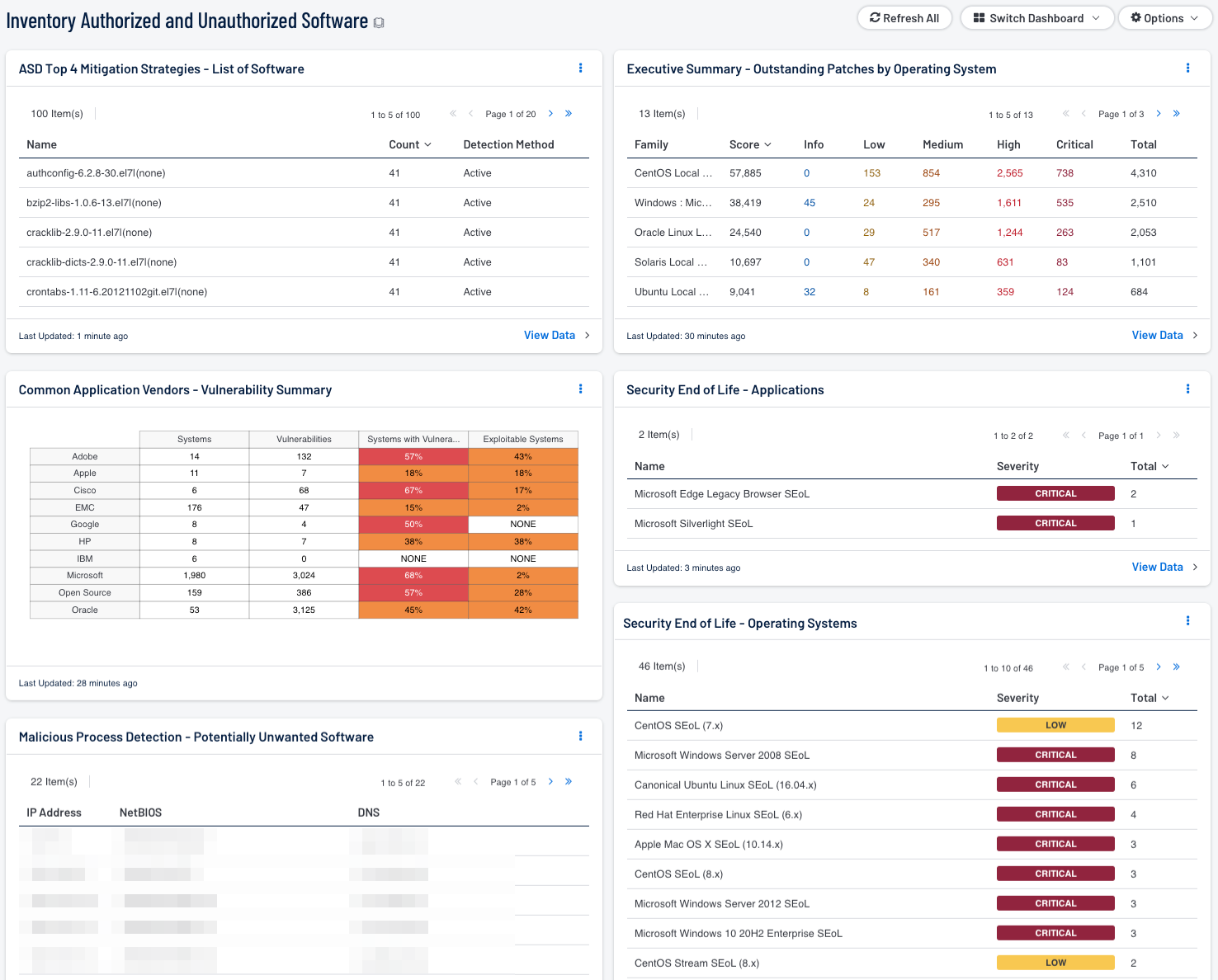
- ASD Top 4 Mitigation Strategies - List of Software - This component provides a detailed list of software currently discovered on the network.
- Common Application Vendors - Vulnerability Summary - This component displays various application vendors by row, and enumerates any found vulnerabilities across the columns.
- Executive Summary - Outstanding Patches by Operating System - The “Outstanding Patches by Operating System” component is a table with counts of vulnerabilities based on the OS local security check plugins.
- Security End of Life - Applications - The Security End of Life - Applications table displays all SEoL applications, associated severity, and is sorted by count. This component utilizes a filter containing the string 'SEoL' (Security End of Life) contained in the plugin name to identify these specific vulnerabilities along with wildcard ‘cpe:/a’ vulnerability text. These plugins can be identified by looking at the plugin name which will contain the string 'SEoL', such as 'Apache httpd SEoL (2.1.x <= x <= 2.2.x)'. SEoL is the state in the Security Maintenance Lifecycle when a product no longer receives security updates. Tenable implements a holistic approach to detecting products consistent with this definition. For more information see the SEoL KB article https://community.tenable.com/s/article/Security-End-of-Life-Plugins-FAQ.
- Security End of Life - Operating Systems - The Security End of Life - Operating Systems table displays all SEoL operating systems, associated severity, and is sorted by count. Displayed is the operating system, severity, and the total found. This component utilizes a filter containing the string 'SEoL' (Security End of Life) contained in the plugin name along with wildcard ‘cpe:/o’ vulnerability text to identify these specific vulnerabilities.
- Potentially Unwanted Software - Host Summary - This component provides a host summary table reports the counts of system, which match the plugin 59641 (Malicious Process Detection: Potentially Unwanted Software). The md5sum of one or more running process on the remote Windows host matches software known to violate some corporate policies. Verify that the remote processes are authorized in your environment.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success