Knowing what kind of vulnerabilities an organization faces requires a deep understanding of existing threats. Identifying these threats can be complicated, as network logs collect vast amounts of event data on a daily basis. The Log Correlation Engine (LCE) greatly simplifies the process of threat identification and can identify vulnerabilities present in an organization’s network by analyzing the log data. The Event Vulnerability Indicators Dashboard contains a series of components that provide an easy way to view vulnerabilities detected by LCE.
The sheer size of log data collected from network devices on a daily basis can be challenging and overwhelming. The normalization of the events performed by LCE assists in the analysis task, as it organizes and groups the data in a simplified manner. However, these events must be processed further to determine the level of risk posed by the vulnerabilities. An analyst must look at the number of and severity of the vulnerabilities present in the normalized event’s grouping to be able to determine the risk present. Tracking these vulnerabilities can be challenging, and analysts can easily lose track of what assets are at risk.
LCE examines log event data for software versions and related vulnerabilities related. In addition, LCE performs daily summary correlations and provides a summary of events based on each event type. The log data is gathered from various sources such as: Windows Event Logs, Linux, Unix, and application logs. Each component presented in this dashboard leverages LCE by evaluating NetFlow traffic, sniffed network sessions, connection events, and log data collected from applications. LCE collects IDS logs as well from many devices such as Check Point OPSEC, Cisco RDEP, Cisco SDEE, and Snort using syslog. Another unique feature to LCE is the ability to monitor cloud services such as Salesforce, Amazon Web Services (AWS) via CloudTrail, and Google Cloud Platform.
As LCE receives an event from a source, advanced threat detection techniques are applied so that the events can be normalized with a unique event name. These normalized events often correlate to various vulnerabilities and signify the presence of potential threats. As such, the events must be properly analyzed to determine the potential vulnerabilities discovered and level of risk posed by those vulnerabilities.
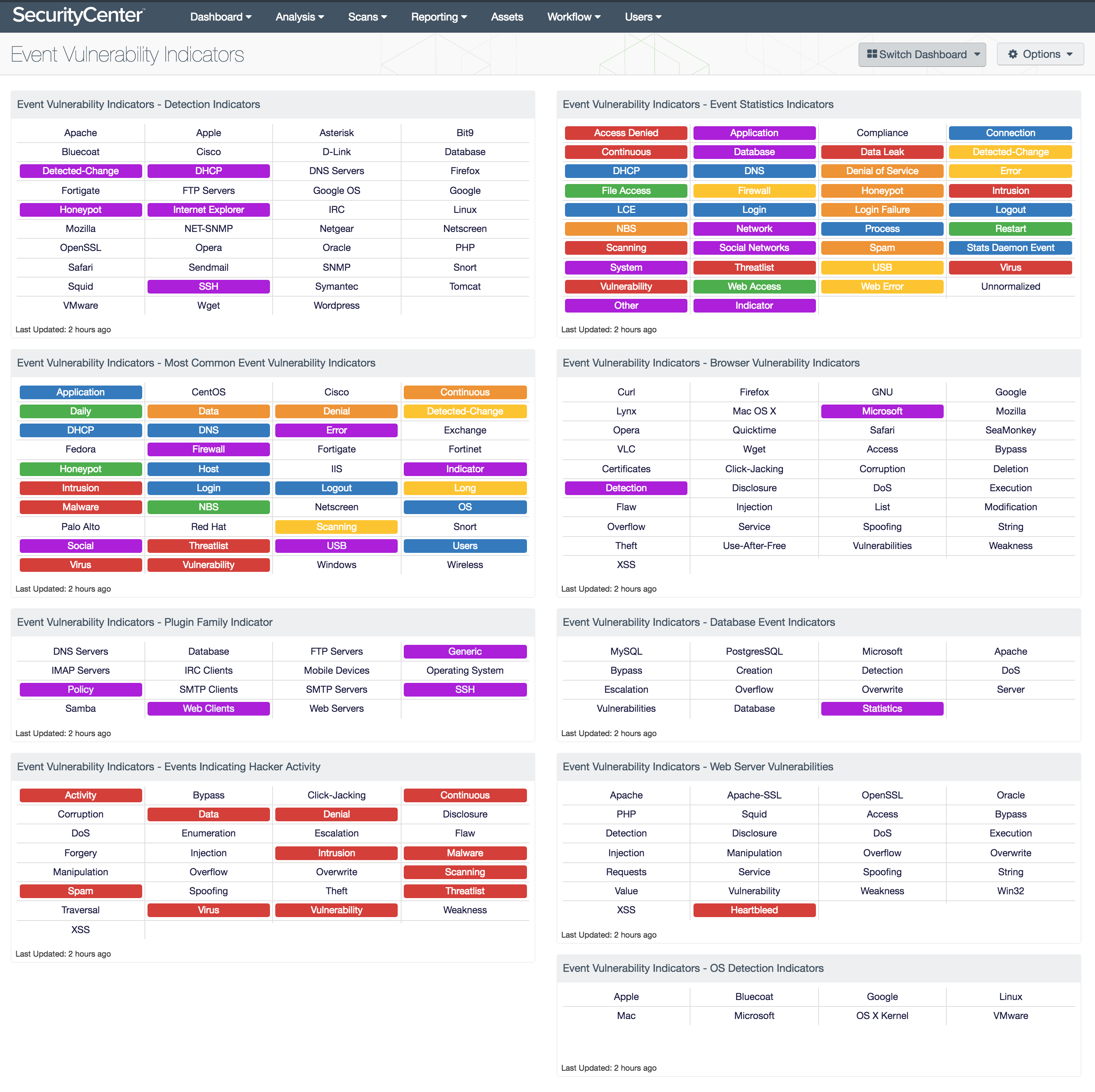
The Event Vulnerability Indicators Dashboard provides an inclusive set of indicator-style components. The components present a detailed view into the vulnerabilities identified by LCE in a clear and concise manner. For each individual event, the components use specialized filters to determine whether or not a vulnerability is present. The presence and severity level of the event vulnerability is indicated by the color shown in each of the matrices. By using different color schemes, the analyst is able to quickly identify risk associated with each vulnerability collected from normalized events.
The dashboard and its components are available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards and assets. The dashboard can be easily located in the SecurityCenter Feed under the category Threat Detection & Vulnerability Assessments. The dashboard requirements are:
- SecurityCenter 5.4.1
- LCE 4.8.1
Tenable Network Security transforms security technology for the business needs of tomorrow through comprehensive solutions that provide continuous visibility and critical context, enabling decisive actions to protect the organization. SecurityCenter is continuously updated with information about advanced threats and zero-day vulnerabilities, and new types of regulatory compliance configuration audit files. LCE performs deep log analysis and correlation to continuously discover and track systems, applications, cloud infrastructure, trust relationships, and vulnerabilities. With the information provided by LCE, SecurityCenter CV enables extensive vulnerability and malware detection, data flow analysis, user and anomalous behavior monitoring, intrusion detection, and change management monitoring.
The following components are included in this dashboard:
- Event Vulnerability Indicators - Detection Indicators: This matrix provides a quick look at what software and hardware has been detected using event vulnerabilities.
- Event Vulnerability Indicators - Most Common Event Vulnerability Indicators: This matrix takes the most common keywords found in the event vulnerabilities and correlates the events to provide an easy way to navigate the many of the vulnerabilities discovered by LCE.
- Event Vulnerability Indicators - Plugin Family Indicator: This component displays indicators of event vulnerabilities identified by the plugin family.
- Event Vulnerability Indicators - Events Indicating Hacker Activity: This matrix presents vulnerabilities that are easily exploited or indicate activities commonly attributed to hackers.
- Event Vulnerability Indicators - Event Statistics Indicators: This component provides an easy method to access all the statistics collected by LCE and reported to SecurityCenter.
- Event Vulnerability Indicators - Browser Vulnerability Indicators: This matrix displays all the common keywords for the Web Clients plugin family and the event plugin type.
- Event Vulnerability Indicators - Database Event Indicators: This matrix displays all the common keywords for the Database plugin family and the event plugin type.
- Event Vulnerability Indicators - Web Server Vulnerabilities: This component displays common keywords found within the Web Server plugin family and the event plugin type.
- Event Vulnerability Indicators - OS Detection Indicators: This matrix displays all operating systems detected by the event plugin type.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success