by Ron Gula
Monitoring the status of Windows credentialed scanning is important in supporting both patch and compliance auditing of Windows systems. Tenable.sc CV has the ability to perform credentialed scans on Windows, thus increasing the accuracy of the collected data. This dashboard monitors the results of Windows credentialed scans.
The dashboard and its components are available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The dashboard can be easily located in the Tenable.sc Feed under the category Monitoring.
The dashboard requirements are:
- Tenable.sc 4.8.2
- Nessus 8.4.0
- NNM 5.9.0
Determining the Window systems that failed authentication is important during the initial roll out of Windows credentialed scans. When a system fails a credentialed scan, patch and compliance auditing will be incomplete or possibly inaccurate. Just as important is the continuous analysis of the scans results as changes to networks and hosts could affect the risk exposure of an organization.
All components do not attempt to filter by hosts that are used during Windows credentialed scans. The asset filter can be modified to only display Windows systems discovered during active and passive scanning. Further information can be found at Using Assets with Dashboards How-To Guide.
The dashboard consists of six components covering network and host resources required to perform a successful patch and/or compliance audit while leveraging the appropriate Windows account. The six components leverage the following plugins, which must be enabled during a credentialed scan:
- 11011 Microsoft Windows SMB Service Detection
- 24269 Windows Management Instrumentation (WMI) Available
- 19506 Nessus Scan Information
- 11936 OS Identification
- 20811 Microsoft Windows Installed Software Enumeration (credentialed check)
- 10400 Microsoft Windows SMB Registry Remotely Accessible
- 10902 Microsoft Windows 'Administrators' Group User List
- 10396 Microsoft Windows SMB Shares Access
- 21745 Authentication Failure - Local Checks Not Run
Tenable.sc Continuous View provides continuous network monitoring, identifies vulnerabilities, helps reduce risk, and monitors for compliance. The Log Correlation Engine (LCE) performs deep log analysis and correlation to continuously discover and track users, applications, cloud infrastructure, trust relationships, and vulnerabilities.
Components
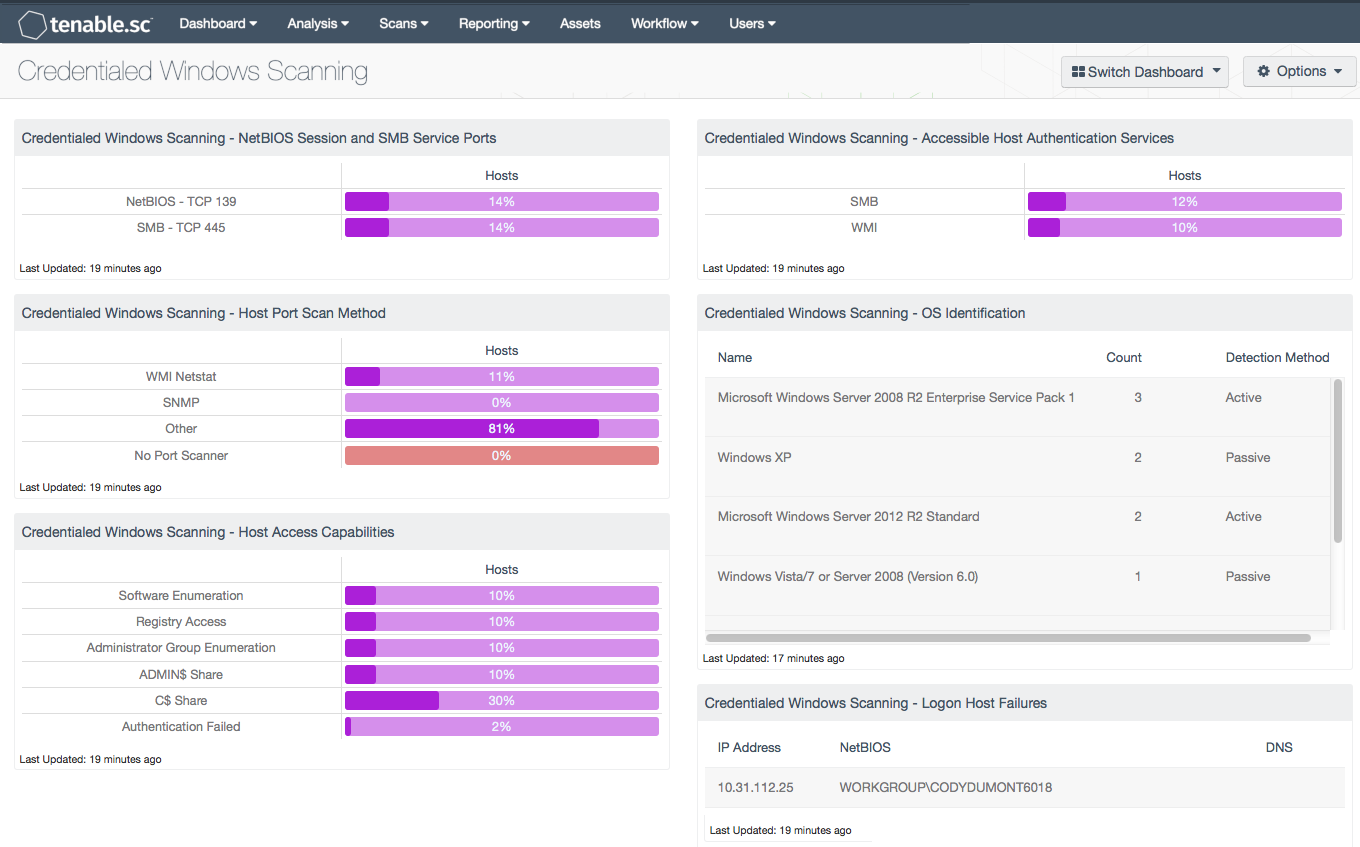
Monitoring Windows - NetBIOS Session and SMB Service Ports: This matrix component indicates the percentage of hosts whose TCP port 139 (NetBIOS) and TCP port 445 (SMB) are found open by a Nessus scanner. For a credentialed scan to work, both ports must be open and accessible to a Nessus server over a network. The Server Message Block (SMB) protocol is a network sharing protocol for Windows systems. SMB provides an authenticated mechanism for Windows systems. Nessus will attempt to use SMB to authenticate with Windows systems but might need to use NetBIOS on older Windows systems. The NetBIOS Session and SMB Service Ports component does not attempt to filter by those hosts that are only using Windows credentialed scans. Modifying the components to filter by an asset list can resolve to only displaying Windows credentialed scans. When adding an asset filter to this component, the asset filter must be added to both the base query and the query filter. This will provide a more accurate display percentage within this component.
Monitoring Windows - Accessible Host Authentication Services: This matrix component highlights the percentage of hosts whose SMB and WMI services, which are necessary for patch and compliance auditing are available to a Nessus server.
Monitoring Windows - Host Port Scan Method: This component displays indicators for different types of successful Nessus scanning methods by host percentages. Many Tenable customers are leveraging the WMI Netstat scanner to considerably speed up, and in some cases improve, port scan accuracy while performing patch and configuration auditing. If a WMI Netstat port scanner cannot be leveraged, then either no port scanner will be used or another port scanner will be used as a fallback choice.
Monitoring Windows - OS Identification: This table component displays the various Windows platforms being audited with a credentialed scan. This table is sorted by OS count and displays the OS version, count, and detection method. This information is useful to an analyst who needs to know the numerous Windows platforms that are being scanned in the network environment. The OS Identification component filters using passive and active plugins to locate all systems running Microsoft Windows. The OS Identification plugins use several techniques to identify the OS, with differing levels of confidence. This component uses the vulnerability text string “windows” in conjunction with plugin IDs.
Monitoring Windows - Host Access Capabilities: When a Nessus server logs on to a Windows host, there are many factors that can still block a successful patch and/or compliance audit. The "Host access capabilities" matrix component measures the success of accessing various host resources required by a host login session. If the resources are available, then the Nessus scanner will be able to enumerate software, access the registry, enumerate the administrators group, and access the C$ and ADMIN$ shares. If the login fails or the login session does not provide the necessary resources, then authentication will fail, highlighted as a percentage over the hosts audited in the final bar in the component. The authentication failure status is provided by plugin 21745 reporting a problem.
Monitoring Windows - Logon Host Failures: This table displays the Windows systems that failed login for credentialed scans. If the resources are available, then the Nessus server will be able to enumerate software, access the registry, enumerate the administrators group, and access the C$ and ADMIN$ shares. If the login fails or the login session does not provide the necessary resources, then authentication will fail. The authentication failure status is provided by plugin 21745 reporting a problem.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success