Detecting and monitoring the vulnerability of mobile devices on a network is a constantly growing challenge. There is an increasing acceptance of employees bringing their personal mobile devices into the office, which poses a challenge for security teams. Personal mobile devices are not often managed by Mobile Device Management (MDM) solutions or held to the security standards required by the company. Detecting and assessing the vulnerabilities associated with unmanaged devices is a key priority in securing a network. By leveraging the capabilities of the Passive Vulnerability Scanner (PVS), organizations can use SecurityCenter to more effectively monitor the unmanaged mobile devices connecting to their network.
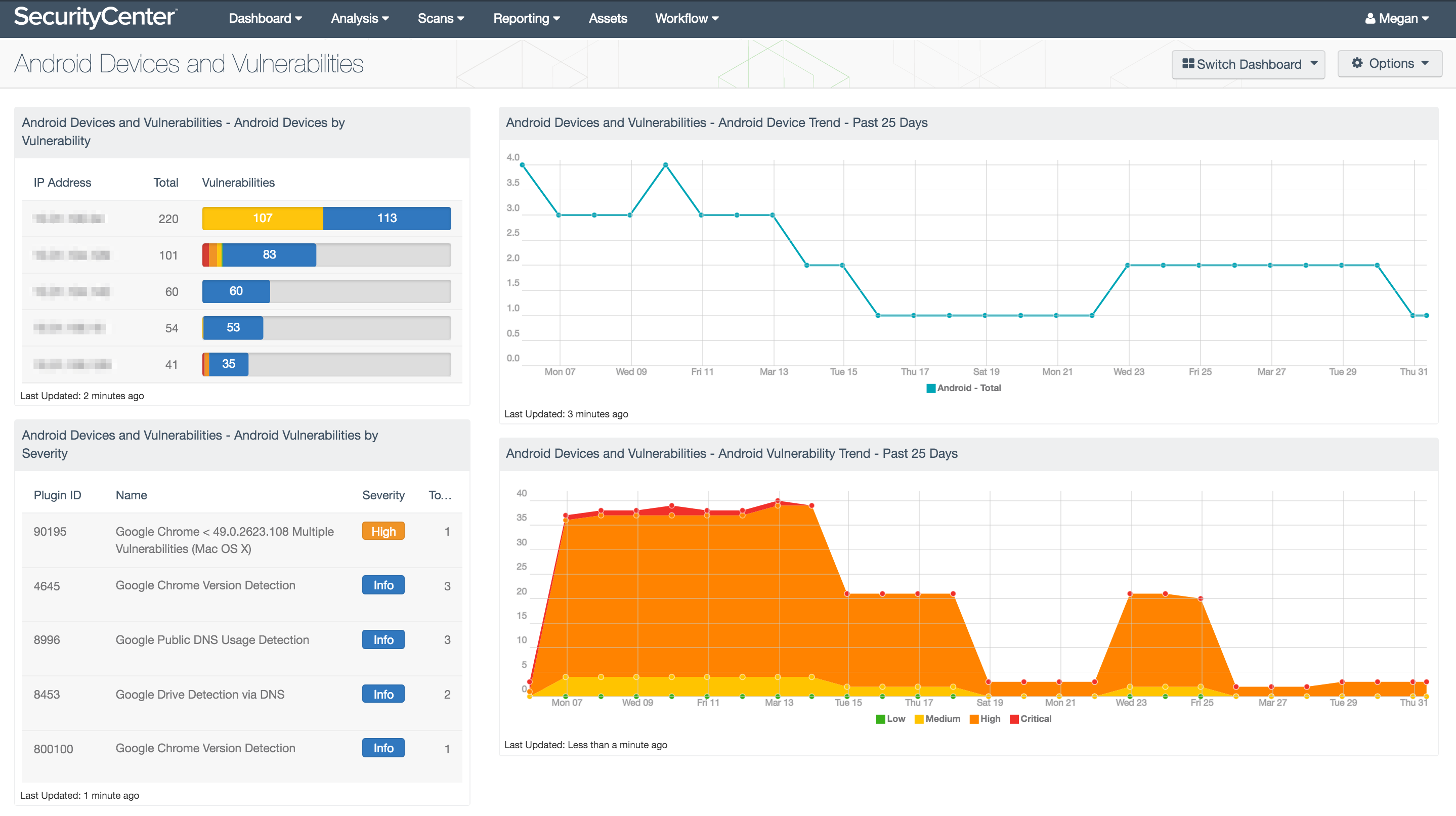
The Android Devices and Vulnerabilities dashboard assists security teams in understanding the Android devices connected to their network and the associated vulnerabilities. Devices are detected by the PVS and identified by vulnerability text. Detections are filtered by vulnerability text and time in order to provide the most accurate information about Android devices on the network. This dashboard provides focus on the prevalence and vulnerabilities associated with one of the world’s most widely distributed mobile operating systems.
The components in this dashboard provide several views of the Android devices connected to the network to help security teams identify relevant vulnerabilities and security measures. Tables are focused on the past seven days of data in order to reflect the most current information gathered by PVS. Trend charts reflect trend data over the past 25 days to help security teams track the connections and severities of vulnerabilities detected on the network. Together, the components in this dashboard provide a platform from which security teams can detect and identify the Android devices connected to their network and the associated vulnerabilities.
The dashboard and its components are available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The dashboard can be easily located in the SecurityCenter Feed under the category Threat Detection & Vulnerability Assessments.
The dashboard requirements are:
- SecurityCenter 4.8.2
- PVS 4.4.0
- This dashboard requires “Full Text Search” to be enabled for each analyzed repository.
SecurityCenter Continuous View (CV) provides continuous network monitoring, vulnerability identification, risk reduction, and compliance monitoring. The Passive Vulnerability Scanner (PVS) performs deep packet inspection to enable discovery and assessment of operating systems, network devices, hypervisors, databases, tablets, phones, web servers, cloud applications, and critical infrastructure. By integrating with PVS, SecurityCenter CV’s continuous network monitoring is able to detect devices, systems, applications, software, and events across the enterprise.
This dashboard contains the following components:
- Android Devices by Vulnerability: This table lists the Android devices observed on the network in the past seven days in order of vulnerability status.
- Android Vulnerabilities by Severity: This table lists the vulnerabilities detected on Android devices connected to the network in the past seven days.
- Android Device Trend – Past 25 Days: This line chart shows the counts of Android devices connected to the network each day over the past 25 days.
- Android Vulnerability Trend – Past 25 Days: This area chart illustrates the trend of Android-specific vulnerability detections on the network each day over the past 25 days.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success