by Cody Dumont
The proliferation of unsupported and end-of-life software is an issue for many organizations and increases the effort required to minimize risk. As software reaches their end-of-life (EOL), vendors often stop providing updates and support for the older versions. This report provides system administrators with a summary of the software that is no longer supported and puts the organization at the most risk.
Nessus is one of the most widely deployed security technologies and is the gold standard for vulnerability assessment. As the industry leader in vulnerability detection and the primary sensor for implementing an effective Vulnerability Management program, Nessus detects software that puts the organization at the most risk. Nessus uses several techniques to enumerate software, from registry scanning on Windows and using Command Line Interface (CLI) package managers (for example rpm). The discovered applications are then checked against known vulnerability registries, for example Common Vulnerabilities and Exposures (CVE®) or Information Assurance Vulnerability Management (IAVM), to establish severity levels. The data is then compiled into this easy to read and understand report which highlights the top 25 unsupported software applications, then provides a list of hosts where the software was found.
Tenable pioneered Cyber Exposure, a new discipline that helps organizations manage and measure their cyber risk across traditional and non-traditional assets. Nessus provides the key risk metrics that businesses need to measure risk exposures. Nessus enables the organization to better identify and track the risk associated with the unsupported software identified by this report. Security Directors and Risk Managers are able to use this report to start risk mitigation initiatives and establish a new level of dialogue with the business owners.
Chapters
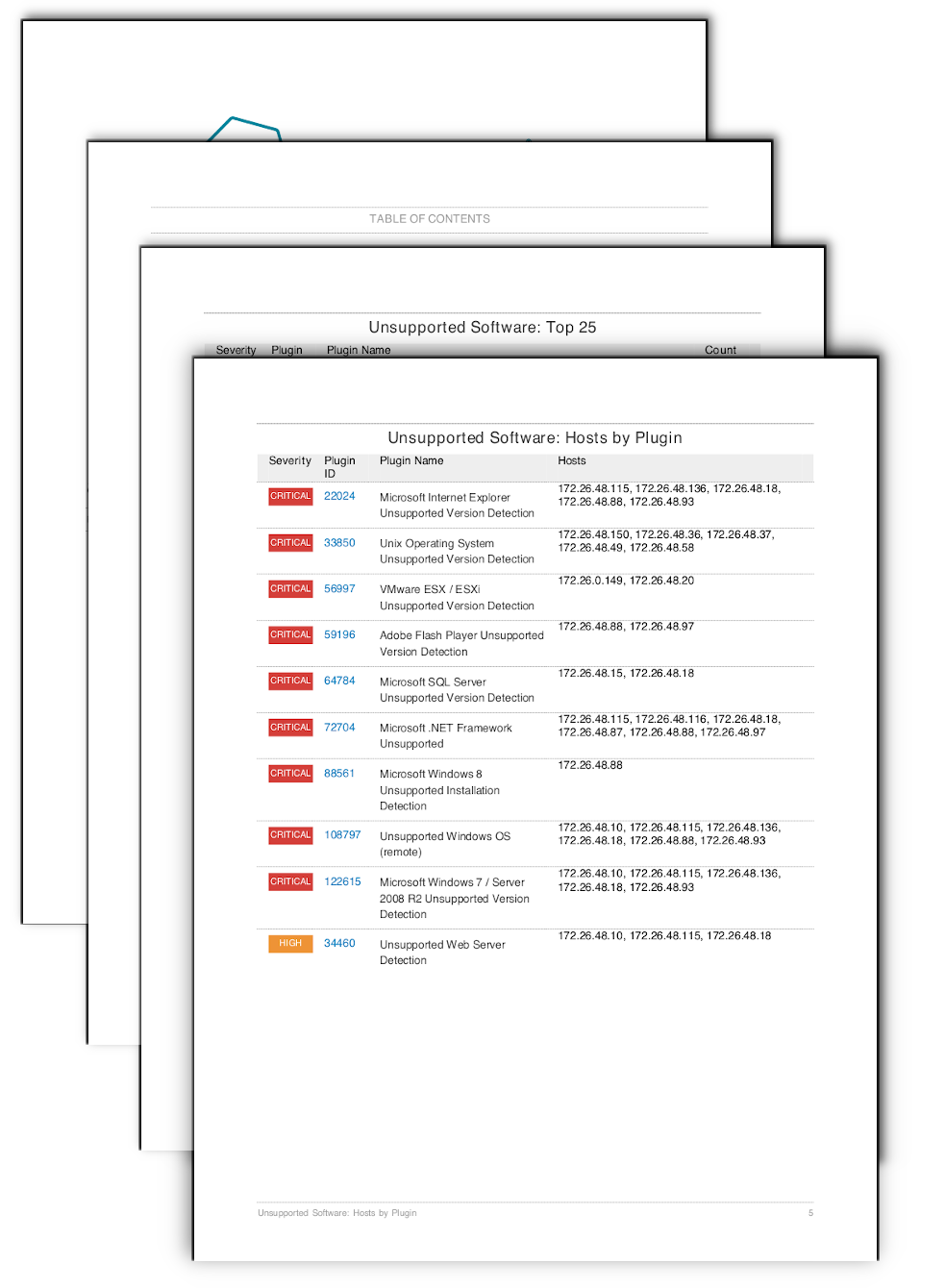
The Unsupported Software: Top 25 table uses the keyword “unsupported” in the plugin name to identify software that is no longer supported by the vendors. The data is then sorted using the count, the number of hosts where the plugin was found. While some plugins may be present more than one time on a single host, for the most part a plugin will only be present once on each host. The unsupported software identified by this report exposes the organization to risk, as the software is no longer maintained by the vendor and therefore the risk cannot be mitigated. These vulnerabilities should be prioritized and the software removed or updated to a supported version as soon as possible.
The Unsupported Software: Hosts by Plugin table provide the IT operations team with an action plan and the identified hosts for each vulnerability. The IT managers are able to use this information in planning new software deployment plan and work with the information security team in risk mitigation efforts. The table uses the keyword “unsupported” and sorts the scan results by severity and plugin ID. The entries in the Hosts column are then sorted in ascending order.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success