by Cody Dumont
System administrators and the security team work together to identify systems at the most risk. A good first step is to understand the operating systems in the network. This report provides a summary of the most prevalent operating systems on the network.
The first step of Vulnerability Management is to Discover the assets in the network. Nessus is designed with a vast library of plugins that use network and computer service protocols to enumerate devices connected on the network to assist in discovery process. Once assets are discovered, Nessus conducts a vulnerability assessment to support the next step, Assess. Nessus provides a simple, easy and intuitive interface to set up the network scan and provides this report to help group assets into operating system families. To aid in the Analysis phase, Nessus identifies vulnerabilities with different severity levels. This data helps the security team in understanding the other risk to network, at the time of the scan.
Nessus uses active scanning and agent scanning to communicate with targets on the network. During the scanning process specially crafted packets are sent to targets and their response is recorded. As different systems will respond in different ways, Nessus starts by port scanning the systems and recording the open ports and services. Then each protocol or service is finger printed and the protocol with highest confidence level is selected. Next Nessus attempts to authenticate to the services allowing for a more accurate assessment of the system. While OS identification is possible without credentials, the results are far more accurate with credentials. For example, a Windows system may appear to be a Windows 7 or Window 10 computer without credentials, but with credentials Nessus is able to validate the OS version with a much higher confidence level.
Tenable built the most innovative vulnerability scanner, Nessus, which is the world's most widely deployed vulnerability assessment scanner. Powerful and flexible to adapt to the unique requirements of today's modern networks. Nessus provides visibility into a wide range of assets on many computing platforms. The data in this report provides a detailed of risks based on the operating systems and vulnerabilities combined together.
Chapters
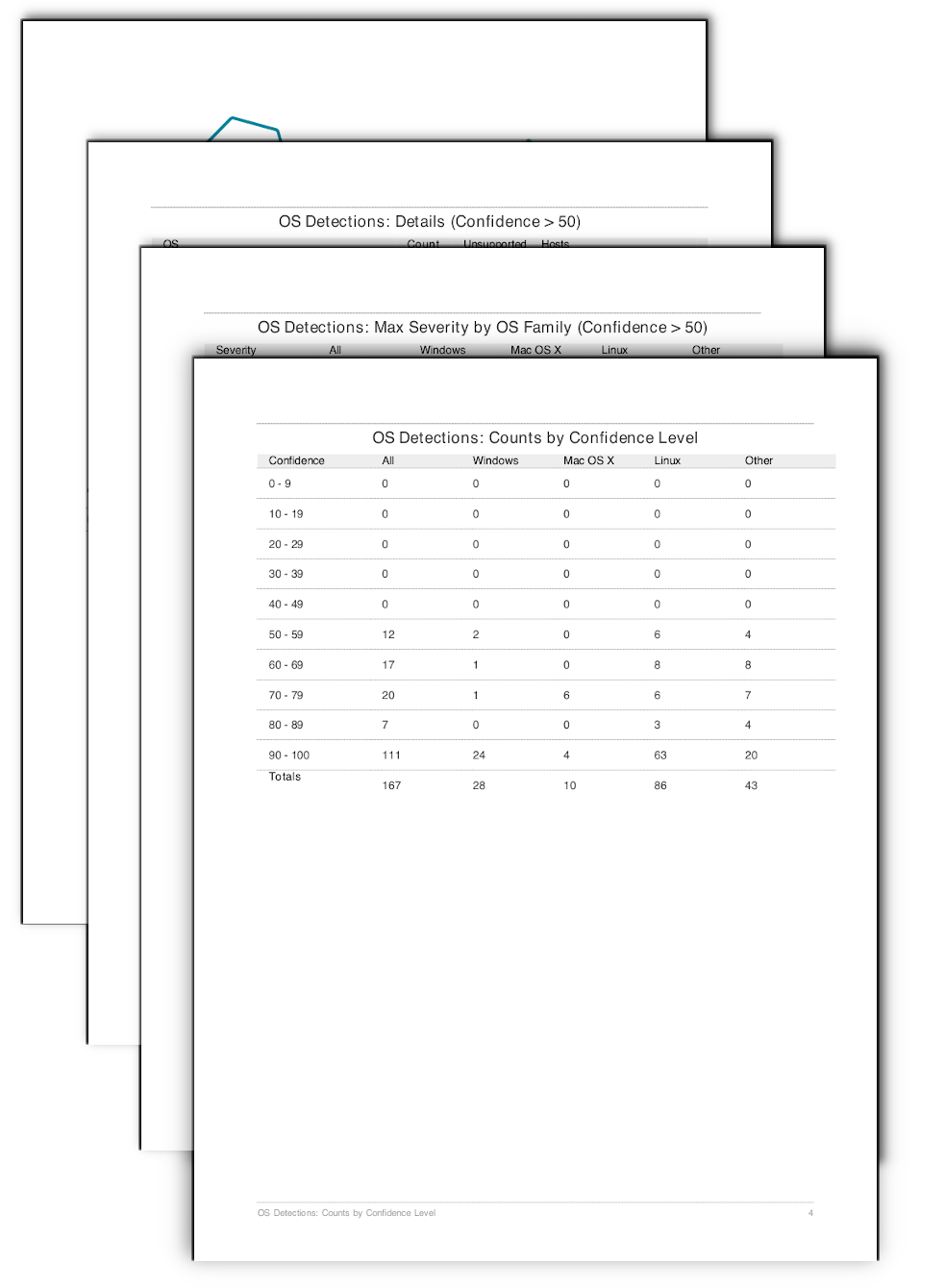
OS Detections: Counts by Confidence Level: Nessus groups the hosts into different OS families, such as "operating-system", "operating-system-unsupported", "os" and "operating-system-conf". In doing so this report organizes the system counts first using a matrix style table, that displays rows by the confidence level and then by an OS family using columns. The All column displays the total count of plugin 11936 present at the respective Confidence Level. The Windows, Mac OS X, and Linux, filter based on the key words 'windows', `mac`, or 'linux'. The Other column will match on anything that does match the aforementioned key words.
OS Detections: Max Severity by OS Family (Confidence > 50): Building upon the previous matrix, the OS Detections: Max Severity by OS Family (Confidence > 50) table provides the security team with a summary view of risk based on operating system. The counts represented in this table are based on system count by OS family and if a vulnerability with the respective severity is present. For example, if there is a count of 15 listed in the Windows column and the High severity row, there are 15 assets identified to have a Windows operating system with at least 1 high severity vulnerability.
OS Detections: Details (Confidence > 50): The OS Detections: Details (Confidence > 50) table presents all the OS family detections, along with assets within each OS. The table also displays the OS is supported by the vendor.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success