Get ahead of cyber threats with exposure management
Is fragmented visibility leaving you exposed?
Siloed security tools create fragmented visibility across your attack surface. The advanced exposure data fabric provided by Tenable Exposure Management unifies that visibility, applying technical and business context to separate noisy findings from true business exposures that can impact the organization.

Your security teams face an uphill battle, encountering three common challenges in preventing attacks:
The world's best exposure data meets generative AI for exposure management
Exposure Data Fabric
For generative AI to truly revolutionize an exposure management program, you must have access to the most exceptional vulnerability and exposure context worldwide. This wealth of information plays a vital role in guiding decisions related to preventive security. Tenable’s Exposure Data Fabric serves as the fundamental building block that drives ExposureAI.
ExposureAI
ExposureAI transforms your defense strategies by offering rapid analysis, decisive decision-making and unwavering guidance. With unmatched data and expertise from Tenable, ExposureAI empowers teams to navigate complexities, outmaneuver adversaries and embrace preventive security. Analysts master risk mitigation across the evolving attack surface, regardless of origin.
Get ahead of your cyber risks
Exposure management enables your organization to understand cyber risk so you can make more effective business decisions. Built on the foundations of risk-based vulnerability management, exposure management takes a broader view across your modern attack surface, applying both technical and business context to more precisely identify and more accurately communicate cyber risk, enabling better business decisions.
Gain comprehensive visibility across your modern attack surface
Security teams need an unconstrained view to effectively protect your organization from an attack.
Apply context to anticipate threats
Your teams need contextual intelligence to prioritize efforts based on what will prevent the most likely attacks.
Communicate cyber risk accurately at all levels of your organization
Accurately communicating risk allows stakeholders to take actions that drive business value.
Exposure management is about seeing the full, accurate picture of your attack surface and being equipped to make the right decisions to reduce your cyber risk efficiently. Learn how to stand up and mature an exposure management program.
Five essential
steps to build
your exposure
management program
Attackers don't honor silos:
Five steps to prioritize true business exposure
Download the white paper
Determine gaps in coverage or integration.
Consider all aspects of the modern attack surface and be sure to look at it from an attacker’s perspective.
Understand the business value of your assets and prioritize remediation based on risk.
Benchmark internally and externally and apply continuous improvement practices.
Develop consistent, accurate communication practices. Can you answer the question, “How secure are we?”
Key roles in an exposure management program
Security practitioners
Security practitioners need full visibility into the attack surface along with a unified view of all assets. An exposure management platform can help security practitioners prioritize efforts in remediating software vulnerabilities, misconfigurations and improperly assigned credential entitlements. Such comprehensive visibility and prioritization capabilities enable security teams to better understand their attack surface, eliminate blind spots and build a baseline for effective risk management. This empowers them to make the best decisions around what, when and how to mitigate exposures that put your organization at risk.
Get startedSecurity managers
Security managers need to focus available resources on their most pressing security needs through insight and context about threats, assets and privileges. An exposure management platform helps security managers eliminate windows of risk while reducing resources needed to remediate and respond. It enables these users to anticipate attack consequences by providing a contextual view of how assets and users are interrelated across the attack surface. It also provides security managers with clear and easily communicated key performance indicators (KPIs), yielding insights into the organization’s progress over time, as well as benchmark comparisons within your organization.
Get startedCISOs, BISOs and other security executives
CISOs, BISOs and other security executives require accurate risk assessments to improve investment decisions, make decisions about insurability, meet regulatory and compliance requirements and drive organizational improvement. An exposure management platform provides actionable metrics to help security leaders measure, compare and communicate cyber risk, not only to operations teams within IT and security, but also up and out to non-technical executives and operating teams throughout the enterprise. A unified cyber risk view with clear KPIs enables executives to measure progress over time and benchmark comparisons against industry peers and within the organization. The goal? Helping security leaders answer the question, “How secure are we?”
Get startedSecurity practitioners need full visibility into the attack surface along with a unified view of all assets. An exposure management platform can help security practitioners prioritize efforts in remediating software vulnerabilities, misconfigurations and improperly assigned credential entitlements. Such comprehensive visibility and prioritization capabilities enable security teams to better understand their attack surface, eliminate blind spots and build a baseline for effective risk management. This empowers them to make the best decisions around what, when and how to mitigate exposures that put your organization at risk.
Get startedSecurity managers need to focus available resources on their most pressing security needs through insight and context about threats, assets and privileges. An exposure management platform helps security managers eliminate windows of risk while reducing resources needed to remediate and respond. It enables these users to anticipate attack consequences by providing a contextual view of how assets and users are interrelated across the attack surface. It also provides security managers with clear and easily communicated key performance indicators (KPIs), yielding insights into the organization’s progress over time, as well as benchmark comparisons within your organization.
Get startedCISOs, BISOs and other security executives require accurate risk assessments to improve investment decisions, make decisions about insurability, meet regulatory and compliance requirements and drive organizational improvement. An exposure management platform provides actionable metrics to help security leaders measure, compare and communicate cyber risk, not only to operations teams within IT and security, but also up and out to non-technical executives and operating teams throughout the enterprise. A unified cyber risk view with clear KPIs enables executives to measure progress over time and benchmark comparisons against industry peers and within your organization. The goal? Helping security leaders answer the question, “How secure are we?”
Get startedTenable One
Security evolved
Tenable One is an exposure management platform designed to help you gain visibility across your modern attack surface, focus efforts to prevent likely attacks, and accurately communicate cyber risk to support optimal business performance. The Tenable One platform offers broad vulnerability coverage spanning IT assets, cloud resources, containers, web apps and identity systems.
Learn more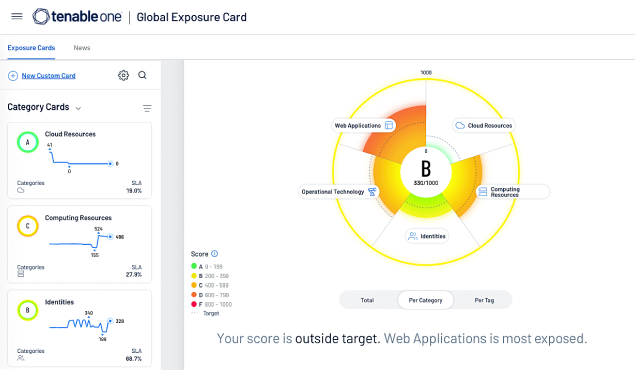
Get started with Tenable One
Tenable One has helped our engineers reduce the time spent on manual tasks by 75%, which allows them to focus on actual engineering work.
- Tenable One








