The Relationship between Vulnerability Scanning and Malware Scanning
In the early days of computing, virus and worm authors were not welcomed in the community of hacking. The hacking community thought of malware authorship as less challenging than finding a good vulnerability and compromising weak systems—unsavory, beneath them as something that was done by kids with no talent or skills. Accordingly, the security industry treated vulnerabilities and malware as two distinctly separate threats.
In 2003, Dr. Sarah Gordon presented a paper at the annual Virus Bulletin conference which broached a topic that many didn’t want to discuss: blended threats. The blended threat was a computer virus or worm that exploited one or more vulnerabilities in order to infect or replicate. When Dr. Gordon presented her paper, many in the industry thought the animosity between the malware authors (vXers, for Virus Exchanges) and the hackers would prevent that type of cooperation and coordination.
Sadly, these communities lacked the foresight to see that malware was evolving from viruses, worms, and Trojans written by hobbyists into a for-profit endeavor. As we moved further into the new millennium, those attempting to use viruses and worms to achieve their political agendas and personal goals or being first to infect were replaced by out of work programmers in the crumbling former Soviet Union and other locations, who saw that they could make a profit from adware and botnets.
Vulnerability scanners vs. malware scanners
In the early days of scanners, there were two distinct products: one type scanned for vulnerabilities and the other type scanned for malicious software. In the computer security world, anti-virus scanners morphed into desktop security suites. These suites include Intrusion Detection Systems (IDS), Intrusion Prevention Systems (IPS), sandboxing, reputation-based web checks, and the familiar virus scanner. Due to the amount of malware being detected, the virus scanner definitions were often updated multiple times a day, sometimes on an hourly basis. While this was happening, vulnerability scanners continued to develop, adding new vulnerabilities and operating system checks.
Vulnerability scanners and malware scanners each have their own intrinsic strengths and weaknesses
Each scanner has its own intrinsic strengths and weaknesses. Obviously, by default, anti-malware scanners are not vulnerability scanners and vulnerability scanners are not anti-malware scanners. Both tools can and do scan for a subset of the other. For example, many desktop security suites scan for vulnerabilities known to be exploited by malware, usually by scanning for files performing that behavior. Likewise, some vulnerability scanners find malware when looking for vulnerabilities on a system. However, neither one is comprehensive enough to be used for doing both tasks.
However, neither one is comprehensive enough to be used for doing both tasks
Malware scanners are typically deployed to every host on a network and run in a memory resident mode to capture activities happening in real-time. This is both a strength and a weakness; the strength is that there are multiple sensor points, and the weakness is that more hosts need to be updated. With all those hosts being frequently updated, there can be network bandwidth issues and other problems that can cause update failures.
Vulnerability scanners have historically been deployed to serve compliance goals. To meet those goals, they don’t have to be deployed everywhere, they don’t have to scan everything, and they don’t have to be active all the time.
While many people think building an anti-malware architecture is as simple as just installing the product on a host and pointing it to the corporate managing server, it’s much more complicated than that. Vulnerability scanning architecture and scheduling is exponentially more complex. With remote vulnerability scanners being located off the local host, they can scan hosts without having results corrupted by an infected system. Remote vulnerability scanners are often more flexible in permitting user defined inputs, making them a preferred tool for audits and specialty responses.
This should encourage all security professionals, as it reinforces the defense in depth vision. Since the two products are complimentary in nature, think of them as a fishing analogy. The professional fisherman makes a catch with nets, a simplified series of mutually supporting ropes. An amateur, however, fishes with a single line at a time, hoping to reel in a fish one at a time. The professional fisherman will always outperform the line fisherman due to the multitude of resources he utilizes. The combination of anti-malware and vulnerability scanners provides the same type of fortified support by allowing a solid defense of prevention and proactive remediation/response to intrusion.
Tenable solutions
While Tenable Network Security’s Nessus® scanner falls into the category of vulnerability scanners and SecurityCenter Continuous View™, our continuous network monitoring solution, is more akin to intrusion detection than a scanner, both have some malware detection capabilities to enhance existing counter-malware architecture.
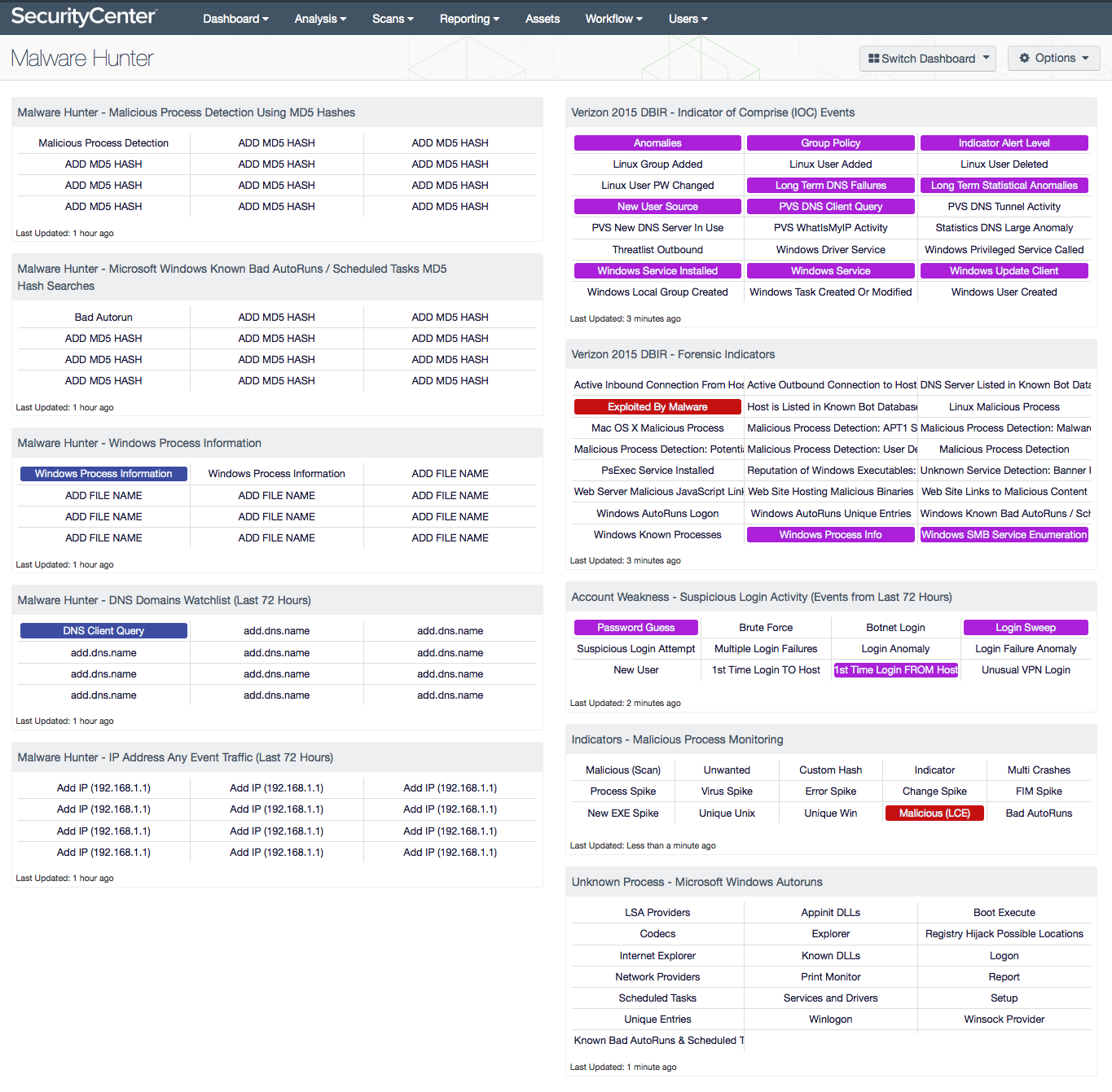
One of the most recent additions is the Malware Hunter dashboard for SecurityCenter. This dashboard is a combination of static Indicators of Compromise (IOCs) and customizable portions, enabling a corporate security team to quickly react to new or high profile malware while waiting for detections from their host security product vendor. We are proud to post discussions concerning IOCs publically, and this dashboard is a simple way of incorporating information from those discussions into practical responses.
While neither Nessus nor SecurityCenter should be considered a replacement for malware scanners, they are excellent safety nets for existing counter-malware structures.
Learn more
- Malware
- Vulnerability Scanning



Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success