Reduce Exposure Through Immediate Threat Identification and Fast Response

At Tenable, we have long been champions of continuous monitoring. Constantly collecting and interpreting data from multiple sources, including active and agent scans, network traffic, events, log data, and via integrations with other systems and applications gives you continuous visibility into what’s happening on your network as well as the critical context you need to take decisive action.
This continuous flow of security information also helps solve some very specific security challenges, including what happens when a high visibility threat or vulnerability makes the news.
High visibility threats and vulnerabilities
High visibility threats and vulnerabilities aren’t anything new. I remember back to my university days (1990s) when the Michelangelo virus was going to wipe out millions of PCs around the globe. Michelangelo turned out to be a bit of dud (thankfully) but it garnered significant attention from the mainstream media.
If we put away our ‘90s Beanie Babies and fast-forward to today, we still see high visibility threats - that hasn’t changed. However, with the internet, social media, as well as traditional media, news about these threats spreads much faster and wider. Heartbleed was one of the first vulnerabilities in recent memory to get full marketing attention; when it was announced in April 2014 with its own cool name, website and logo, word spread fast. Today, a Google search for “Heartbleed” yields 4+ million results. This mass communication means a much wider audience learns about threats faster than ever before, including your CEO.
As a security professional, do you dread seeing your CEO when the next Heartbleed makes the news? Your CEO will want to know right away whether the organization is exposed, and if so, how quickly you can respond. If you’re relying on traditional security tools, like active scanning alone, you know it will take days or weeks to get that answer, even though your CEO wants it immediately.
Immediately identify new threats and respond effectively
So how can continuously collecting and interpreting security data help when you need to immediately determine if your organization is affected by the next high visibility threat or vulnerability? Simply put, if you need an answer immediately, there’s nothing more immediate than already having the information you need.
If you need an answer immediately, there’s nothing more immediate than already having the information you need
With SecurityCenter ContinuousView™ (SecurityCenter CV™), Tenable is in a unique position to provide threat and exposure information immediately. SecurityCenter CV gets information from multiple sources, including scan data, agent data, network traffic monitoring, host activity and event monitoring, as well as through external sources like threat intelligence and connectors to other systems and applications. With all of this information, much of it collected in near real time, it becomes easy to answer critical questions like “which systems are running an affected operating system?” immediately.
Mapping out an effective response requires critical context
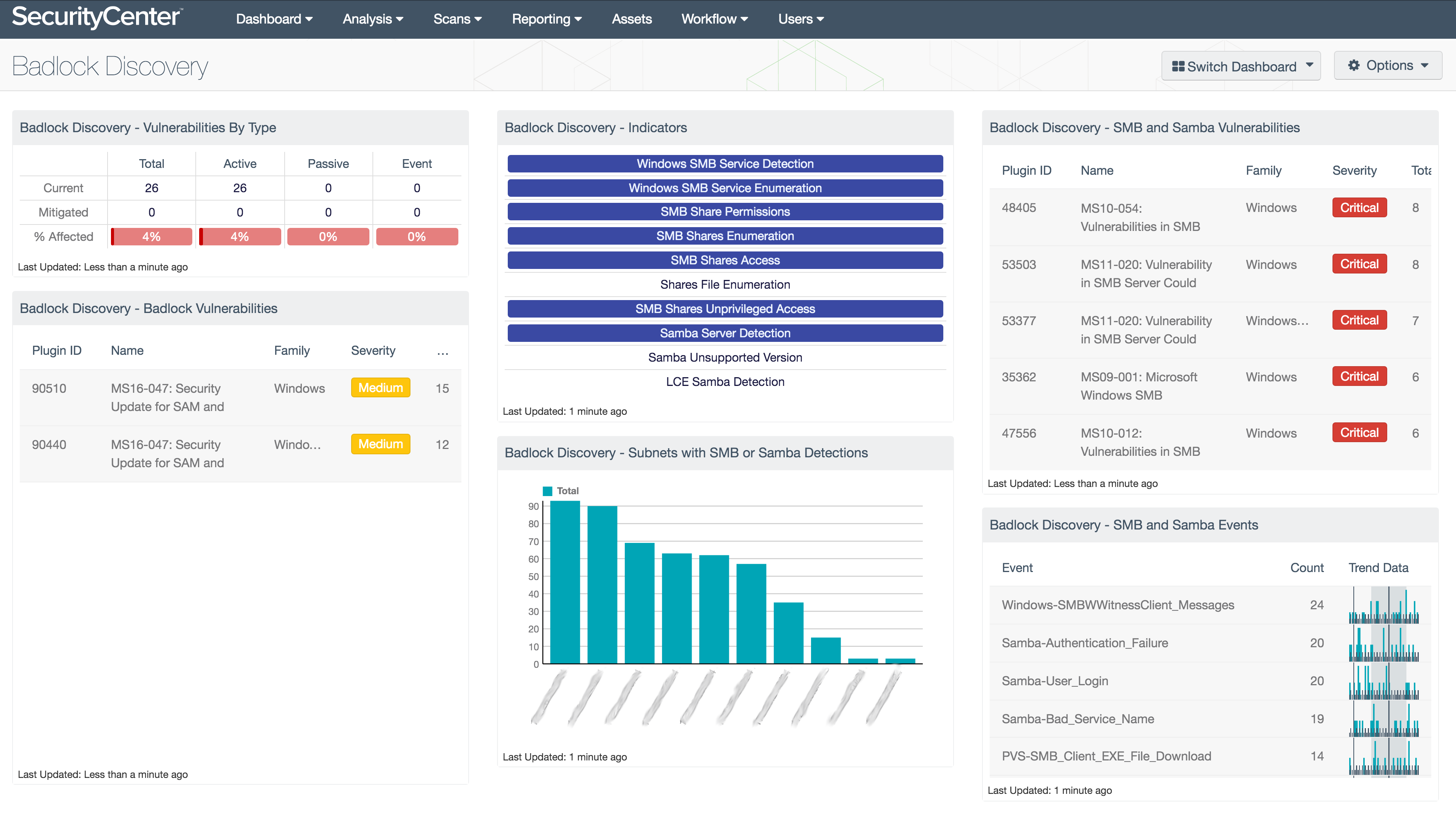
With these high visibility threats though, knowing whether or not you are exposed is just the first step. Mapping out an effective response requires critical context - an ability to interpret the data, prioritize remediations and mitigations, and reduce the risk to your organization as quickly as possible. Again, SecurityCenter CV is uniquely positioned to help. A library of curated dashboards is available from the Tenable Research Team, who delivers new dashboards when new vulnerabilities emerge. Here’s a recent example of a dashboard the team developed when the Badlock vulnerability was announced earlier this year:
Tenable introduces new Exposure Response solution
History tells us that exposure response isn't trivial. A full year after Heartbleed was announced, 74% of Global 2000 organizations were still exposed, as noted by Fortune. At Tenable, we want to make it easier. That’s why today, we’ve introduced the new Exposure Response solution.
Our Exposure Response solution is intended to help organizations understand how to identify high visibility threats and vulnerabilities and immediately respond to them. Using the data collection mechanisms and dashboards described earlier, SecurityCenter CV delivers both visibility and context to make exposure response easier and more effective.
SecurityCenter CV delivers both visibility and context to make exposure response easier and more effective
If you’re interested in learning more, visit our Exposure Response page. You’ll find whitepapers and other materials to learn more about how SecurityCenter CV can help you quickly identify threats and vulnerabilities, and effectively respond to them.
Keep up with the latest from Tenable! Subscribe to the Tenable Blog by clicking Blog email updates on the Blog Home Page.
Learn more
- Vulnerability Management
- Vulnerability Scanning



Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success