Primary Group ID Attack in Active Directory: How to Defend Against Related Threats

The Primary Group ID in Active Directory, created to help manage access to sensitive resources, has become a critical vulnerability that attackers can exploit to escalate privileges without leaving a trace.
The Primary Group ID in Active Directory was originally developed to support the UNIX POSIX model and integration for controlling access to resources. Traditionally, the PrimaryGroupID attribute for a user needed to match the RID (or relative identifier) of the group with which the user must be associated. By default, all Active Directory users have a PrimaryGroupID of 513, which is associated with the Domain Users group.
However, if the user needed to be seen as a Domain Admin for POSIX, the PrimaryGroupID needed to be 512, the RID for that group. The Enterprise Admins group, 519, is also used to grant this level in POSIX.
The caveat is that Active Directory’s built-in management tools, the AD Users and Controls (ADUC), require users to have membership in the group used for the PrimaryGroupID, so a standard user could not be seen as a privileged user without actually being in the privileged group. Even today, when you attempt to move a user with a privileged PrimaryGroupID out of the group the ID represents, Active Directory will not allow you to do so. Similarly, a user who is not in a privileged group cannot have the PrimaryGroupID modified manually to be a privileged group’s ID.
The PrimaryGroupID attribute is not used much anymore, as newer technologies such as Identity Management for Unix (IdMU), Services for Network File System (NFS) and Services for Unix-based Applications (SUA) no longer need this attribute. Ideally, the value should be set to 513, which is the Domain Users group. The value cannot be blank, as Active Directory uses it to generate the initial group assignment during the user creation process, to make sure the user will receive a set of minimum permissions.
However, there are some attacks, such as DCShadow, which can alter the PrimaryGroupID attribute for a user to be 512 or 519, even though the user is not in one of the privileged groups. This attack, which does not create events in the log, is stealthy, persistent and difficult to detect.
Therefore, it is necessary to have a security solution that can detect when the PrimaryGroupID of users changes and when a DCShadow attack occurs. Tenable.ad is a solution that can continuously detect both of these attacks in real time, as you can see by the solution’s Indicators of Exposure shown in Figure 1.
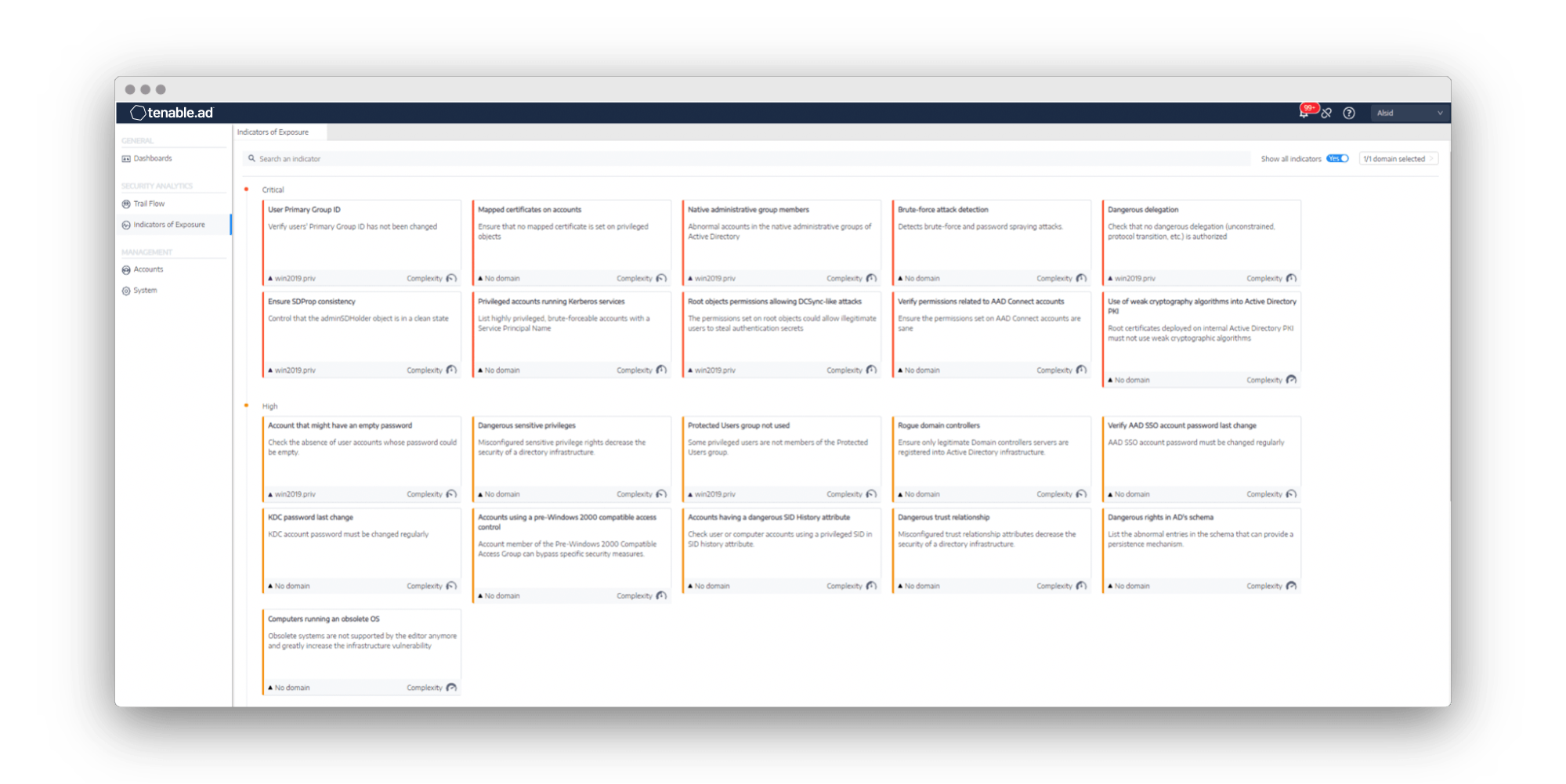
Figure 1. Tenable.ad can detect both a DCShadow attack and modification of the PrimaryGroupID for users.
Being able to see different components of an attack in real time allows the security team to react with swift precision to stop adversaries in their tracks.
For more information on this topic and strategies for strengthening your Active Directory security, visit our Tenable.ad product page.
This blog post originally appeared on the Alsid website on July 14, 2020.
Learn more
- Active Directory



Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success