Microsoft’s January 2020 Patch Tuesday Kicks Off the New Year with 49 New CVEs
UPDATE 01-30-2020: The Solution section has been updated to reflect that a direct check plugin to test for CVE-2020-0609, CVE-2020-0610 and CVE-2020-0612 has been released (Plugin ID 133306).
UPDATE 01-23-2020: Researcher ollypwn has released a proof of concept (PoC) titled BlueGate which leverages CVE-2020-0609 and CVE-2020-0610 for a potential Denial of Service (DoS) attack.
Microsoft kicks off 2020 by patching 49 CVEs, eight of which are rated as critical.
Microsoft rang in 2020 with 49 CVEs addressed in the January 2020 Patch Tuesday release. This update contains 12 remote code execution flaws and eight vulnerabilities that are rated as critical. This month’s updates include patches for Microsoft Windows, Microsoft Office, Internet Explorer, .NET Framework, NET Core, ASP.NET Core and Microsoft Dynamics. The following is a breakdown of the most important CVEs from this month’s release.
CVE-2020-0601 | Windows CryptoAPI spoofing vulnerability
CVE-2020-0601 is a spoofing vulnerability in crypt32.dll, a core cryptographic module in Microsoft Windows responsible for implementing certificate and cryptographic messaging functions in Microsoft’s CryptoAPI. For a more detailed examination of this vulnerability, check out our blog post here.
CVE-2020-0609 and CVE-2020-0610 | Windows Remote Desktop Gateway (RD Gateway) remote code execution vulnerability
In the wake of critical pre-authentication flaws from 2019, including BlueKeep (CVE-2019-0708) and DejaBlue (CVE-2019-1181, CVE-2019-1182, CVE-2019-1222 CVE-2019-1226), Microsoft has patched two new remote desktop flaws, this time in the Windows Remote Desktop Gateway (RD Gateway). CVE-2019-0609 and CVE-2019-0610 are both pre-authentication remote code execution vulnerabilities, which can be exploited when an unauthenticated attacker connects to the target system using RDP and sends specially crafted requests. Microsoft notes these flaws have not yet been exploited in the wild, but rates these both as ‘Exploitation More Likely.’ Patches have been released for Server 2012, Server 2012 R2, Server 2016 and Server 2019.
CVE-2020-0611 | Remote Desktop Client remote code execution vulnerability
CVE-2020-0611 is a remote code execution vulnerability that exists in the Windows Remote Desktop Client. Exploitation of this flaw would allow an attacker to execute arbitrary code on the machine of the connected client. To successfully exploit this flaw, an attacker would have to convince a user to connect to a malicious server, making exploitation of this flaw less likely. While this flaw is only scored as a CVSS 7.5, Microsoft still rates this as critical severity.
CVE-2020-0605, CVE-2020-0606 and CVE-2020-0646 | .NET Framework remote code execution vulnerability
CVE-2020-0605, CVE-2020-0606, and CVE-2020-0646 are remote code execution vulnerabilities in .NET Framework. Exploitation of these vulnerabilities requires that a user open a specially crafted file with an affected version of .NET Framework. In an email attack scenario, an attacker could exploit the vulnerability by sending the specially crafted file to the user and convincing the user to open the file.
CVE-2020-0603 | ASP.NET Core remote code execution vulnerability
CVE-2020-0603 is a remote code execution vulnerability in ASP.NET. Exploitation of the vulnerability requires that a user open a specially crafted file with an affected version of ASP.NET Core. In an email attack scenario, an attacker could exploit the vulnerability by sending the specially crafted file to the user and convincing the user to open the file.
CVE-2020-0650, CVE-2020-0651 and CVE-2019-0653 | Microsoft Excel remote code execution vulnerability
This month, Microsoft released 3 CVEs for remote code execution vulnerabilities in Microsoft Excel: CVE-2020-0650, CVE-2020-0651 and CVE-2020-0653. These flaws exist due to a flaw in properly handling objects in memory. Successful exploitation of these vulnerabilities would allow an attacker to execute arbitrary code in the context of the current user. To exploit these flaws, an attacker would need to convince a logged-in user to open a specially crafted file with an affected version of Microsoft Excel.
Windows 7 and Server 2008 R2 end of support
As a reminder, Windows 7 and Server 2008 support was discontinued on January 14, 2020, so we strongly recommend identifying and upgrading end-of-life systems. Plugin ID 122615 (Microsoft Windows 7 / Server 2008 R2 Unsupported Version Detection) can be used to identify the OS running on a target to assist in identifying end-of-support devices.
Tenable solutions
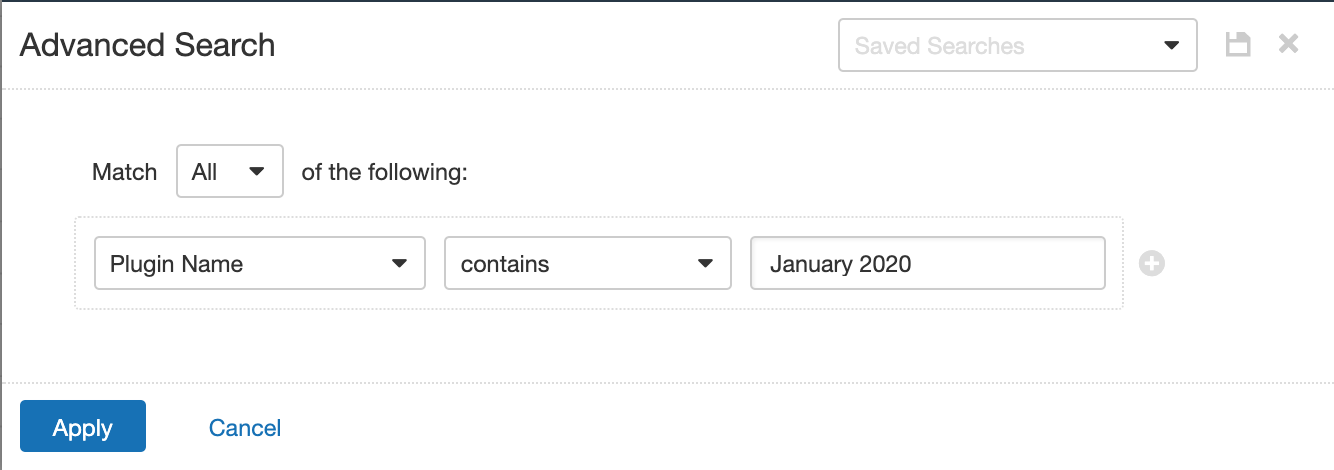
Users can create scans that focus specifically on our Patch Tuesday plugins. From a new advanced scan, in the plugins tab, set an advanced filter for Plugin Name Contains January 2020.
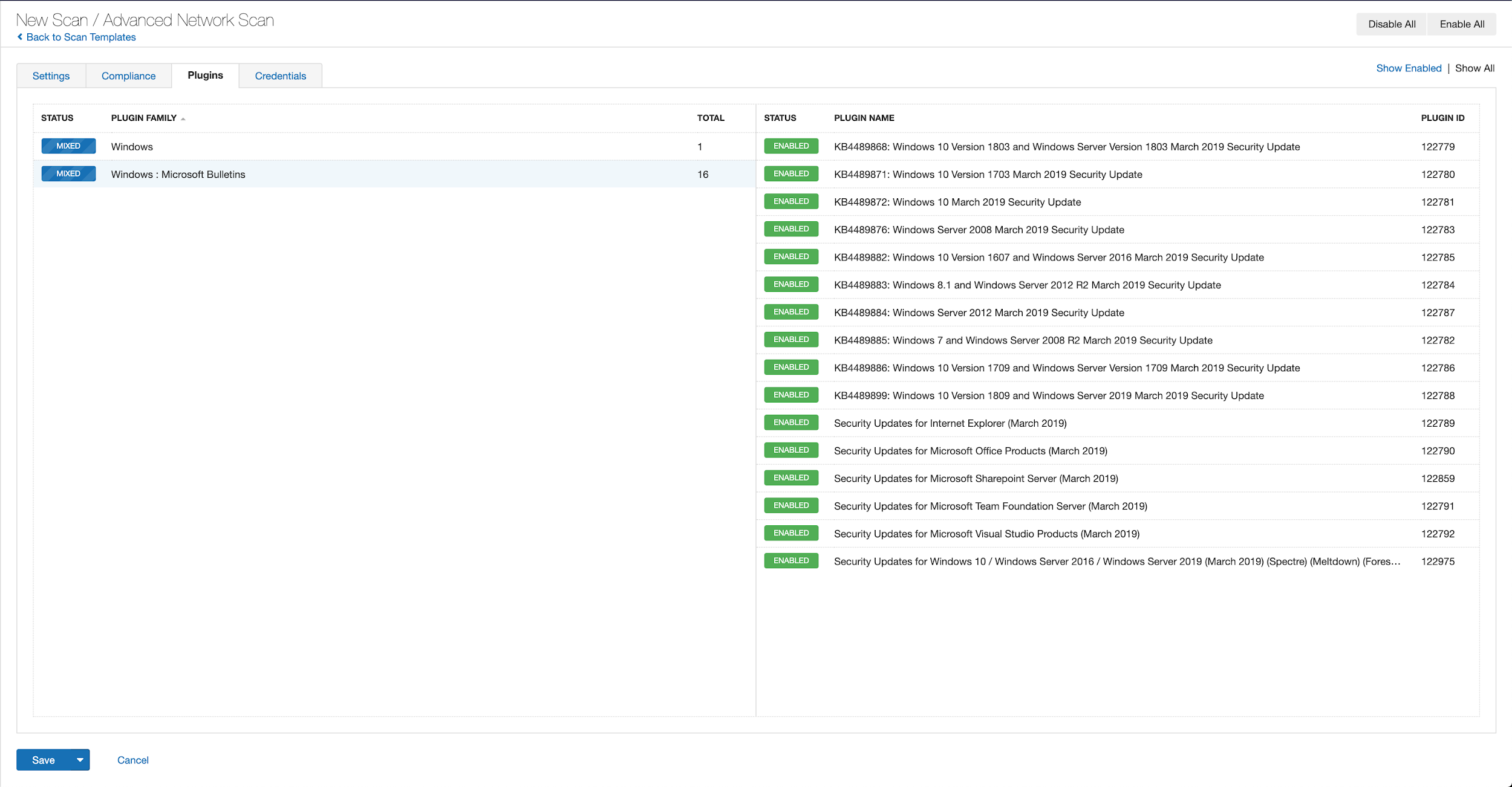
With that filter set, click the plugin families to the left, and enable each plugin that appears on the right side. Note: If your families on the left say Enabled, then all the plugins in that family are set. Disable the whole family before selecting the individual plugins for this scan. Here’s an example from Tenable.io:
A list of all the plugins released for Tenable’s January 2020 Patch Tuesday update can be found here. As always, we recommend patching systems as soon as possible and regularly scanning your environment to identify those systems yet to be patched. An uncredentialized check testing for systems vulnerable to CVE-2020-0609/CVE-2020-0610/CVE-2020-0612 (Plugin ID 133306) have been released.
Get more information
- Microsoft's January 2020 Security Updates
- Tenable plugins for Microsoft January 2020 Patch Tuesday Security Updates
Join Tenable's Security Response Team on the Tenable Community.
Learn more about Tenable, the first Cyber Exposure platform for holistic management of your modern attack surface.
Get a free 30-day trial of Tenable.io Vulnerability Management.
- Vulnerability Management

