Measuring Security Assurance: The Right Tools to Achieve Success

Imagine you’re standing on the beach with your boss. He hands you a ruler and tells you it’s your job to measure the ocean and make sure that it stays within acceptable parameters for “ocean safety.” You’d probably think he was crazy. A ruler isn’t the right tool to measure that vast and constantly changing environment. Furthermore, what metrics could you possibly collect that would have any bearing on whether or not the ocean was “safe”?
IT security teams face a comparable challenge when they try to measure the effectiveness of their security programs. With the prevalence of cloud services and mobile devices, enterprises have become enormous, complex, borderless infrastructures. Just knowing what you have that needs to be secured is a challenge. Finding security metrics that actually communicate meaningful information on the security state of your organization and the effectiveness of your security programs to business executives and the board is even harder.
You need a better way
On their own, security metrics can be just noise – easily overwhelming CISOs and other IT leaders and business executives.
According to Gartner in Sharpen Your Security Metrics to Make Them Relevant and Effective:
CISOs are unhappy with their existing security metrics, and are asked to improve them, but they are not sure what better and more meaningful metrics look like.
At Tenable, we repeatedly hear of this unhappiness in the hundreds of conversations we have with CISOs each year. CISOs and other IT leaders continue to struggle to use security metrics effectively when explaining to business executives and the board how and why security investments are being made.
To help with this problem, Tenable recently sponsored the publication of a highly insightful ebook, Using Security Metrics to Drive Action: 33 Experts Share How to Communicate Security Program Effectiveness to Business Executives and the Board. In this book, experts from diverse industries share their first-hand experiences and best practices for using security metrics to communicate security program effectiveness and for implementing actionable security metrics. One important point that these experts repeatedly highlight is the importance of effectively translating security metrics into business language.
The importance of effectively translating security metrics into business language
Spanning the gap between IT and the business when measuring security program effectiveness and communicating security assurance is critical. To be successful, you must have tools and processes in place that enable you to define security metrics that make sense; that business executives and the board can understand; and that drive action at both the strategic and operational level. This requires not only defining the correct metrics, but having trustworthy data and ways to measure these metrics – and in a format that visually makes sense to business users.
Measure security assurance more effectively, close the communication gap
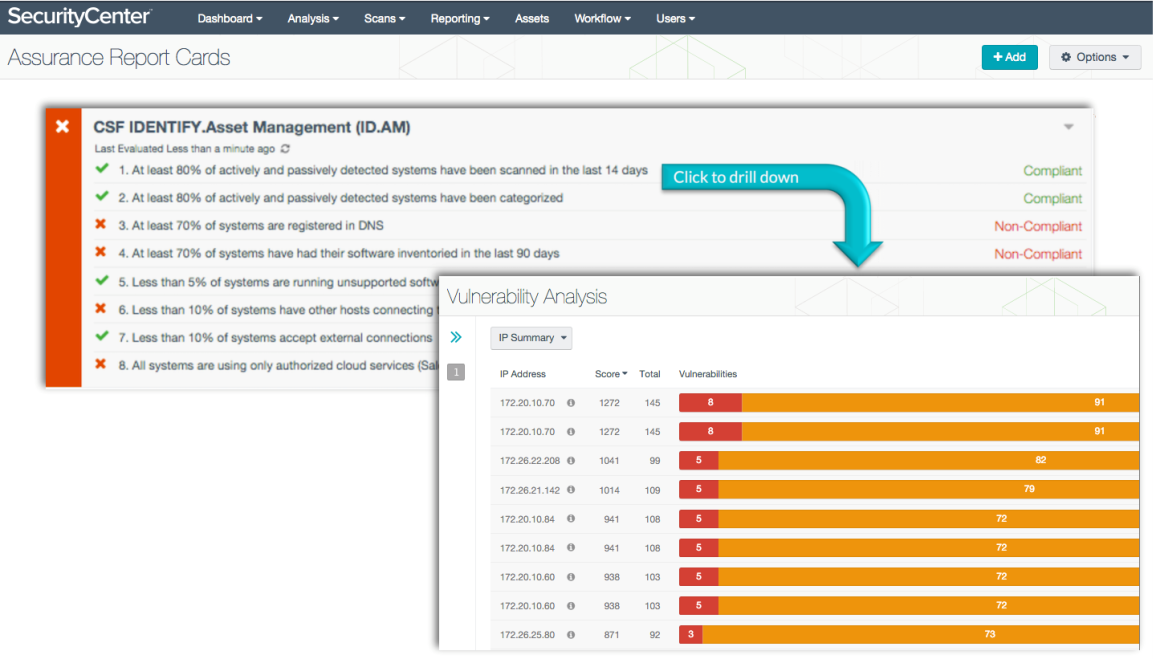
To help CISOs and other IT security leaders more effectively measure their security posture and close the communication gap, Tenable helps you measure security assurance in SecurityCenter Continuous View™ (SecurityCenter CV™). Security assurance capabilities in SecurityCenter CV align security metrics with business goals through proactive measurement, analysis of security metrics, and visualization of security metrics using customizable dashboards, reports, and the industry’s first Assurance Report Cards™ (ARCs).
Our approach to measurement is two-fold:
- We give you the tools to define security metrics in a way that aligns directly with your business goals.
- We ensure those metrics are accurate, using reliable data collection methods that include active scanning, agent scanning, integrations with third-party systems, passive listening, and host data activity monitoring.
One size doesn’t fit all
When it comes to security assurance, there is no one-size-fits-all template for developing meaningful security metrics, because each business is unique.
There is no one-size-fits-all template for developing meaningful security metrics, because each business is unique
If you don’t know where to start in terms of defining security program objectives and security assurance metrics and mapping them to business objectives, Tenable provides five pre-packaged ARCs, known as Tenable’s Five Critical Cybersecurity Controls. The five controls summarize the most important points presented in industry standards such as the 20 Critical Security Controls from the Center for Internet Security (formerly from the SANS Institute), the NIST Cybersecurity Framework, and the PCI Data Security Standard. Adopting these five controls enables you to identify the security strengths and weaknesses of your organization and start improving alignment with business leaders.
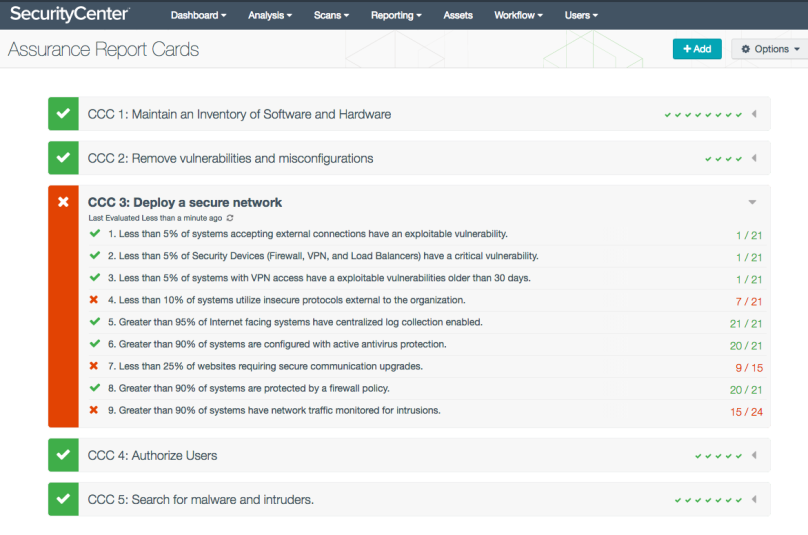
If you already know what your business objectives are, you can map your business objectives to the policies and controls used in your security program by creating your own custom ARCs. ARCs are powerful and flexible. You can define security policy statements in ARCs that map upwards to business objectives, as well as downward to security controls and their underlying data. With ARCs, you can take a metric-driven approach to visualizing and communicating security program effectiveness. ARCs use business language that executives understand, helping business executives and other IT leaders quickly grasp the impact of security efforts by visualizing progress and gaps.
ARCs use business language that executives understand
For example, a report card for a healthcare organization that provides home health visits could help identify vulnerabilities on mobile devices that have taken longer than 30 days to fix – since that interferes with HIPAA compliance for protecting patient information.
At an online retailer, a report card could easily show that the percentage of payment systems patched in the last month has met corporate goals without interfering with order processing.
Even if you’re not sure exactly how you want to develop security metrics, but are thinking about implementing the NIST Cybersecurity Framework in your organization, we can get you started with eight pre-built ARCs that align with the NIST Cybersecurity Framework.
Measure, communicate, improve, succeed
If your security team is struggling to validate their ongoing security assurance efforts and justify budget requests to the board, Tenable can help. SecurityCenter CV security assurance capabilities enable you to better communicate the effectiveness of your security programs, justify or revise security investments, and ensure compliance with corporate or industry security mandates.
Learn more
Want to know more? Check out these resources:
- ebook: Using Security Metrics to Drive Action: 33 Experts Share How to Communicate Security Program Effectiveness to Business Executives and the Board
- Solution Story: Tenable Security Assurance
- Whitepaper: Communicating Security Program Effectiveness: SMART Metrics and SecurityCenter Continuous View
Keep up with the latest from Tenable! Subscribe to the Tenable Blog by clicking Blog email updates on the Blog Home Page.
Learn more
- Metrics
- Security Assurance
- SecurityCenter



Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success