Leveraging NIST Standards to Build Your Enterprise Security

The federal government has produced a body of standards and guidelines—including the NIST Cybersecurity Framework—that can help the private sector as well as government agencies improve information security. Automation can help you take full advantage of these standards.
The U.S. Department of Defense (DOD) now requires contractors holding sensitive government information on their IT systems to comply with federal cybersecurity guidelines spelled out in Special Publication 800-171 from the National Institute of Standards and Technology (NIST) by the end of 2017.
The DOD mandate reflects what a department spokesperson called the “urgent need to increase cybersecurity requirements.” The guidelines are crafted specifically for the private sector and provide a path to security for contractors using government controlled unclassified information (CUI).
This is an example of how government standards are shaping private sector cybersecurity.
The trend toward standardized security
Government standards are shaping private sector cybersecurity
Corporate enterprises increasingly are taking advantage of security standards developed by and for the federal government. With the recognition that private sector cybersecurity is essential to national security and the national economy, NIST is helping to create a foundation of standards, best practices and guidance that can be applied across the nation’s information infrastructure.
Some efforts, such as the Security Content Automation Protocols (SCAP), have already had a major impact. The requirement that government agencies use tools that comply with the SCAP open security standards has resulted in the availability of a wide range of commercial products that also help companies automate security monitoring and scanning. Other programs are being crafted specifically for the private sector, such as the NIST Framework for Improving Critical Infrastructure Cybersecurity, commonly referred to as the Cybersecurity Framework (CSF).
The core of NIST security guidance is the extensive catalog of security controls contained in SP 800-53. These controls, together with industry standards and best practices, are used to produce flexible, interoperable guidelines that can be adapted to fit the needs of organizations of almost any type and size. Because of this integration and flexibility, organizations can easily find the appropriate security controls for meeting the requirements of their own security policies, and to comply with industry or government regulation.
Adoption of guidance such as the Cybersecurity Framework is becoming viewed as a best practice
As a result, government security standards and guidance are finding wide adoption in the private sector. Adoption of guidance such as the Cybersecurity Framework is becoming viewed as a best practice, helping organizations move beyond mere regulatory compliance to effective risk management. A Gartner study estimated that 30 percent of U.S. organizations were using the CSF in 2015 and predicted that it would be 50 percent by 2020.
Automation helps leverage standards-based security
Although the Cybersecurity Framework was created to adapt to the needs of organizations of all sizes, implementing it is not necessarily easy when IT budgets and resources are stretched thin. Manual assessment, configuration and validation of controls and settings can be time consuming and resource intensive. Automation can replace manual processes to help ease the adoption of the CSF and other standards.
Automation can replace manual processes to help ease the adoption of the CSF
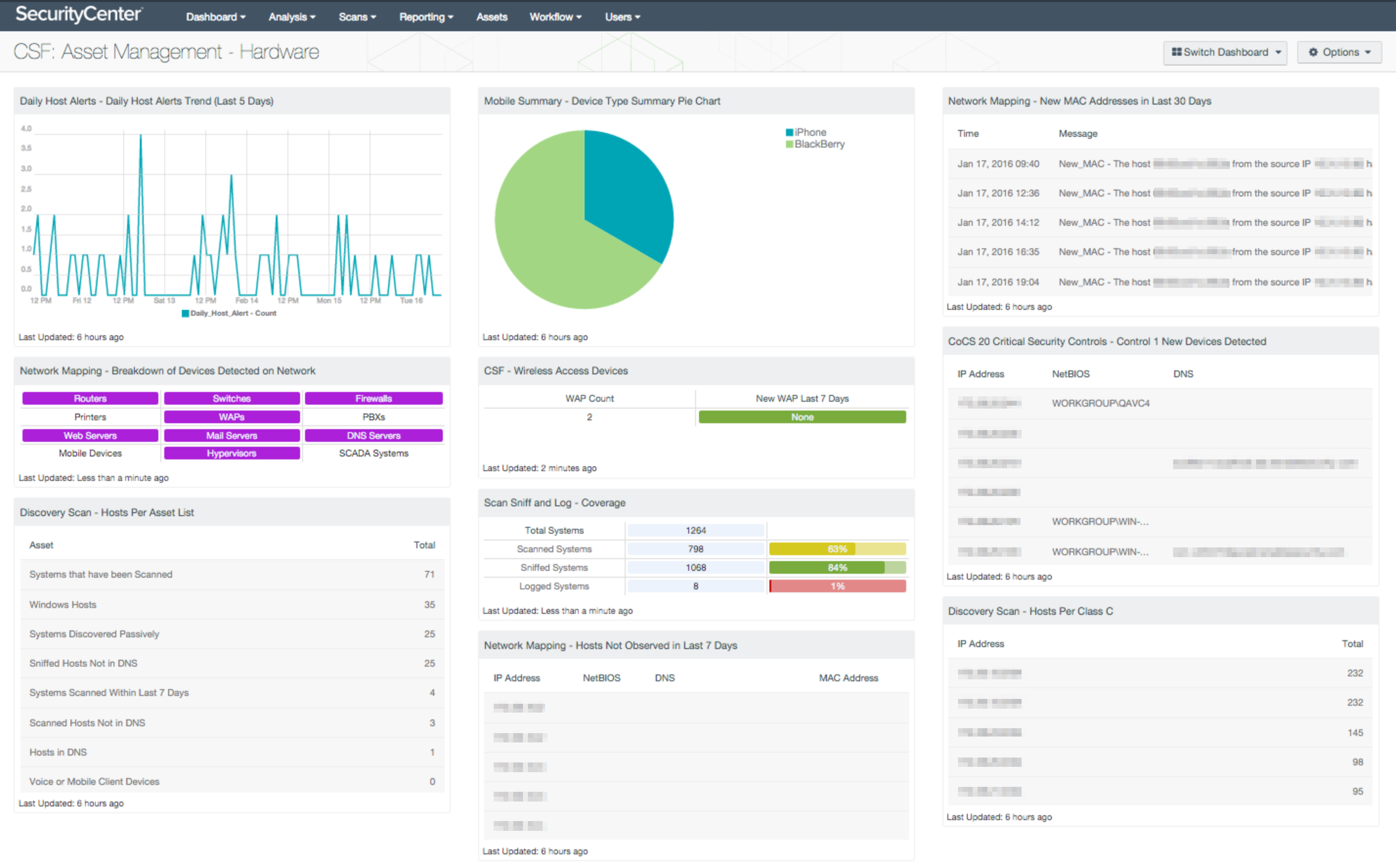
SecurityCenter™ from Tenable Network Security was validated for compliance with SCAP 1.2 in 2015. At RSA Conference 2016, Tenable also announced a new solution making it easier for companies and government agencies to ensure conformance with CSF. SecurityCenter Continuous View™ (SecurityCenter CV™) includes the industry’s first CSF dashboards to provide a unified view of the organization’s IT landscape. It replaces manual processes by automating:
- Conformance assessments to evaluate the technical controls in place and validate that they are operating effectively.
- Continuous monitoring across both industrial control systems and IT networks, including physical and virtual infrastructure, cloud, and mobile environments.
- CSF-specific customizable Assurance Report Cards (ARCs) and dashboards to provide a unified view of conditions.
- Comparison of current security posture to a target security profile to identify gaps and create a roadmap to a defensible security program.
To learn more about how SecurityCenter CV can help you take advantage of the Cybersecurity Framework, visit Tenable Network Security.
Learn more
- Federal
- Government
- NIST
- Standards




Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success