Ghost in the Machine: “MouseJack” Wireless Mouse and Keyboard Injection Vulnerability (Updated)

It was over 6 years ago that the wireless keyboard sniffer project known as “Keykeriki” was first demonstrated. The sniffer allowed someone to eavesdrop on what is being typed as each key was pressed on the keyboard. Recently, another vulnerability dubbed “MouseJack” has been discovered in the way some wireless devices, such as the Logitech Unifying Receivers for wireless keyboards process received RF packets, allowing keystroke injection that bypasses encryption. Exploiting this vulnerability involves transmitting RF packets to a vulnerable vendor dongle and requires physical proximity to the target computer. This vulnerability can be remediated by removing the device or updating the firmware on the vendor dongle to only accept encrypted RF keyboard packets.
Searching for affected devices
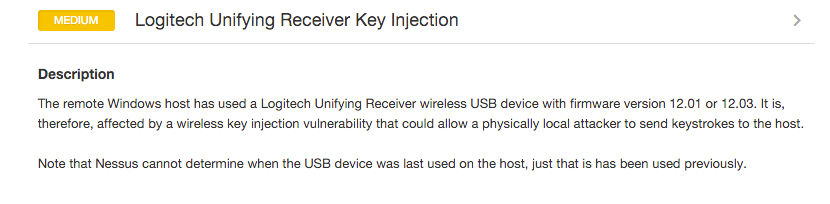
While USB Device History Auditing has been a long time capability of Nessus®, Tenable has released two new local plugins to detect the presence of affected devices. A plugin (ID 88905) to detect the presence of affected versions of the Logitech Unifying Receiver, and another (ID 88934) to detect the presence of other devices that are potentially affected by either wireless key injection or a denial of service. Since the plugins report on historical devices, they require that the scan reporting mode be set to “Paranoid”.
In this example, we have USB devices with a Vendor ID (VID) 0x046D and Product ID (PID) 0xC52B. I used both http://www.PCIDatabase.com and http://www.linux-usb.org/usb.ids to identify the corresponding VID as Logitech Inc., and the Product is a USB Receiver. The plugin will report if a vulnerable device has been previously utilized by the host and manual validation will need to be performed if the device is still in use.
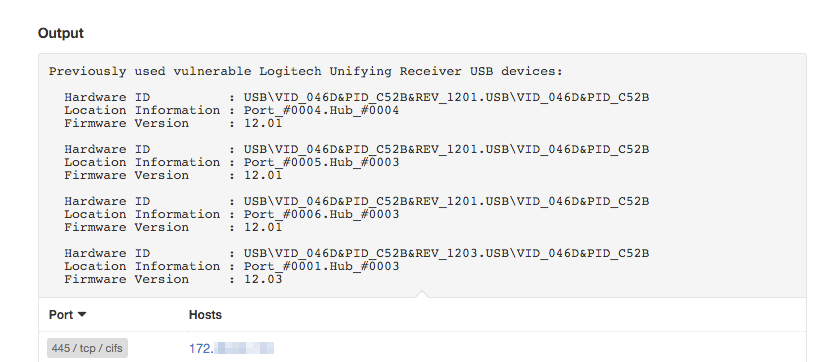
USB event monitoring
SecurityCenter Continuous View™ and the Log Correlation Engine™ ( LCE®) Windows client can also detect USB device insertions and removals. The logs generated by these events are normalized to the “usb” event type and include the following normalized events:
Windows-LCE_Client_Detected_Attached_Drive: A USB or CD-ROM drive was attached.
Windows-LCE_Client_Detected_Removed_Drive: A USB or CD-ROM drive was removed.
Windows-LCE_Client_Detected_Attached_USB_Device: A USB peripheral was attached.
Windows-LCE_Client_Detected_Removed_USB_Device: A USB peripheral was removed.
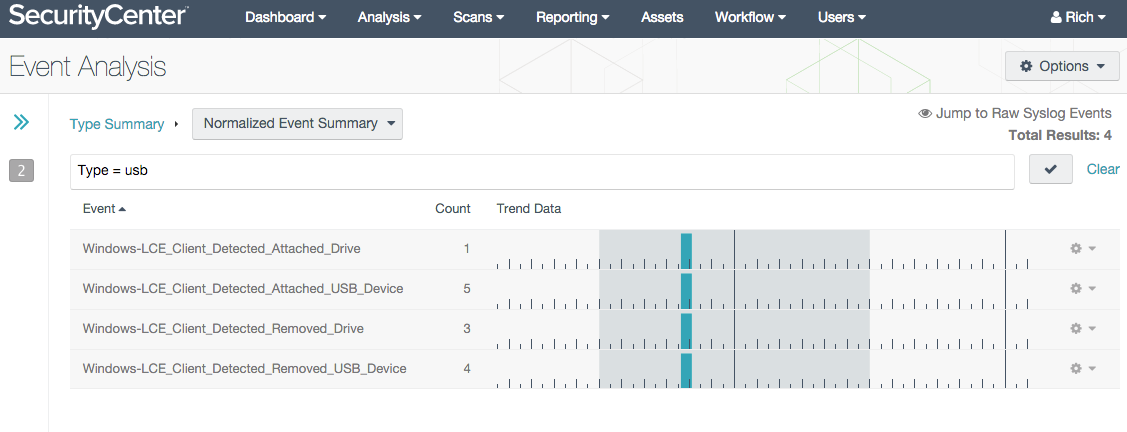
The Windows-LCE_Client_Detected_Attached_USB_Device event indicates that the LCE client detected the attachment of a USB device. The event tells us about the device being attached or detached, including the Vendor ID (VID), the Product ID (PID), and the device serial number/Windows unique identifier, allowing users to look up exactly what is being attached to their hosts.
You can use the following query to alert on the presence of the Logitech Unifying Receiver in your environment:
Type = usb; Normalized Event = Windows-LCE_Client_Detected_Attached_USB_Device ; Syslog Text = “046D AND C52B”To enable USB event monitoring, use one of the two following configuration tags in your LCE Windows Client policy:
<event-log>Volumes</event-log> <!-- Monitors for USB Events -->
<event-log>all</event-log> <!-- Monitors for all Events including USB -->Note "Volumes" is a special entry for device monitoring and is not really an event log (or you can also use “all”).
References
Cert Vulnerability Note VU#981271
Flaws in Wireless Mice and Keyboards Let Hackers Type on Your PC
USB Device History Auditing with Nessus
LCE Windows Client - New USB Events
Updated February 25, 2016
Learn more
- Nessus
- Plugins
- SecurityCenter
- Vulnerability Scanning



Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success