Four Trending Security Issues to Watch
At Black Hat 2015, one of the people I interviewed said the best way we can be smarter about security is to learn from the people who are already smart in security. It’s wise advice and that's why I attended the Infrastructure Security Panel Discussion at VMworld 2015 in San Francisco.
The panel was moderated by Mike Foley (@mikefoley), senior technical marketing manager, VMware, and included panelists:
- Greg Hatch, infrastructure architect, Raymond James
- Steve Kaplan, principal infrastructure architect, Defense Contract Management Agency
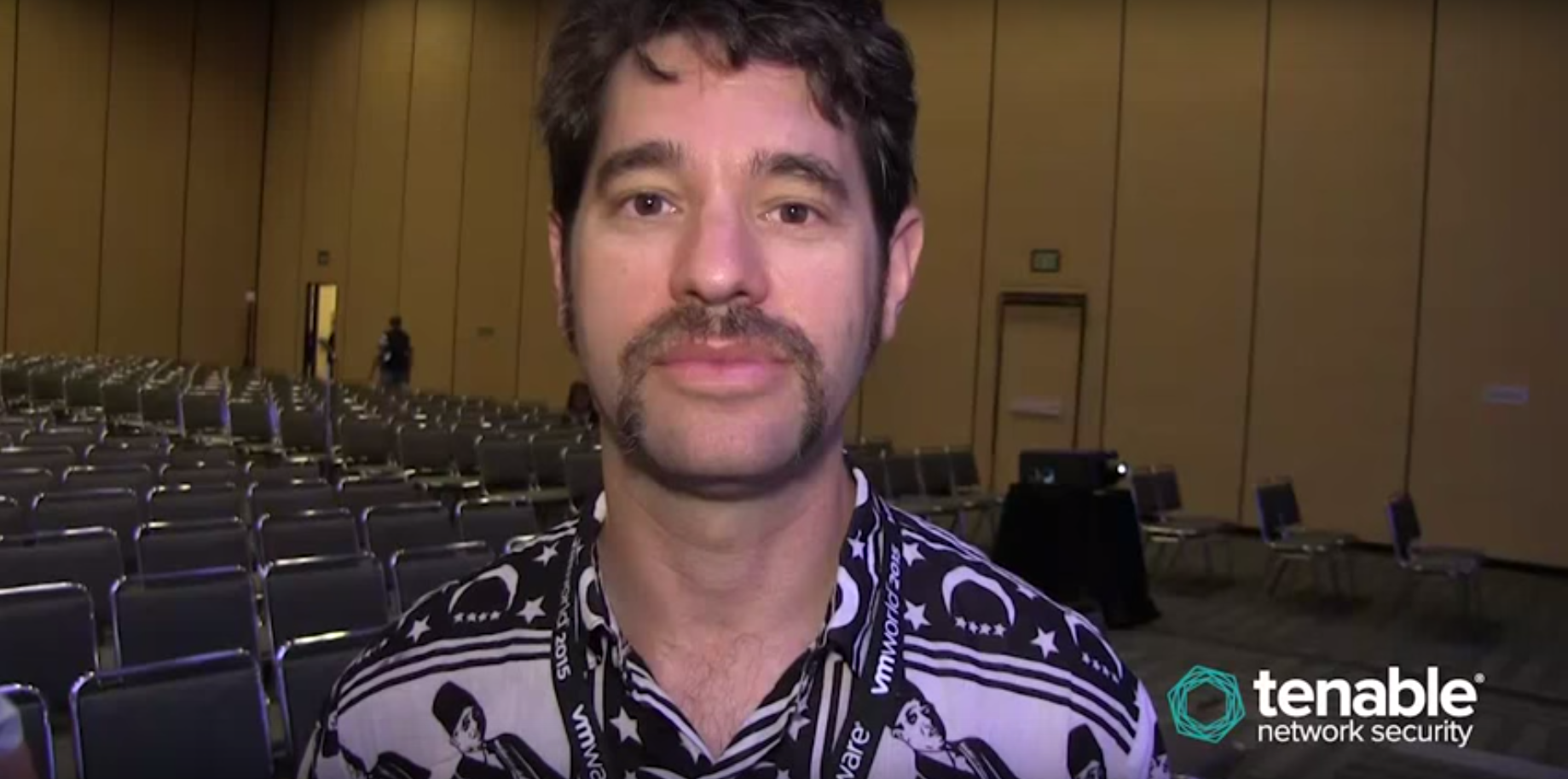
- Davi Ottenheimer (@daviottenheimer), president, flyingpenguin
It was a really interesting discussion on the security issues that many aren’t considering. There were also references to some of the themes of VMworld — that stuff should just work, and that there’s a great need to remove complexity from people’s lives.
I was most intrigued by the following four issues brought up by Ottenheimer, so I asked him to expand them on camera.
Temporary vanishing databases: Can you build a data environment that vanishes after a certain period of time? This would be valuable for disaster recovery if you need to move information to a location temporarily, or to improve performance of an application. If certain data doesn’t need to be persistent, why let it sit around and languish and bring down the performance of the rest of your application?
Authentication should be focused on knowledge: We don’t just authenticate people by their names. We look at them and gather other clues, such as what they look like, the way they walk, talk, who their friends are, etc. For that reason, we should realize that our simple methods of online authentication are far from sufficient, and we should integrate approaches from the way we handle authentication in the real world.
Don’t just ask for a solution. Know the problem: Knowing about problems is important. Don't shut down that discussion by saying, “Don’t tell me the problem. Just fix it.” The real goal is to move away from binary understanding of security issues. Begin looking at analytics so you can have a more nuanced understanding and discussion.
Classifying data creates a new vulnerability: The more metadata you get the more knowledge you have, and that makes it hard to create privacy. Be wary of trying to come up with a schema to determine your most sensitive data. The act of creating metadata can create new vulnerabilities.
Here are some of the other interesting items that came up in the security panel discussion:
- In the financial industry, we don't trust the cloud with our client list and customer data. We are slowly moving towards IaaS.
- The biggest challenge is determining when you’ve been hacked when the hacker is able to get in with valid credentials.
- Do you have a way to monitor all the tools that you have? Do you have the people, and can you have them operational 24 hours a day? Criminals don’t work 9-to-5.
- Lean teams of just two or three hope that they're doing security right. The answer to being better at security is to do and think about it a lot, even if you’re just a small team.
- IT can't provide secure stuff fast enough to the business guys, so the business guys often get what they want themselves. When IT fails this way, it gives rise to shadow IT, or the business procuring tech services themselves. If you’re heading down that path, look at the APIs for SaaS applications. They’re pretty good because they allow you to do an audit and to see who is using these outside applications.
- Most SaaS applications can deliver the security you want, but they don't necessarily have it turned on by default.
- SaaS applications don’t give a satisfactory answer to the question of "can you wipe out all the data completely?" Some won't even let you have access.
- It's important to have all of IT very transparent for users so that they can provision it easily. It's a simple process of letting a request come in and an action be taken. In general, the goal is to drive better IT behavior.
- Everyone wants two-factor authentication on vSphere. Everyone wants it. You just need to yell at the product managers and you'll get it. That's how things often get done. When the customers demand it, it gets done.
- How do you educate the C-suite that they need to think of security beyond compliance? If you go into one of these discussions, they start to glass over. Get into a security discussion by talking about how you’re trying to fix process problems, not necessarily security. Talk about how you can improve the business and the lifecycle of the product. You're just rebranding the classic security discussion.
- If you don't get what you want, you could pull the Fear, Uncertainty, and Doubt (FUD) card. That will help you get what you want. But that only gets you so far.
Learn more
- Conferences



Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success