Endpoint Security with Nessus® Agents
Note: Nessus Cloud is now a part of Tenable.io Vulnerability Management. To learn more about this application and its latest capabilities, visit the Tenable.io Vulnerability Management web page.
Endpoints can include PCs, laptops, smartphones, tablets and specialized equipment such as bar code readers or point of sale (POS) terminals. For the purpose of this article, we'll focus on a specific set of endpoints: laptops used by remote or traveling employees. In other words, ones that aren't always connected to your corporate network.
Each device connecting to the network creates a potential entry point for security threats
Endpoints like laptops present a unique challenge for organizations. On one hand, they offer a lot of benefits. Employees get more flexibility in when and where they work. On the other hand, each device connecting to the network creates a potential entry point for security threats. That threat might be increasing. Not that long ago, most laptop access was through a VPN to get to company resources. Today, with more things being accessed through the cloud, it's very likely that a typical remote employee does not use the VPN at all, and can still get all of the work done.
Managing security risk for all these endpoints is challenging. Applications like Adobe Flash and Java seem especially susceptible to vulnerabilities commonly run on endpoints, end users often don’t comply with security policies, and it can be difficult to scan endpoints for vulnerabilities because they’re not always connected to the corporate network during a scan.
In this article, we’ll look at how to overcome these endpoint security challenges by including endpoints in your vulnerability management program using the recently introduced Nessus Agents.
What are Nessus Agents?
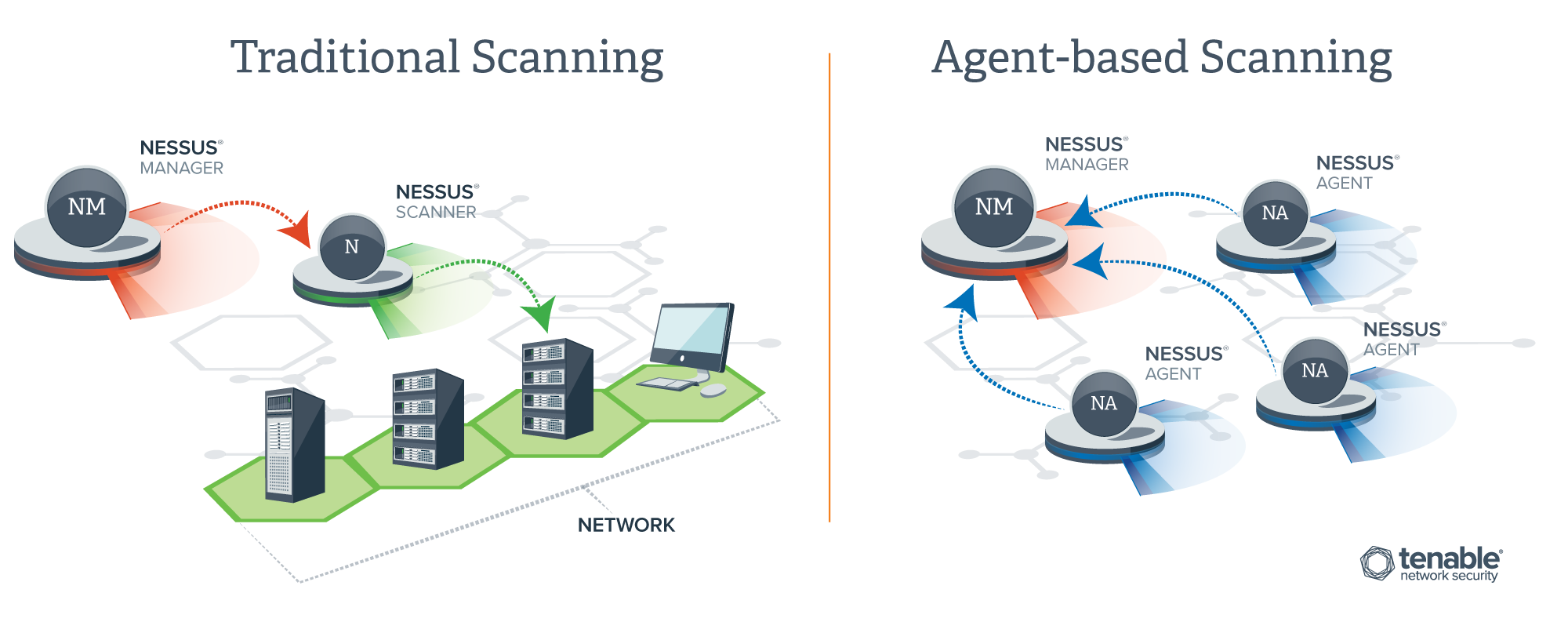
Nessus® Agents are lightweight programs that are installed locally on an endpoint or other host (Nessus Agents can run on endpoints like laptops but also on other assets like servers or virtual machines). Agents receive scanning instructions from a central Nessus Manager or Nessus Cloud server, perform scans locally, and report vulnerability, compliance, and system results back to the central server. Unlike traditional scanning, agents can perform scans at any time, even when the endpoints they’re running on aren’t connected to the corporate network.
Agents can perform scans at any time, even when the endpoints they’re running on aren’t connected to the corporate network
Nessus Agents protect endpoints by identifying configuration errors, malware, suspicious processes or other potential vulnerabilities that if addressed will help prevent security breaches.
How do Nessus Agents work?
Step 1: Use a policy template to define what the Nessus Agent will scan
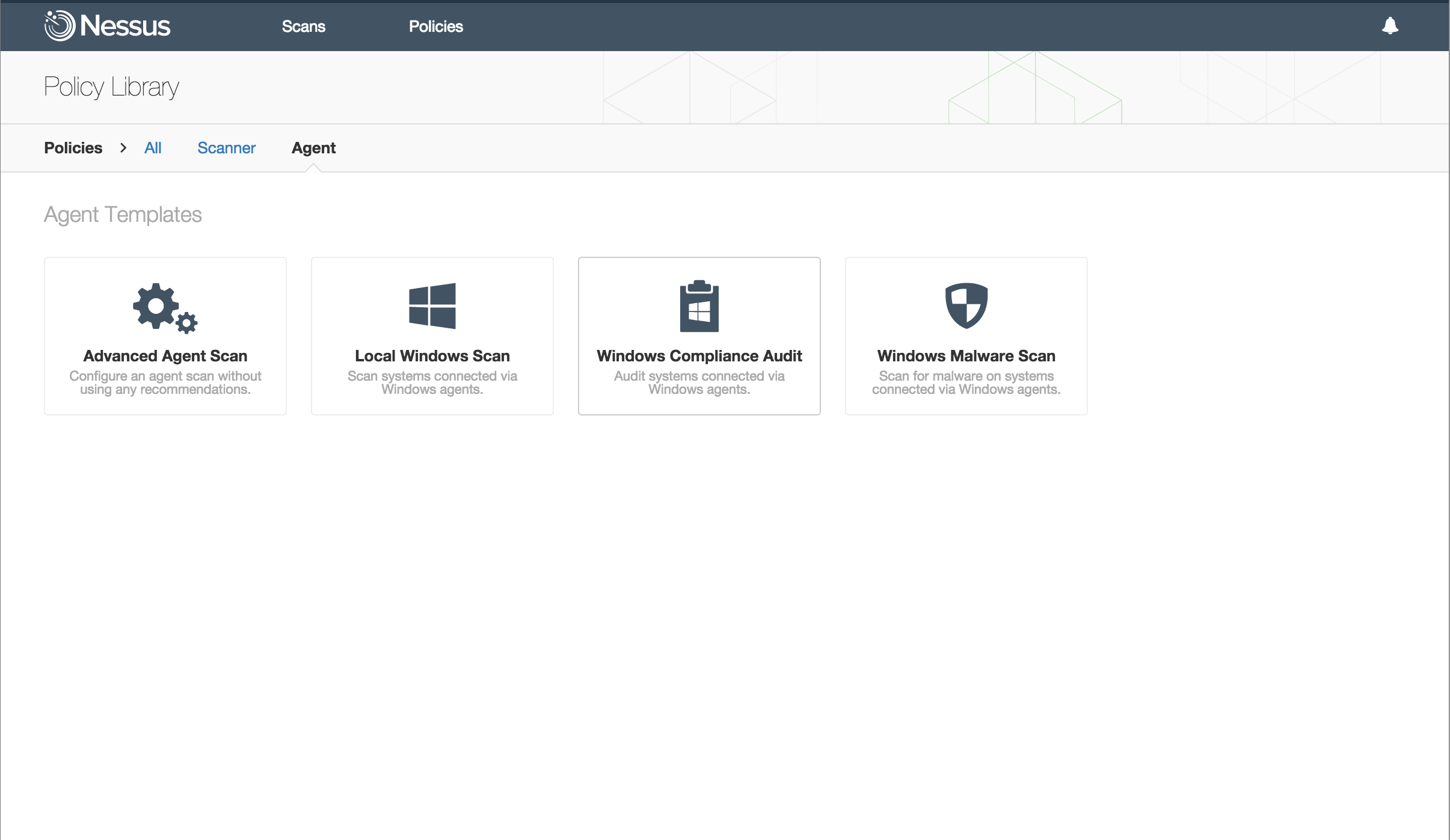
Similar to how Nessus is instructed about what and how to scan for traditional scans, a Nessus Agent scan starts with selecting or creating a policy. Policies define how Nessus should scan and there are a number of agent templates available with Nessus out-of-the-box.
For example, to regularly check if any remote users in my organization have malicious processes running on their laptops, I’d select a Malicious Process Detection policy template to get started.
Step 2: Tell Nessus Agents where and when to scan using that policy, and when to report back results
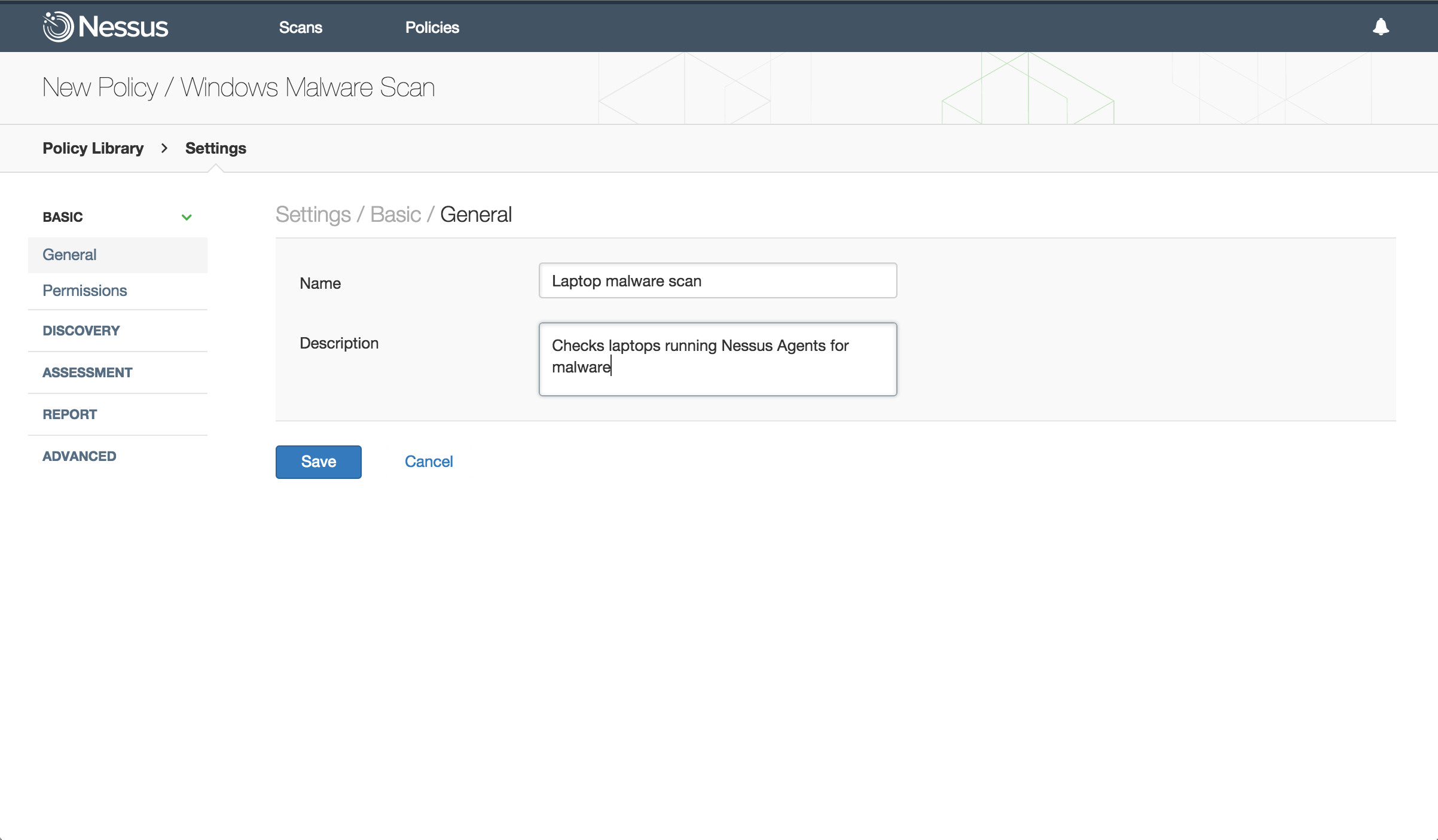
Once I’ve set up the scan policy, the next step is to set up the scan itself. Scanning with Nessus Agents will look familiar to Nessus users, with just a few differences.
Like other Nessus scans, when I’m setting up a new scan, I name the scan and add a description. After that, there are a few additional parameters to identify:
- First, instead of selecting a scanner and specifying targets by IP address or hostname, select the group of agents to serve as targets for the scan (you’ll be presented with a drop down list of groups to choose from). Following the example from earlier, I might have created a group called “Remote Employees” or “Laptops” and use that as the scan target.
- Next, specify the “Scan Window.” This is the window of time when targeted agents can check in, receive a new policy, and upload their results for this particular scan.
- Finally, set the scan schedule: how frequently to run the scan, when it should run and (optionally) if you want to repeat the scan on a regular basis, how frequently to run the scan.
Step 3: Review your results
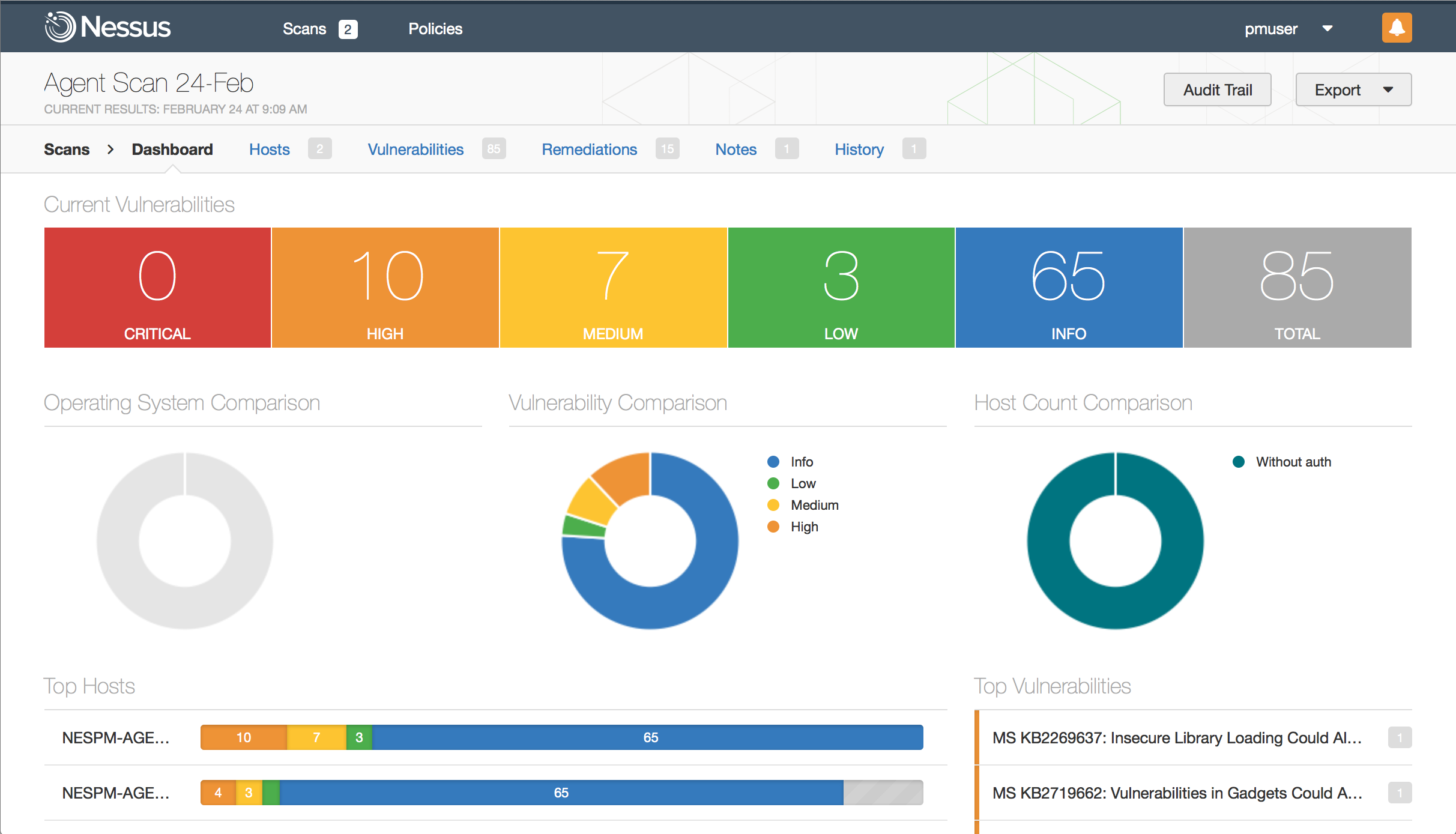
Once the Nessus Agents have run the scan and reported results back to the central Nessus Manager, the results can be viewed in Nessus dashboards or through reports. Dashboards give you an at-a-glance view of scan results with drill-down capabilities and reports give you even more flexibility in filtering results.
Like other scans, you can use the scan results to identify and prioritize vulnerabilities on endpoints to mitigate.
Summary
We expect most organizations will use a mix of agent-based and agent-less scanning. Agents are useful in many situations, including scanning transient devices like laptops. In future articles, we’ll explore other scenarios where agents are useful, like scanning assets where it’s difficult to get and maintain host credentials. We’ll also explore how agents can speed up the scanning the process.
In other scenarios, agent-less scanning will be the preferred method, and that’s why Tenable makes both options available in our Nessus Manager and Nessus Cloud vulnerability management solutions.
Resources
If you’d like to learn more about using Nessus Agents to protect endpoints like laptops, please use the following resources:
- If you are a current Nessus Manager or Nessus Cloud customer, visit the Nessus Download page in the Customer Support Portal to download and start using Nessus Agents.
- If you are a Nessus Professional customer or not currently using Nessus, request an evaluation of Nessus Manager or Nessus Cloud to try either of these vulnerability management solutions.
- If you’d like to get more details on Nessus Agents:
- Read our whitepaper
- Check out this short video
- Watch this on demand webcast
Special thanks to Joseph Sokoly for his generous contributions to this article.
Learn more
- Agents
- Nessus




Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success