Cloud Computing Trade-Offs
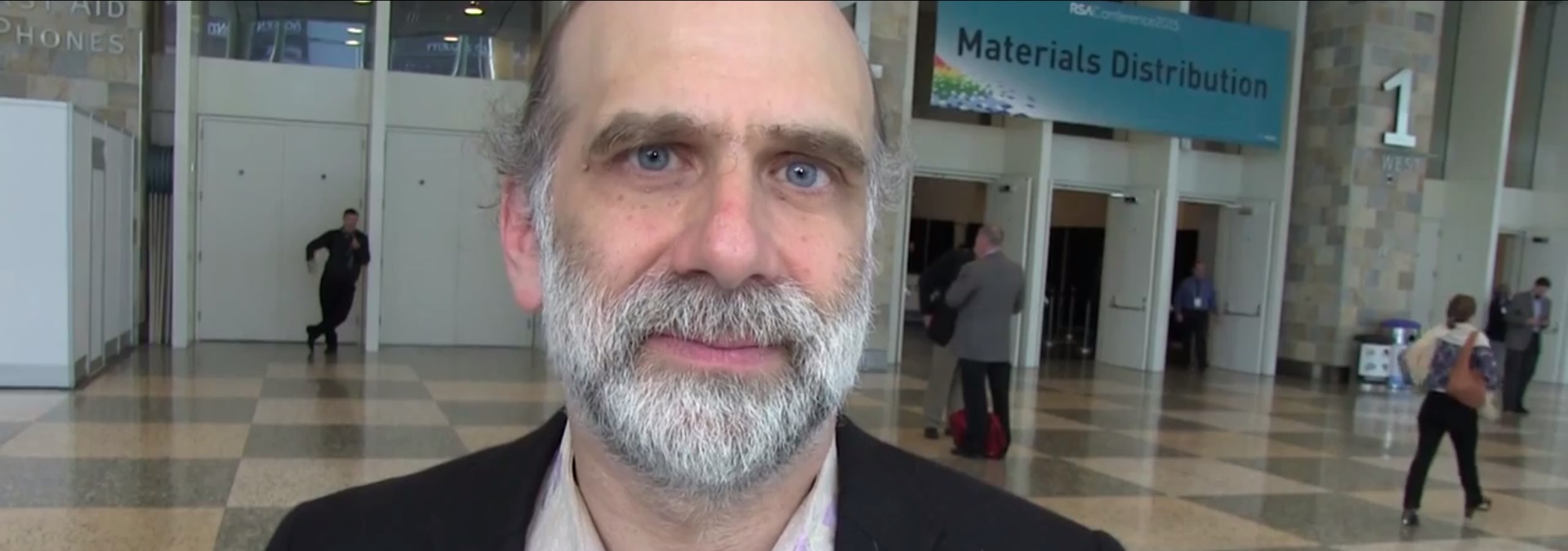
“As a business or as an individual you have to make a choice. Should I do this thing—whatever it is—on my computer and on my network or on a cloud computer on a cloud network,” asked Bruce Schneier (@schneierblog), CTO of Resilient Systems, Inc., in our conversation at the 2015 RSA Conference in San Francisco.
Whatever you choose, you’re going to be making a trade-off. Schneier recommends you first look at who your adversaries are.
“If your adversaries are a cybercriminal, I bet Google can do a better job at securing your stuff than you can. If your adversary is the U.S. government, Google will respond to court orders and not tell you about it, so maybe you’re better keeping it. It’s going to depend on what you’re worrying about,” said Schneier, who runs his personal email on his own computers, not so much for security reasons, but for control. He doesn’t want Google looking at his email or sending him advertising.
Schneier understands that by hosting his own mail versus cloud-based mail will mean he’ll have to give up the ability to have access to his mail from any device and the ability to use Google’s anti-spam and Gmail features. In exchange, Schneier gets to use Eudora, his favorite email program. Plus, he can read his email on airplanes. For him that’s much more important. For a lot of people it’s not.
If your business is moving to the cloud, you’ll have to ask similar questions.
“Business service is the same way. You put stuff on the cloud, you get a lot of benefits. You get a lot of benefits of the cloud services, the management of interactions among customers, you lose the ability to control it locally. Now for a lot of applications and a lot of businesses, that’s a really good trade-off. It’s more reliable, it’s cheaper, it’s more feature rich, and you don’t have to manage it. That’s a plus. You don’t know what country your data is in, maybe. That could be a minus. You don’t know what governments are accessing it. That could be a minus. For most companies I don’t think they care very much. It really depends on who your adversary is, what you’re worried about, and what your trade-offs are,” said Schneier.
Check out Schneier’s full video in which he talks about cloud computing trade-offs. You’ll hear a few other conversations we had about people’s exhaustion with security warnings and what management needs in order to make decisions about security.
Learn more
- Conferences



Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success