Auditing Multiple Databases with Nessus in a Single Scan
If you have been sitting on the fence debating about whether or not you should upgrade to Nessus v6.3, hopefully this blog will provide you with enough incentive to make the switch.
A quick look back
Since its release in 2009, database auditing has become a significant part of Tenable's compliance auditing feature set. But when it was first released, we weren’t sure how it would be received. We knew that auditors often have to convince DBAs to share database credentials to perform an audit. Some DBAs guard their databases like fortresses. It can be hard to gain access. But we listened to our customers and knew that database auditing was needed.
Database auditing proved to be a popular feature
The initial design of the plugin provided just one preference to enter database credentials. To audit more than one database instance or database type (such as Oracle and SQLServer) in a single policy, you had to create an additional Nessus policy; one policy for each instance or database type. And we all know that having tens or even hundreds of database instances within a single production database isn't all that uncommon; nor is having more than one database type.
Database auditing proved to be a popular feature. DBAs appreciated the fact that Nessus never made any changes to the databases during an audit. And they welcomed support for MySQL, Oracle, SQL Server, DB2 and PostgreSQL and Informix. But our customers wanted more flexibility.
The 6.3 solution
With release of Nessus v6.3, I am happy to say that the database auditing constraints are all behind us. The Nessus Database Compliance Plugin now supports not one, not two, but an infinite number of database credentials. Our developers have completely re-architected the plugin from the ground up; the end result is simple and intuitive.
The Nessus database compliance plugin now supports an infinite number of database credentials
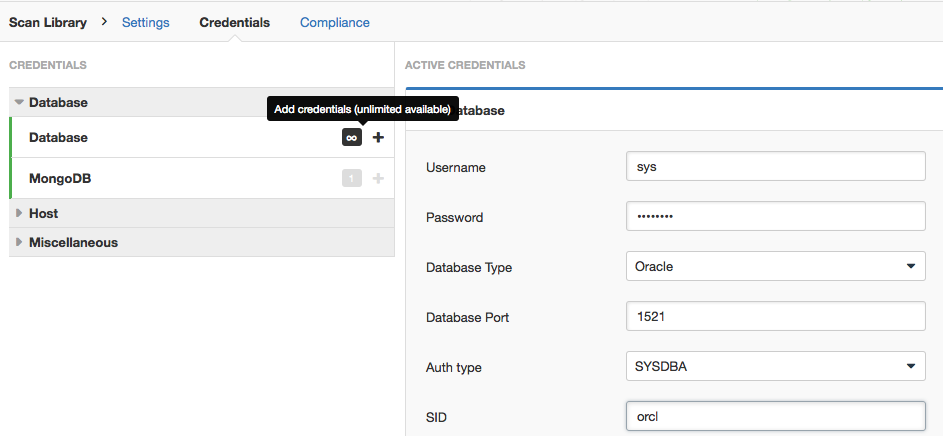
Nessus users will now see one ∞ (infinity) symbol under the database Credentials tab. From there, you can configure any number of database credentials, all within a single scan policy.
What can you do now?
Multiple SIDs/instances in a single policy
This one is obvious: you can now configure an infinite number of database names/SIDs/instances within a single policy.
Multiple database types in a single policy
In addition to multiple SIDs/instances, you can now configure multiple database types in a single scan policy. So for example, if you wanted to audit Oracle, MySQL and SQL Server databases within a single scan, you can do that without creating a separate policy for each database.
Run informational SQL queries
You can now run informational SQL queries from .audit without including sql_expect in the check. This helps you avoid FAIL results when all you want to do is include an SQL result in a Nessus report.
For example:
<custom_item>
type : SQL_POLICY
description : "List Database Users"
sql_request : "select username from dba_users order by username;"
sql_types : POLICY_VARCHAR
</custom_item>Sample result
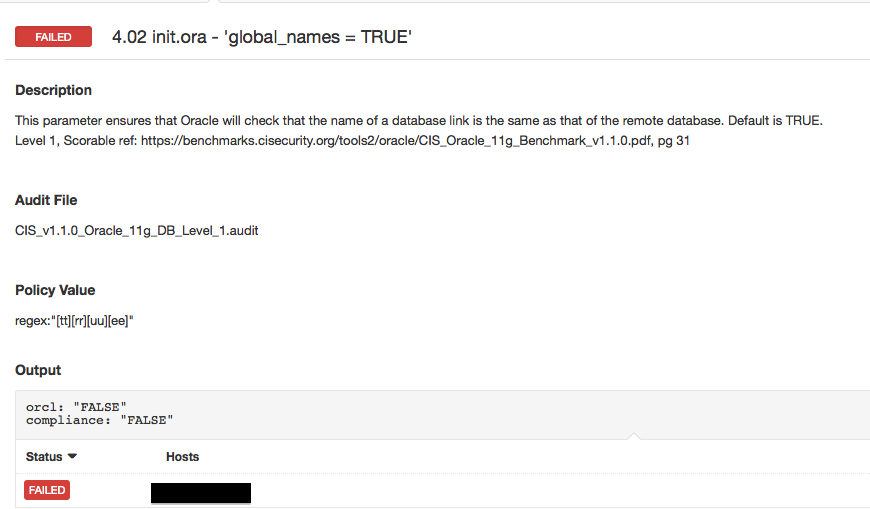
Here’s a sample result from a scan with the updated Database Compliance Plugin. Notice that multiple SIDs are now reported under a single check (orcl, compliance).
Hopefully you are now convinced that Nessus v6.3 is worth your time. Go ahead, give it a try, take it for a spin and let us know what you think. We welcome your feedback to make our products even better.
Learn more
- Plugins
- Vulnerability Management



Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success