by Cesar Navas
With the growing number of threats against network infrastructures, many organizations still do not have an adequate patch management system in place. This can leave critical systems unpatched and vulnerable for a significant period of time. The ISO/IEC27001 dashboard provides security teams information on outstanding vulnerabilities, mitigation progress, and opportunities to reduce risk.
The ISO/IEC 27001 framework establishes guidelines and general principles for initiating, implementing, maintaining, and improving Information Security Management Systems (ISMS). Each security control and objective provided within the standard can be tailored to specific business and regulatory objectives, and assist with maintaining overall compliance. This dashboard provides organizations with information which specifically measures against the compliance standards related to ISO/IEC 27001. The International Organization for Standardization (ISO) and the International Electrotechnical Commision (IEC) formed the specialized system for worldwide standardization. The Standard specifies the requirements for establishing, implementing, maintaining, and continually improving an information security management system within an organization. ISO/IEC 27001 is part of the ISO 27000 family of standards that addresses various aspects of information security.
By following the guidelines and requirements outlined in ISO/IEC 27001 organizations can establish a robust information security management system that helps protect valuable information assets and manage associated risks effectively. The standard provides a structured framework for continuous improvement in information security practices and resilience against potential threats.
This dashboard assists organizations in detecting critical severity vulnerabilities, exploitable vulnerabilities, remediation progress, and vulnerability related events. Several components provide information on outstanding vulnerabilities, which security teams can use to target remediation efforts. Indicators will detect exploitable vulnerabilities from common applications, web servers, cloud services, and more.
Tenable provides several solutions for organizations to better understand vulnerability management. Security leaders need to SEE everything, PREDICT what matters most and ACT to address cyber risk and effectively align cybersecurity initiatives with business objectives. Tenable Vulnerability Management (formerly Tenable.io) discovers and analyzes assets continuously to provide an accurate and unified view of an organization's security posture. The requirements for this dashboard are: Tenable Vulnerability Management.
Widgets:
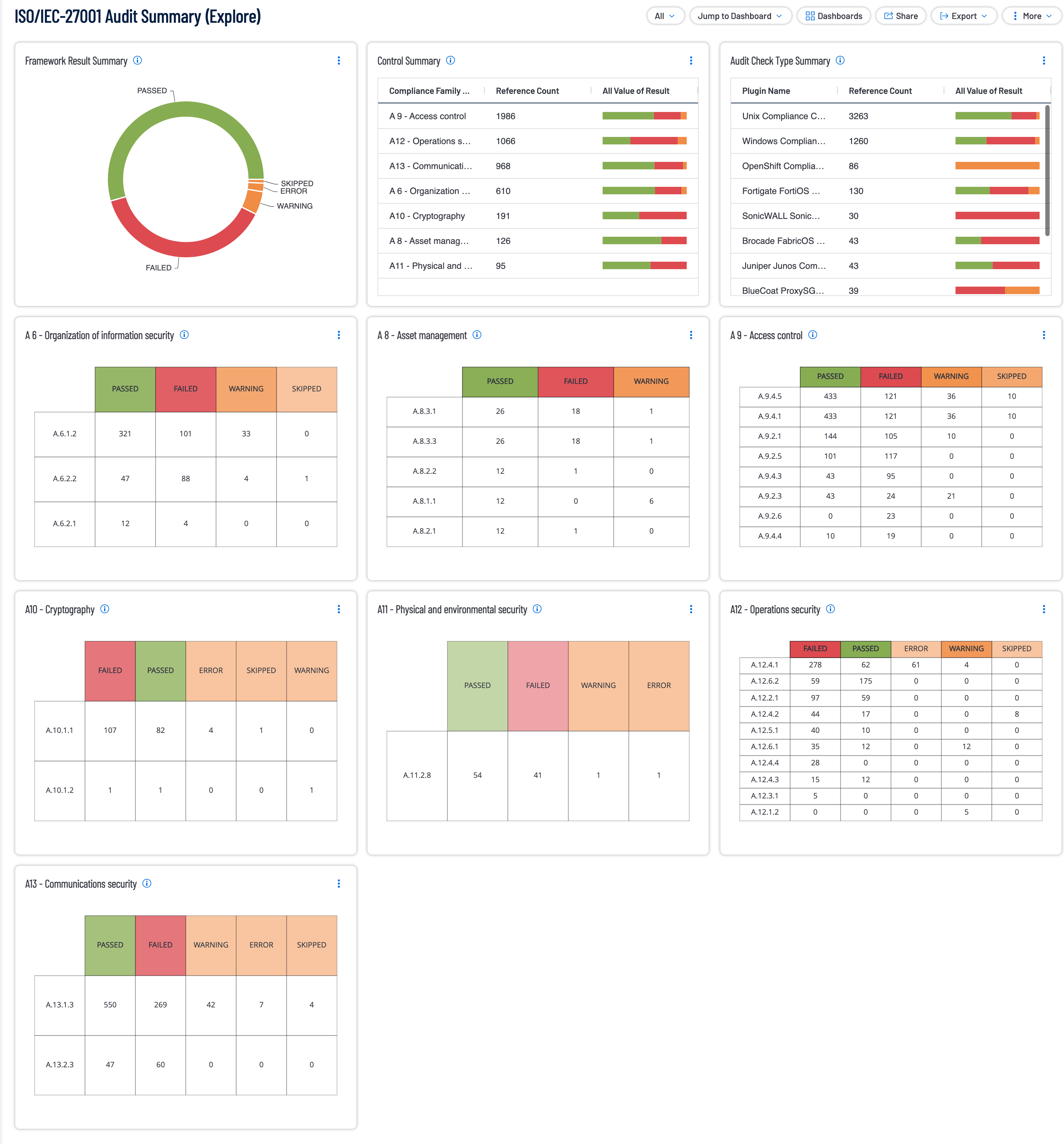
- Framework Result Summary: This chapter summarizes all the families outlined in the
- Control Summary: This chapter provides compliance results for each control family within the compliance standard.
- Audit Check Type Summary: This chapter provides compliance results for hosts within the compliance standard.
- A 6 - Organization of information security: This chapter provides organizations with information which specifically measures against the compliance standards related to ISO/IEC 27001. The vulnerability data presented in this chapter is from annex A6 Organization of Information Security.
- A 8 - Asset management: This chapter provides organizations with information which specifically measures against the compliance standards related to ISO/IEC 27001. The vulnerability data presented in this chapter is from annex A8 Asset Management.
- A 9 - Access control: This chapter provides organizations with information which specifically measures against the compliance standards related to ISO/IEC 27001. The vulnerability data presented in this chapter is from annex A9 Access Control
- A10 - Cryptography: This chapter provides organizations with information which specifically measures against the compliance standards related to ISO/IEC 27001. The vulnerability data presented in this chapter is from A10 Cryptography.
- A11 - Physical and environmental security: This chapter provides organizations with information which specifically measures against the compliance standards related to ISO/IEC 27001. The vulnerability data presented in this chapter is from A11 Physical and environmental security.
- A12 - Operations security: This chapter provides organizations with information which specifically measures against the compliance standards related to ISO/IEC 27001. The vulnerability data presented in this chapter is from A12 Operations security.
- A13 - Communications security: This chapter provides organizations with information which specifically measures against the compliance standards related to ISO/IEC 27001. The vulnerability data presented in this chapter is from A13 Communications security.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success