by Josef Weiss
Malware presents a risk to any organization and comes packaged in many forms. Malware can exploit weaknesses and vulnerabilities to make software or hardware perform actions not originally intended. Vulnerabilities can also be widely exploited shortly after publication as malware authors reverse engineer the fix and develop "1-day exploits" that can be used to attack organizations. Tenable.io easily identifies assets most vulnerable to malware and other exploitation frameworks. This report provides the necessary context to understand which assets are vulnerable to malware. Organizations can better communicate cyber risk to the business by supplying context and associated metrics.
Organizations can use the report to gain operational awareness of assets on the network with exploitable vulnerabilities. Analysts need to prioritize vulnerability remediation or mitigation, depending on risk. Focusing on vulnerabilities that are actively being exploited by malware helps to reduce the risk to the organization and provides guidance on which vulnerabilities to remediate first.
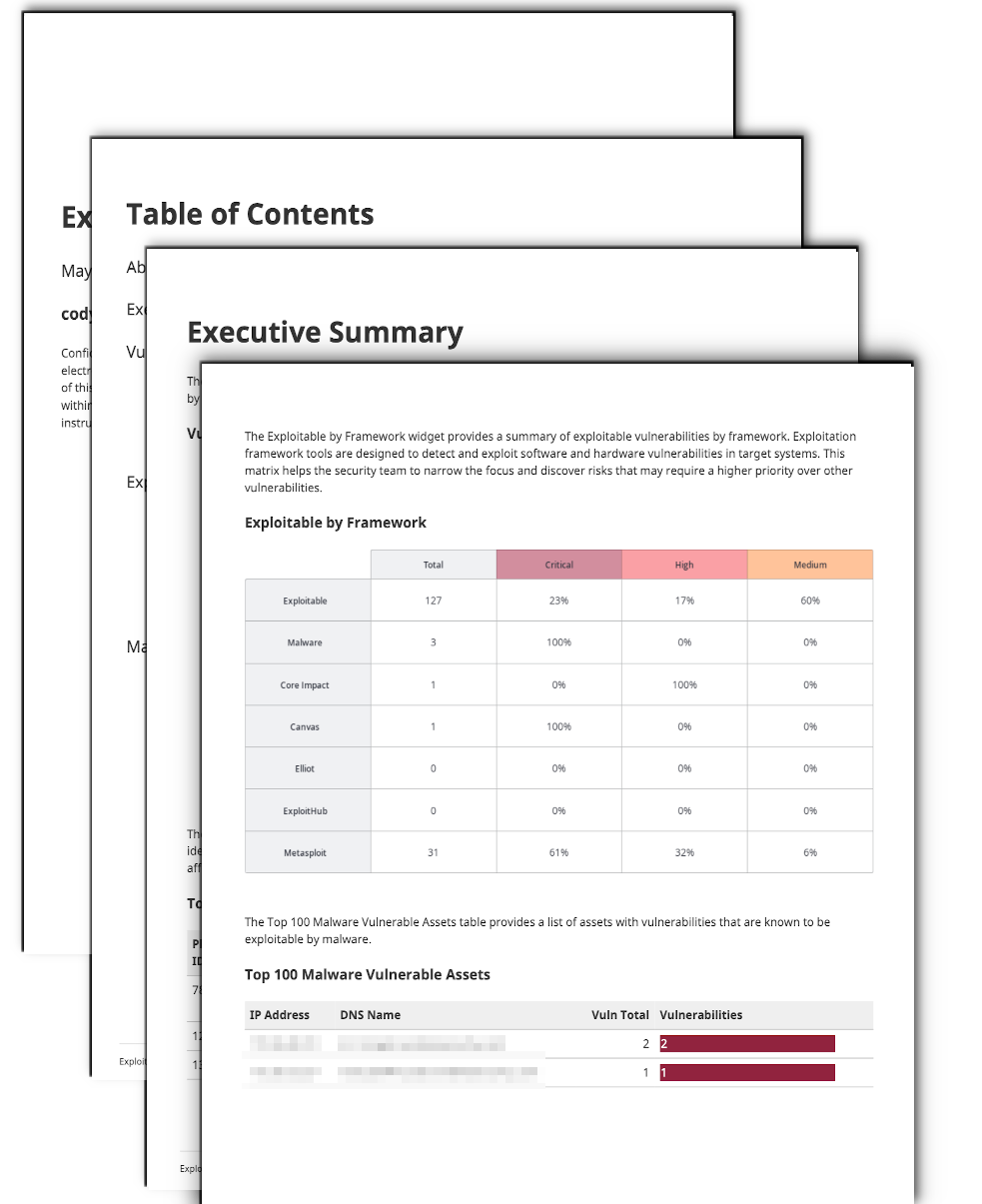
Vulnerabilities can also be exploited through common software applications. Frameworks such as Metasploit, Core Impact, and exploits listed in ExploitHub can be used by anyone to perform attacks against vulnerabilities. Vulnerabilities that can be exploited through these means are highlighted in this dashboard.
Modern ransomware and malware can be initially developed with the assistance of an exploit framework. This report provides executives and administrators alike insight into how vulnerable their network is to attacks by such frameworks.
Security leaders need to SEE everything, PREDICT what matters most and ACT to address cyber risk and effectively align cybersecurity initiatives with business objectives. Tenable.io discovers and analyzes assets continuously to provide an accurate and unified view of an organization’s security posture.
Chapters
Exploitable by Malware - This chapter presents a summary of the top 100 vulnerabilities that have been identified to be exploitable using malware.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success