by Josef Weiss
Organizations using Tenable.io gain a tremendous amount of details such as vulnerabilities, software used, and hardware supporting the environment. Tenable.io provides valuable insight into systems throughout the Cyber Exposure Lifecycle. Analysts are provided with common visibility to discover, assess, analyze, and fix vulnerabilities quickly and efficiently to protect the organization. With any piece of software or hardware, Tenable.io needs to be properly configured to ensure the best scan results are returned to the analyst. Each organization is going to have different methods of account management and what Tenable.io can use to SSH (secure shell) into systems.
Within the Assess phase of the security lifecycle, analysts create scans within Tenable.io for many tasks such as compliance, Windows patch verification, or general vulnerability scanning. Within scans for Linux/Unix based systems, analysts can configure the scans to use SSH username/password credentials. Configuring the scans to use SSH credentials allows Tenable.io to gather detailed information of the system.
If a Tenable.io scan is configured with SSH credentials for a regular user account, basic information about a system can be retrieved. However, a SSH scan can be provided to a regular user account along with credentials to “su/sudo”. The “su/sudo” SSH credentials allow the user to gain higher privileges into the system with an administrator or root account.
When Tenable.io attempts to connect to a system with SSH, the first set of credentials are used to make a connection. After the scanner establishes a session using SSH, Tenable.io will try to elevate privileges with “su/sudo” to retrieve further information off the system. If Tenable.io is unable to perform this action, plugin 12634 will report that the attempt to elevate permissions was unsuccessful.
This report identifies scans that used plugin 12634 with the specific failure message within the plugin output. With this report, analysts can identify systems that did not have adequate permissions to do in-depth scanning of systems with SSH username/password credentials. Along with each system identified with this plugin, the details of the plugin are provided to further assist analysts in remediating the SSH credential issue. To ensure there is no confusion, this report only addresses “su/sudo” failures when Tenable.io attempts to elevate privileges from a scan. This report does not address attempts from users who try to elevate privileges with “su/sudo” and are unsuccessful.
Tenable.io is the first solution in Cyber Exposure to provide the key risk metrics businesses need to measure risk exposures. Identifying elevated privilege failures due to errors or misconfigured credentials is critical in maintaining continuous visibility into assets. Once these failures are identified, analysts can remediate the issues and continue to accurately communicate cyber risk to the business.
Chapters
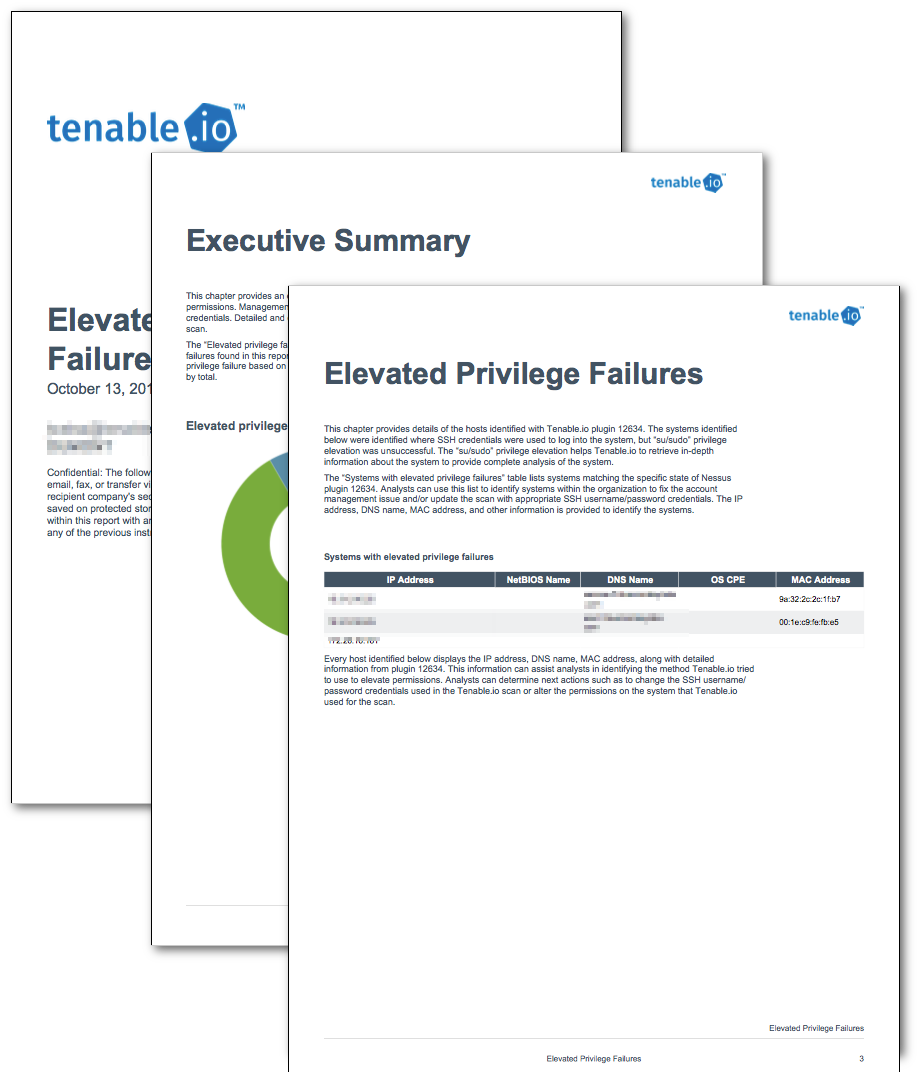
Executive Summary - This chapter provides an overview of systems detected in the organization that could not elevate SSH permissions. Management and analysts can quickly see the impact of systems scanned without proper SSH credentials. Detailed and complete analysis can be performed with appropriate SSH credentials within the scan.
Elevated Privilege Failures - This chapter provides details of the hosts identified with plugin 12634. The systems identified below were identified where SSH credentials were used to log into the system, but “su/sudo” privilege elevation was unsuccessful. The “su/sudo” privilege elevation helps Tenable.io to retrieve in-depth information about the system to provide complete analysis of the system.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success