Operational Technology (OT) Security: How to Reduce Cyber Risk When IT and OT Converge
Eliminate IT and OT Cybersecurity Silos to Find Threats and Stop Potential Attacks
Operational technology (OT) has been a part of manufacturing, utilities and other industries since the late 1960s. For much of that time, users considered the technology "safe" from attacks because most OT devices weren’t connected to outside networks.
However, in today’s modern industrial and manufacturing facilities, air-gapping is no longer effective, increasing the likelihood of cyberattacks.

There have been documented attack cases that impact nearly every manufacturing vertical and critical infrastructure environment imaginable.- White Paper: Prediction of an OT Attack
In manufacturing, for example, OT assets are used in both discrete manufacturing such as automobile production and the pharmaceutical industry, and continuous manufacturing such as water purification and oil production. In these settings, programmable logic controllers (PLCs) or distributed control systems (DCSs) control OT devices
Historically, these devices were physically separated from networks through air-gapping, a security measure to prevent OT devices from connecting to anything else or being exposed to the outside world.
But today, a convergence of OT and IT devices, along with an increasing dependency on the internet of things (IIoT), means air-gaps are no longer sufficient to keep OT environments safe.
Now, a cyberattack that begins in an IT network can easily traverse into an unsecured OT environment, pushing cybersecurity teams to give OT environments increased attention.
This knowledge base outlines OT cybersecurity challenges and solutions to create a better understanding of OT-related cyber risks and provides recommendations about how to keep your organization safe in this ever-changing and rapidly evolving converged IT and OT world.
Learn more about:
Industrial Cybersecurity for Modern OT Environments
An increasing convergence between IT and OT creates new challenges and risks for industrial cybersecurity. Take a closer look at these challenges and how to mitigate OT security threats.
Learn MoreTenable Connect community for operational technology
Maintaining cybersecurity for operational technology isn't the same as traditional IT security. Need help? Tenable Connect is the No.1 place to talk about OT, ask questions and share tips.
Learn MoreFrequently Asked OT Questions
Do you have questions about industrial cybersecurity, operational technology or how to keep your OT environment secure? Check out these frequently asked questions.
Learn MoreHow to Choose the Right OT Security Solution
Are you considering purchasing an OT security solution? Not sure where to start or which is best for your organization? Check out these 6 core questions to consider.
Learn MoreEnd-to End OT Visibility and Other OT Blogs
End-to-end visibility and risk prioritization for all assets are key to securing your converged IT/OT environment. Learn more about the role of exposure management and other important topics in these OT blogs.
Learn MoreOT 2-Minute Quick Tips
Got two minutes? In these videos, learn more about automated OT asset discovery, industrial control planes, industrial controllers and more, all in just two minutes.
Learn MoreTenable OT Security: Unified IT/OT Security
Protect Your Industrial Network From Cyber Threats, Malicious Insiders and Human Error
Tenable OT Security can help you identify threats and predictively prioritize cybersecurity risks and other security vulnerabilities to maximize the safety and reliability of your modern OT environment.
Tenable OT Security delivers:
- Complete visibility into your converged attack surface
- A multi-detection engine that discovers high-risk events and activities that may impact your OT environment
- Visibility into your infrastructure from network down to individual device level
- Predictive Prioritization for every asset in your ICS network so you can find vulnerabilities and understand risk level
- Tracking for user-based changes or malware across your network or on a device
Industrial Cybersecurity for OT Environments
Industrial controllers are a focal point for attacks on industrial operations and critical infrastructure. So, how do you keep your ever-expanding attack surface safe?
Tenable OT Security offers a comprehensive security solution for IT and OT security. It can help protect your industrial networks from threats, malicious insiders and other risks with capabilities such as:
- 360-degree visibility into converged IT/OT environments and industrial control systems (ICS) activity
- A multi-detection engine that discovers high-risk events and behaviors that threaten your organization
- Automated alerts for policy violations and detection of deviations from your network traffic baseline
- Signature updates that use crowd-sourced data to discover new attacks
- Passive detection and patented active querying to find threats to your network and OT devices
- Up-to-date and detailed inventory list with risk data to help you prioritize vulnerabilities and plan maintenance
- Configuration control with reports about changes to OT assets including programmable logic controllers (PLCs), distributed control systems (DCSs) and human-machine interfaces (HMIs).
Mind the Gap: A Roadmap for IT/OT Alignment
In your OT environment, your OT devices are increasingly connected, thereby creating new challenges in securing your industrial network. Air-gaps alone are no longer effective because today's industrial attack surface now encompasses both IT and OT. This makes lateral attacks a growing threat. If attackers find a weak link on either side, they can use it as a gateway into your entire organization, quickly gaining access to both information and operations.
An integrated IT/OT security strategy can detect attacks earlier and help your team more effectively identify, investigate and address vulnerabilities and threats across your attack surface.
This white paper explores:- How OT and IT are increasingly converging
- What’s happening in your expanding attack surface and attack vectors
- Issues contributing to a disconnect between IT and OT security practices
- Security and compliance best practices for industrial networks
- Benefits of a converged IT/OT security strategy
Accidental Convergence: A Guide to Secured IT/OT Operations
Operational technology plays an important role in critical infrastructure and industrial environments. In addition to routers, servers, computers and switches used in traditional IT environments, to operate plants and factories, industries also use OT devices such as distributed control systems (DCSs), programmable logic controllers (PLCs), and human-machine interfaces (HMIs).
While threats that begin in IT can laterally move into your OT environment, OT threats aren’t necessarily the same as IT security risks. Because of this, you need different security tools and operating policies to secure your OT environment.
This white paper explores:
- What’s fueling IT/OT convergence
- Why air-gapping OT systems is not effective
- What accidental convergence is and what can happen
- Threat actors looking to infiltrate your systems
- How you can plan ahead for OT security including more visibility, better situational analysis and reduction of cyber risk
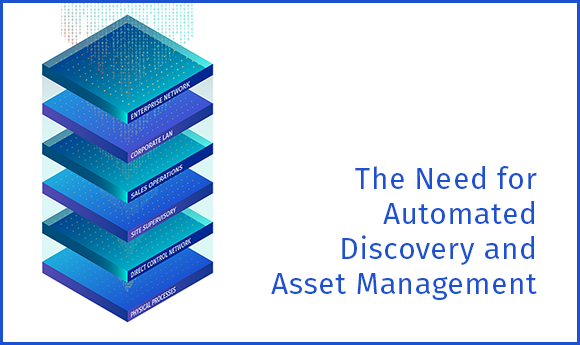
Top Three Use Cases for Automated OT Asset Discovery and Management
Most ICS networks lack basic security controls and the ability to automatically manage assets like you’d find in more traditional IT environments.
Unfortunately, attackers know this and that’s why ICS networks are increasingly under attack.
As your organization looks for ways to defend your ICS systems, automated asset discovery and automated asset management are critical. If you don’t have an up-to-date and accurate ICS asset inventory, you can’t effectively manage OT risks. If you don’t know your risks, you can’t secure your environment.
As your ICS network grows and your IT and OT networks continue to evolve, effective asset management is an increasingly important component of your overall cybersecurity strategy.
This white paper explores:
- Incident response strategies
- How to decrease resolution time and ensure operational continuity
- Compliance with key industry regulations
Critical Infrastructure Cybersecurity: Actively Secure Your Industrial Environment in the New Era of Distrust
Within your industrial control system environment, if you’re using network monitoring only, you may miss a device attack. Network monitoring only gives you about 50% visibility into your converged IT/OT environment and those blind spots put you at risk for being infected for days — or even months — without your knowledge.
Effective OT cybersecurity is more than network monitoring. By adding device-based security measures to your exposure management program, you’ll have better situational awareness about your actual cyber risks so you can plan remediation and defense strategies accordingly.
This white paper explores how to:
- Improve controller integrity by quickly discovering device changes made through physical connections
- Discover assets, even those that don’t communicate over your network
- Maintain “last known good state” data so you can enable holistic back-up and recovery strategies
- Monitor all routable components of your network
Tenable Connect community: Your go-to resource for OT
The Tenable Connect community is a place to share common interests in OT security and exchange ideas. Tenable Connect is a great resource to help you make the most of your Tenable products and access fresh ideas about how to keep your OT environment secure.
Avoid Scanning Fragile Devices
There are many fragile devices on each network that cannot be included in active scanning, due to the sensitive nature of such devices. Operational Technology (OT) is the most common category of sensitive devices.
Read MoreSecuring Operational Technology from Cyberattacks
Threat actors are increasing attacks on water and wastewater systems (WWS). These attractive OT targets are complex to protect.
Read More3 Ways to Handle Insider Threats in OT Infrastructure
With blurred lines between IT and OT, the newest threat may come from where you least expect it — inside your organization.
Read More6 Questions to Ask When Choosing an OT Security Solution
When it’s time to choose an OT cybersecurity solution, you want to know if you’re choosing one that meets all of your organization’s unique and specific requirements and if it’s flexible and scalable for future requirements you may have.
To reduce exposures in your OT environment, the solution you choose should support your specific OT devices, including non-disruptive asset discovery (even in older network assets), alerts on critical vulnerabilities, and support for secure OT/IT alignment.
Knowing the right questions to ask upfront can prevent future headaches and ensure you choose the best solution to secure your OT and IT environments. Here are six important questions to consider when evaluating OT security solutions:
-
Is it vendor-agnostic?
The solution should support all of your protocols and specific devices.
-
Does it provide multi-detection methods?
The solution should provide coverage both to the network and devices on the network.
-
Does it detect and alert on known common vulnerabilities and exposures?
A platform that incorporates known CVE discovery into your security policy will provide faster detection.
-
Does it provide IT support in addition to OT?
The solution should work in conjunction with your already-deployed IT security products such as your security information event management (SIEM) tool, next-generation firewalls (NGFWs) and diode-based firewalls.
-
Does it support secure IT/OT alignment?
Each environment needs purpose-made solutions.
-
Is it designed to live in an OT environment from a hardware or operating environment perspective?
Your solution should be configurable to meet your network and physical architecture requirements.
Trends That Impact OT Security
Whether intentional or accidental, there are several trends increasing attack vectors across OT environments. Here are some common OT trends and how they can impact your organization:
-
Purposeful convergence of IT/OT
By uniting IT and OT and eliminating siloed infrastructures, you may reduce costs and improve operational efficiencies.
-
Accidental convergence of IT/OT
If your organization doesn’t have a convergence strategy, but your employees use IT assets (such as laptops, thumb drives etc.) in OT environments, it can inadvertently create an accidental IT/OT convergence that increases organizational risks.
-
Industry 4.0
Industry 4.0 includes the introduction of IoT tech used to monitor and/or control OT environments and/or assets.
-
Increased collaboration
IT and OT teams are collaborating with each other more than ever before. Information and expertise silos are beginning to come down and, in some cases, IT and OT function on the same team.
Because today's cybercriminals can attack from all sides — and attacks laterally creep across IT to OT and vice versa — keep an eye on these trends to ensure comprehensive OT security.
Unprecedented Situational Awareness for Your Entire OT Environment
Tenable OT Security protects your industrial network from malicious insiders, cyber threats and human error. The solution provides deep situational awareness about all the threats that put your OT network at risk so you can maximize the visibility, security and control of your operational technology environment.
Tenable OT Security Blog Bytes

Building Resilient OT Environments: Safeguards for Electric Utilities
One in 10 cyberattacks around the world in 2022 targeted energy organizations, making it the fourth most-attacked industry. With this growing number of attacks on critical infrastructure, it's important to understand how attackers can take advantage of industrial control systems and the role vulnerability management best practice plays in reducing risk, mitigating damage and preventing the shutdown of essential services.

How to Tackle OT Challenges: Asset Inventory and Vulnerability Assessment
With the convergence of IT and OT devices in industrial environments, comprehensive asset discovery and vulnerability identification and remediation is complex and challenging. In many environments, most OT systems are legacy, customized, or proprietary, which increases cyber threats and complicates mitigation. Responsive and accurate vulnerability detection requires active monitoring and querying of all of your OT devices.

Operational Technology in the DoD: Ensuring a Secure and Efficient Power Grid
To uphold its national defense mission, the U.S. Department of Defense depends on critical infrastructure to manage everything from illuminating command centers to fueling advanced weapons systems. At the heart of this infrastructure are OT devices, including the hardware and software necessary to monitor and control physical processes and systems like the power grid. Unfortunately, the power grid is vulnerable to cyberattacks, and the consequences of an attack could be dire.

Navigating Security Challenges Around OT in the DoD’s Manufacturing Lines
Operational technology has a direct impact on the Department of Defense's manufacturing lines and can play a vital role in improving supply chain management and logistics. As DoD (DoD) integrates OT devices into the Defense Industrial Base (DIB), it introduces new cyber risks and security challenges. Yet, ensuring OT system security is paramount to mobilization, deployment and the sustainability of military operations.

How To Secure Your IT, OT and IoT Assets With an Exposure Management Platform
To stay ahead of today's evolving threat landscape, especially in converged IT/OT environments, your organization needs end-to-end visibility and the ability to prioritize risk across all of your assets — IT, OT and IoT. An exposure management platform like Tenable One enables comprehensive visibility that's critical to ensuring your teams can monitor, analyze and safeguard every component of your digital infrastructure effectively.
OT Security On Demand
Experts Share Ways To Improve Manufacturing Sector IT/OT Security
Manufacturers are facing increased cyber attacks, and evolving cyber threats can negatively impact the factory floor, making it challenging to mature your cybersecurity posture and ensure operational resilience. This webinar explores steps you can take to improve both and avoid becoming a target of a cyberattack.
Learning more about
- Common manufacturing security challenges
- Best practices to mature your cyber hygiene
- Best practices to mature your cyber hygiene
- Lessons learned from recent cyber incidents
Ops or Security? Who Should Own OT Security And Why?
As OT cybersecurity becomes increasingly complex, it can quickly shift OT security responsibilities within your organization. Without a clear plan that details who is responsible for what, you can quickly and unintentionally increase cyber risk. This webinar explores steps you can take to evaluate and mature your existing OT security practices, with insight from industry experts.
Learn more about:
- Why and how to take control of your OT security
- Why OT security is challenging
- Insights from a recent GigaOm Radar for Operational Technology (OT) Security report
- Takeaways from real-world issues that affect IT-OT attack surfaces
OT Security Trends – From the Boardroom to the Industrial Floor
Critical infrastructure faced a range of new and updated cybersecurity regulations in 2023, leading many organizations to rapidly increase their adoption of OT/ICS security best practices. Moving forward, however, new trends also require the same intense focus. This webinar explores recommendations from OT/ISC security experts about these trends and how you can address them.
Learn more about:
- New OT/ICS attack methods and defense measures
- Changes in the cyber insurance market evolving from new regulations
- Which business drivers increase OT/IoT/IIoT adoption
Understanding Key Principles, Challenges and Solutions of Securing OT and Industrial Control Systems
Cybersecurity professionals understand how important it is to ensure IT devices are protected from cyber risk; however, they can overlook OT and industrial control system (ICS) security. This webinar, which features ICS security experts, takes a closer look at OT/ICS security best practices.
Learn more about:
- Unique OT assets and IT/OT convergence complexities
- How to assess OT threats, including new risks
- Best practices to manage OT cybersecurity
- How to decrease the impact of an OT attack
- Basics for a robust OT/ICS security program
2-Minute Quick Tips for Operational Technology Security
The Need for Automated Asset Discovery
If you don’t know which assets exist within your OT environment, you can’t protect them. This video explores how Tenable OT Security's automated asset discovery tools will help you overcome challenges created by using a mix of manual processes for asset discovery and management. In two minutes, learn how Tenable OT Security:
- Reduces manual labor, time and expense
- Improves your incident response and recovery processes
- Increases program accuracy and efficiencies
- Addresses compliance requirements
- Helps you implement a reliable and effective vulnerability management process
The Importance of the Industrial Control Plane
ICS networks employ two types of protocols: data plane protocols to manage physical parameters for ongoing processes and control plane protocols to manage engineering activities. In just two minutes, learn:
- Why your industrial control plane (ICP) is difficult to monitor
- How a lack of security controls impacts your industrial control plane
- What potential problems can arise when you don’t monitor your ICP
- How Tenable OT Security can help
Why Industrial Controllers are the Most Important Assets to Protect in ICS Networks
Controllers are the brains of your industrial network, but they are surprisingly vulnerable. That’s because they were designed decades ago with either few protections or none at all, creating OT security risks, which leave you vulnerable for attacks. In two minutes, learn:
- Why networks are often under-protected
- Who can make changes to logic
- Potentially catastrophic results of continuing operations and safety of malicious or erroneous changes
- How Tenable OT Security can protect against unauthorized changes
Proactive Security on Both Fronts for Industrial Control Environments
Is your OT security solution passive or active? Unless you’re listening to both your network and actively querying devices, you don’t have full protection. Detailed asset inventory and real-time information are critical components of protecting your converged IT/OT environment. In two minutes, learn:
- Why being passive and waiting for threats to appear on your network may be too late
- Where your blind spots may be
- How to safely and effectively gain a comprehensive view across your industrial environment
Top Threats to Industrial Control Systems
Attacks on industrial control systems and critical infrastructure environments continue to increase. If your ICS or infrastructure is compromised, it can cause widespread damage and put lives at risk. Do you know the top threats to guard against? In two minutes, learn:
- Why ICS systems are more vulnerable to attacks today than ever before
- How you can become collateral damage even if your company is not the target
- What kind of threats may exist inside your network
- The top obstacles for securing your controllers
Tenable OT Security: Industrial Grade Security for Your Industrial Systems
In modern industrial and critical infrastructure environments, an increasing number of devices are now connected to your networks, many of which are internet-facing. This changing OT environment means traditional ways of protecting OT devices, like air-gapping or air walls, are no longer effective.
From malicious insiders and human errors, it’s increasingly challenging to effectively discover, investigate and remediate all the threats lurking against industrial and critical infrastructure environments. And because of that, OT attacks are on the rise.
Effective OT security requires complete visibility, security and control over all of the threats that put you at risk. Tenable OT Security is the industry’s first unified, risk-based solution for converged IT/OT environments.
Threat Detection and Mitigation
Use a multi-detection engine to find potential high-risk events on your network and alert your team so they can respond quickly.
Adaptive Assessment
Discover more information than just passive monitoring and get unparalleled visibility into your infrastructure without impacting operations.
Risk-Based Vulnerability Management
With Predictive Prioritization, prioritize risks within your ICS network, to mitigate them before attackers exploit vulnerabilities.
Configuration Control
Get a full history of device configuration changes over time, complete with a back-up snapshot of your last known good state for faster recovery.
Complete Visibility
Measure and manage all your IT and OT risks in a single platform for complete visibility into your converged attack surface, supported by native integration with leading IT security tools.
Enterprise Management
Get clear situational awareness across your distributed environment, complete with reporting, vulnerability management and centralized security.
Frequently asked questions about OT Security
What is operational technology (OT)?
Operational technology (OT) represents all of the hardware and software to manage, monitor and control physical devices and processes. Some OT examples are distributed control systems (DCSs), programmable logic controllers (PLCs) and human-machine interfaces (HMIs) etc. Industrial control systems have used OT for manufacturing, transportation and utilities since the 1960s.
Unlike information technology (IT), OT in those industries was not originally connected to outside networks. These devices were primarily air-gapped (physical isolation from unsecured networks) for security; however, air-gapping is no longer effective in today’s connected world, and vulnerabilities in an OT system can leave critical infrastructure at risk of sabotage.
What is operational technology security?
Operational technology security includes all the measures you can take to protect your organization’s hardware and software to monitor and manage your physical devices and processes from internal attacks, external attacks or other cyber risks.
Historically, OT involved closed systems. In those closed systems, air-gapping (physical isolation from unsecured networks) was the primary form of security. In today’s highly connected environment, OT security solutions include IT/OT security integration, passive and active threat detection, detailed asset inventory, risk-based vulnerability management and configuration control.
What’s the difference between IT and OT?
There are a few key differences between IT and OT. Information technology is used to store, manage, process and protect information, while operational technology is used to manage, monitor, and control physical devices and processes. IT generally has a stable environment, with a focus on security, a short lifecycle with frequent updating and standard operating systems. OT, on the other hand, may operate in adverse environmental conditions, with a focus on uptime. It also has a long lifecycle with infrequent updating and proprietary operating systems.
Traditionally, IT and OT have been separate. However, today, IT and OT are more interconnected than ever before, creating new attack surfaces and requiring new cybersecurity measures to protect both.
What is OT infrastructure?
OT infrastructure refers to physical equipment and processes that operational technology manages, monitors and controls. It is used in a variety of industries including manufacturing, oil and gas, electrical generation and distribution, aviation, maritime and rail, as well as to control critical infrastructure such as emergency services, water treatment plants, electrical grids and traffic management systems. As part of all these industries and services, OT infrastructure is ubiquitous. It includes valves, pumps, switches, generators, pipelines, fans, PLCs, remote terminal units (RTUs), industrial robots and more.
What is industrial security management?
Industrial security management is the processes used to ensure your industrial control systems (ICS) are safe and secure. Security management practices include visibility, security and control elements. Protecting industrial plants involves significantly minimizing potential risks and achieving affordable and minimally disruptive security for all assets, including industrial automation networks. It’s important to design and manage ICS security so it does not conflict with other important requirements such as performance output, uptime, and workforce-friendliness. Securing automation networks is the largest challenge in industrial security management today.
What is ICS security?
Industrial control system security (ICS) encompasses all of the processes, hardware and software used to keep ICS safe and secure. ICS security solutions include detailed visibility, asset inventory, passive and active threat detection, risk-based vulnerability management and configuration control. Industrial control systems are a main component of operational technology. ICS includes different types of devices, controls, systems and networks that manage industrial processes. Maintaining ICS safety to decrease risks from internal and external threats is key to keeping most kinds of industrial operations up and running.
What’s an air-gap?
An air-gap is a physical separation between the OT environment and the rest of the world. No data comes into the OT device from the outside and no data goes out from the OT network.
What is a SCADA system?
A supervisory control and data acquisition (SCADA) system is a control system used to communicate with and collect data from industrial machines, sensors and end devices, often at distributed sites. SCADA then transmits data to computers to process it and make it available to operators and other employees. Your staff can use the analyzed information to make important decisions and quickly control virtually any activity that might occur.
Why is OT security important?
OT security is important because without complete visibility and security for both your OT and IT assets you can’t effectively mitigate your overall cyber risk. The industry relies heavily on automation to ensure high efficiency and minimal down time, while meeting exacting engineering standards. This creates unique and evolving risks for industrial and critical infrastructure organizations. Cyberattacks that target OT, or that begin in IT and laterally move into your OT environment, can destroy your operations, change products and put people’s lives at risk. In addition, the modern level of connectivity between operating technology systems and information technology systems increases your attack surface. Gaps in OT security can lead to a breach that can then be used to access your IT system. A successful attack on IT can disrupt more of your operations and put proprietary information at risk.
What is IT-OT convergence?
IT-OT convergence is the intersection of IT and OT devices and systems within the same environment, whether intentional or accidental. The convergence of OT and IT systems can optimize your production processes, encourage innovation and help your organization become more sustainable. However, it can also increase your attack surface by providing more access points for bad actors to enter your network and disrupt operations. Without complete visibility into all of your assets and security threats, you can’t protect your organization from cyber risks.
Eliminate Blind Spots in Your Converged IT/OT Environment With Tenable OT Security
Get comprehensive visibility into your industrial environment. Actively query your OT devices in their native protocols and get a more complete understanding of your modern attack surface.
- Tenable Nessus
Tenable OT Security
Close OT exposure with the unified security solution for converged OT/IT environments.










Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success