by Josef Weiss
Identifying methods of ingress into the network via wireless access points is crucial to maintaining a successful security program. This dashboard collection utilizes both active and passive methods to identify wireless access points and vulnerabilities found within the environment.
There are many challenges associated with wireless networks. Access point and SSID identification within the organization is one important aspect of monitoring wireless networks. Monitoring wireless vulnerabilities is another. The collection assists in the identification and inventory of wireless access points, and presents wireless related vulnerabilities. The collection assists the analyst in identifying wireless vulnerabilities and understanding wireless configurations within the organization.
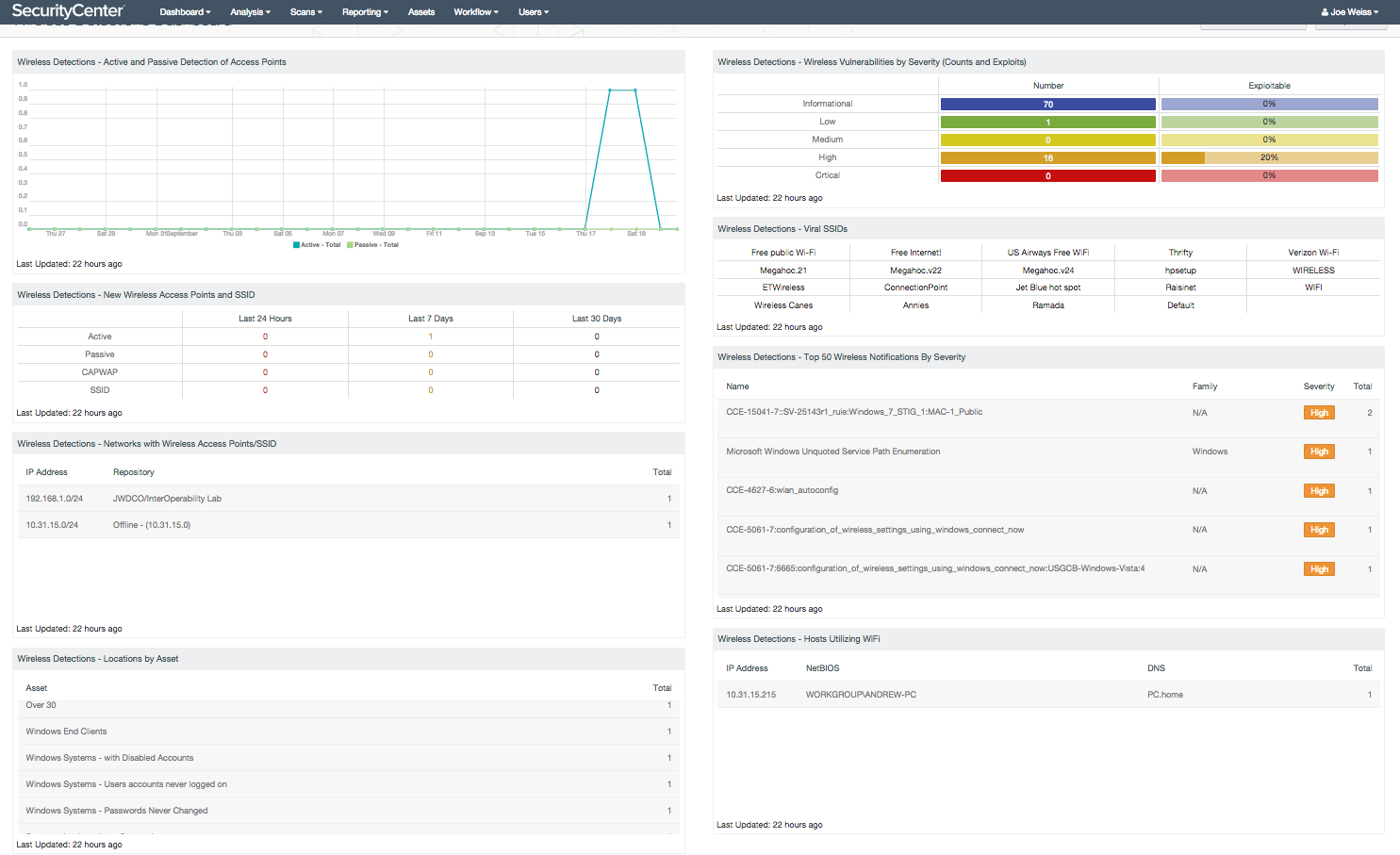
Detecting wireless access points can be a major activity. The collection includes a trend component that displays active and passive wireless access point detections over the previous 25 day reporting period. Spikes in access point counts would identify new or rogue devices. Identifying wireless vulnerabilities is also critical. A severity matrix and vulnerability table is presented that allows the analyst to quickly determine the physical counts of detections by severity, and if any of the detections are exploitable. Also provided is detail on the Top 50 vulnerabilities. This provides the organization with information to quickly identify and mitigate wireless threats.
These tables allow for immediate drill down into the respective severity area for additional details. A table is also included that displays the number of detections by last 24 hour period, last 7 days, and last 30 days, as well as the number of access points by class C address space, which can also assist in the identification of new or rogue access points.
The SSID (Service Set Identifier) is unique name that identifies a wireless network. The Wireless Detections collection also has a component that displays detected active SSIDs present in the environment. For analysis, SecurityCenter displays collected information using Nessus plugin ID 25197 and a text field that can be used to highlight any matching SSIDs. Lastly, a matrix that indicates CAPWAP protocol, client and server detection is included.
SecurityCenter CV scales to meet future demand of monitoring virtualized systems, cloud services, and the proliferation of devices. Nessus is continuously updated with information about advanced threats, zero-day vulnerabilities, and new types of regulatory compliance configuration audits. PVS provides deep packet inspection to enable discovery and assessment of operating systems, network devices, hypervisors, databases, tablets, phones, web servers, cloud applications, and critical infrastructure. Combined, SecurityCenter CV’s continuous network monitoring is able to detect systems, applications, software, and events across the enterprise.
The dashboard and its components are available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The dashboard can be easily located in the SecurityCenter Feed under the category Discovery & Detection.
The dashboard requirements are:
The requirements for these dashboards are:
- SecurityCenter 5.0.0
- Nessus 6.4.2
- PVS 4.2.1
This collections includes the following components:
- Wireless Detections - Active and Passive Detection of Access Points - The Active and Passive Detection of Access Points chart displays a trend over the last 25 days of all wireless access points detected actively or passively. Filtering is accomplished by plugin ID and vulnerability text for both passive and active detections over a 24-hour period, trending for 25 days. Spikes in trend activity for active detections usually depict when active Nessus scanning on the network has occurred, while passive detections occur immediately when devices are detected by Tenable’s Passive Vulnerability Scanner.
- Wireless Detections - New Wireless Access Points and SSID - The New Wireless Access Points and SSID indicates on triggers from active and passive detection type plugins, by plugin ID, and vulnerability text. Data displayed displays the number of wireless access points detected over time. Indications are filtered by time, into columns for the last 24 hours, last 7 days and last 30 days. If no indication is present for the specified time period, zero is shown. If an alert is present, the indication changes to the number of access points discovered. The analyst may click on the indicator to retrieve further details on the number of access points discovered during the scan.
- Wireless Detections - Networks with Wireless Access Points/SSID - The Networks with Wireless Access Points/SSID table displays detections by count of Wireless Access Points detected by active scanning, and presents the count by Class C address space. The table quickly allows the analyst to determine the physical counts of wireless access points by Class C address space within the organization. This allows the analyst to determine if any access points are outside of any specified address space. This table allows for immediate drill down for a more detailed view.
- Wireless Detections - Locations by Asset - The Location by Asset table lists Nessus plugin 25197 – Windows Wireless SSID Detection result totals by SecurityCenter asset names. In SecurityCenter, hosts can be grouped by a large number of criteria including network location. To use the table efficiently, it would be prudent to ensure that asset names representing network locations include some indicator if they are within a known WLAN network range.
- Wireless Detections - Wireless Vulnerabilities by Severity (Counts and Exploits) - The Wireless Vulnerabilities by Severity matrix component presents a severity and vulnerability summary that allows the analyst to quickly determine the physical counts of detections by severity and if any of the detections are exploitable.
- Wireless Detections - Viral SSIDs - This Viral SSIDs matrix derives its list of interesting SSIDs from an article published in 2008 titled: Study shows viral SSIDs could be creating a massive wireless botnet. Reading about ad hoc wireless networks and recommended Windows related configuration settings is very interesting and the topic is made even more interesting by attempting to find the relevant settings mentioned in published hardening guides. The matrix is a convenient way to provide a grouping of interesting SSIDs as reported by plugin 25197. After a wireless site survey, you may wish to repurpose the matrix to list other interesting SSIDs not broadcast by your organization. Please take into consideration that the SSID filtering performed by the dashboard components is case insensitive.
- Wireless Detections - Top 50 Wireless Notifications By Severity - The Top 50 Wireless Notifications By Severity table component displays a list of the Top 50 most prevalent detections using the vulnerability summary tool, sorted by total. The table presents the analyst with a method to view detections in a readable format. Detections that are the most common are listed at the top of the table and are sorted in a descending order. The plugin ID, name, family and severity rating are also displayed for the analyst. Detections are listed by using a filter for the “wireless” keyword contained within the vulnerability text. This may or may not represent an actual vulnerability associated with a wireless AP, but will represent any possible wireless related vulnerability.
- Wireless Detections - Hosts Utilizing WiFi - The Hosts Utilizing WiFi table component utilizes data from Nessus plugin 24272, Network Interface Enumeration, and filters for the term “wireless” to display hosts that have active wireless interfaces. Plugin output displays the network interface details, including the MAC address and IP address.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success