Modern web servers can host a multitude of services on a single server. As more services on a web server are installed, the attack surface becomes a bigger target. This dashboard displays a comprehensive collection of plugins that have detected web vulnerabilities in the organization.
Organizations are finding ways to better utilize existing hosts to offer more services to their customers. Over time, neither administrators nor analysts may know or remember about the various roles, such as file transfer or database services, running on the web servers. The default installations of a new application on a web server can install more services than expected, such as database, software update, or file transfer services. This dashboard helps analysts identify many potential services that may be installed on a host. Once services such as CGI or databases are identified, analysts can determine vulnerabilities associated with those services. As vulnerabilities are detected, remediation efforts can be performed to reduce the risk in the organization.
Many web technologies can integrate easily with other services to provide a complete stack of technologies. For example, a common configuration on a Linux host is a “LAMP” stack, which consists of a Linux host and Apache hosting PHP with a MySQL database. These technologies integrate well and allow for developers to quickly spin up a stack to test complex web services. However, a quick and easy installation may install older versions of each software product. Also, whoever performed the quick and easy software installation may not know of the integration of Apache, MySQL and PHP on the Linux host. The host could also host a forum software package such as vBulletin.
Asset management is a vital piece of a mature organization that helps administrators and analysts track software and hardware in an organization. If analysts knew of all of the software packages and versions in the environment, tasks such as vulnerability remediation would be an easier task. This dashboard assists analysts in identifying various web applications and services in the organization. Not all possible web applications and services are represented in the dashboard, but many popular ones are listed. Using the information in this dashboard, analysts can better prepare and react to vulnerability disclosures and patch releases.
The dashboard and its components are available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The dashboard can be easily located in the Tenable.sc Feed under the category Monitoring. The dashboard requirements are:
- Tenable.sc 4.8.2
- Nessus 8.6.0
- NNM 5.9.0
Tenable provides continuous network monitoring to identify vulnerabilities, reduce risk and ensure compliance. Tenable's family of products includes Tenable.sc Continuous View (CV), Nessus and Nessus Network Monitor (NNM). Tenable.sc CV performs log normalization from hundreds of unique data sources. Nessus is the global standard in detecting and assessing network data. NNM provides deep packet inspection to continuously discover and track users, applications, cloud infrastructures, trust relationships, and vulnerabilities.
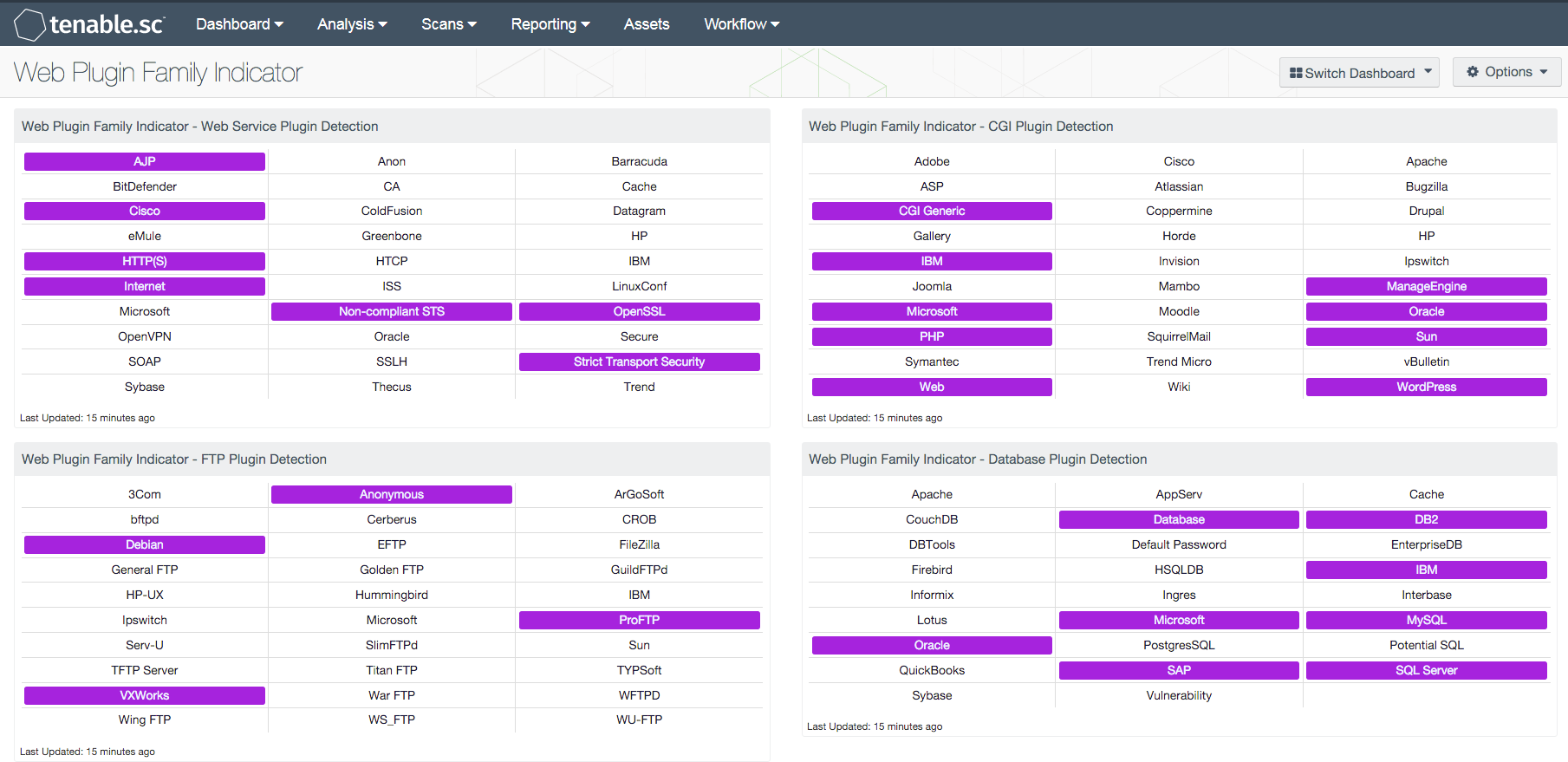
This dashboard contains the following components:
- Web Service Plugin Detection: The “Web Service Plugin Detection” component displays a comprehensive collection of potential web services
- FTP Plugin Detection: The “FTP Plugin Detection” component displays a comprehensive collection of potential FTP services in the organization
- CGI Plugin Detection: The “CGI Plugin Detection” component displays a comprehensive collection of potential CGI services in the organization
- Database Plugin Detection: The “Database Plugin Detection” component displays a comprehensive collection of potential database services in the organization
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success