The Verizon Data Breach Investigation Report (DBIR), first published in 2008, is an annual publication that analyzes information security incidents from public and private organizations, with a focus on data breaches. Data breaches continue to have a major financial impact on organizations, as well as an impact on their reputations. Tenable Network Security offers dashboards and Assurance Report Cards (ARCs) that organizations can use to check themselves against the common threats described in the Verizon DBIR. As in previous years, the 2016 DBIR notes that a vast majority of all attacks fall into a few basic patterns. Throughout this and past years’ reports, suggestions are given for monitoring the network for each of these patterns. This dashboard can assist an organization in monitoring its network to reduce the successfulness of these attack patterns and to reduce its chances of a data breach.
The Verizon report recommends quickly keeping up with remediating vulnerabilities from major vendors and being vigilant to remediate older vulnerabilities or mitigate their risk. Remediating vulnerabilities are important, but not all vulnerabilities present the same level of risk to the organization. Depending on the organization, not even the same vulnerability may present the same level of risk due to the location of the system with the vulnerability.
The Verizon report focuses on the vulnerabilities from vendors such as Adobe, Microsoft, Oracle, OpenSSL, Apple and Mozilla. The vulnerabilities from these vendors are typically the ones to be commonly exploited by attackers. All of the vendors produce client-side products used for interaction with websites, which attackers use to leverage attacks against users. Due to the frequent occurrence of attacks with these products, Verizon specifically highlights the need for organizations to closely monitor these vulnerabilities. In some cases, attacks with Adobe vulnerabilities can compromise a user in less than five minutes. Once one user is compromised, the attacker can then use those credentials to compromise the rest of the organization.
Not only do newly released vulnerabilities become quickly exploited by attackers, but the vulnerabilities which have had patches published for over a year and remain in the organization are also targets. Attackers of many types have various methods to detect and exploit not only the newest vulnerabilities, but validate if older and more reliable exploitation vectors with older vulnerabilities still exist. Organizations need to ensure that adequate resources are available to address the vulnerabilities and whether or not to remediate them or mitigate their risk.
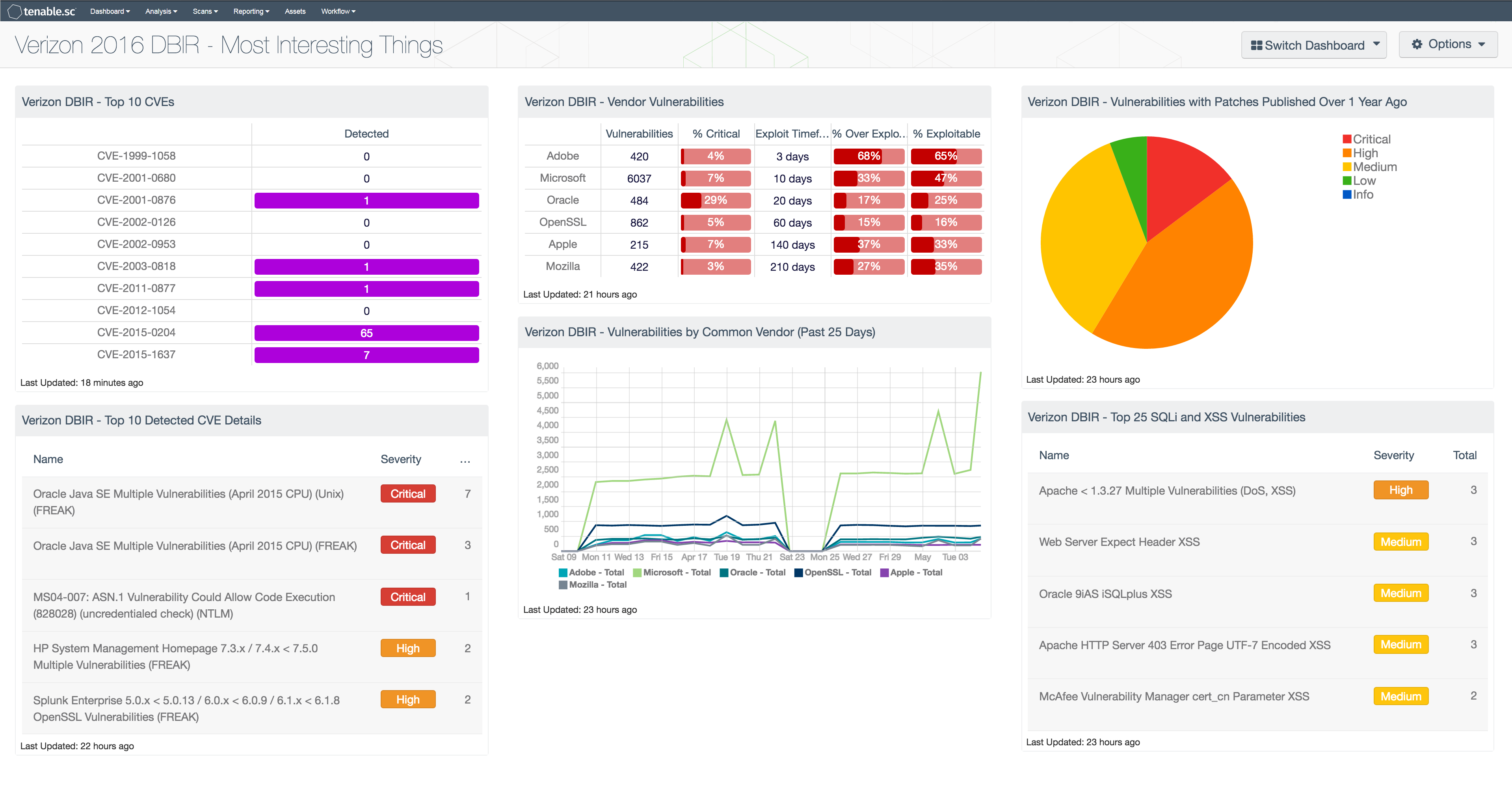
This dashboard assists organizations in improving analyst awareness of high priority vulnerabilities in the organization. Analysts can quickly see the CVEs that Verizon listed as the top 10 most exploited CVEs still in use today in both a matrix component and as a table component. Verizon mentions specific vendors who typically have vulnerabilities in their products, which have either short or long exploitation timeframes. The dashboard identifies those vendors along with metrics identifying the current state of the vulnerabilities in the organization and their exploitability. Web application vulnerabilities are also mentioned as a point of concern, which had increased as an attack vector from the previous year. The dashboard contains a table that identifies the top 25 SQL Injection (SQLi) and Cross-Site Scripting (XSS) vulnerabilities detected in the organization. Having visibility of vulnerabilities within an organization allows organizations to proactively respond to threats, mitigate vulnerabilities, and take preventative measures before any serious damage occurs.
Brief details of each CVE are listed below:
- CVE-1999-1058: Buffer overflow in Vermillion FTP Daemon VFTPD 1.23
- CVE-2001-0680: Directory traversal vulnerability in ftpd in QPC QVT/Net 4.0 and AVT/Term 5.0
- CVE-2001-0876: Buffer overflow in Universal Plug and Play (UPnP) on Windows 98, 98SE, ME, and XP
- CVE-2002-0126: Buffer overflow in BlackMoon FTP Server 1.0 through 1.5
- CVE-2002-0953: Arbitrary code execution with globals.php in PHP Address before 0.2f
- CVE-2003-0818: Multiple integer overflows in Microsoft ASN.1 library
- CVE-2011-0877: Unspecified vulnerability in multiple Oracle Database Server and Enterprise Manager Grid Control versions
- CVE-2012-1054: Local privilege escalation in multiple Puppet versions
- CVE-2015-0204: “FREAK” attack vector in multiple OpenSSL versions
- CVE-2015-1637: Schannel downgrade attack in multiple Microsoft Windows versions
The information provided in this dashboard provides insight into the effectiveness of an organization's information security policies and whether the current policies being enforced are effective. The dashboard components are guides that can be customized as necessary to meet organizational requirements.
This dashboard is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The dashboard can be easily located in the Tenable.sc Feed under the category Security Industry Trends. The dashboard requirements are:
- Tenable.sc 5.3.1
- Nessus 8.5.1
Tenable.sc provides continuous network monitoring, vulnerability identification, risk reduction, and compliance monitoring. Tenable.sc is continuously updated with information about advanced threats and zero-day vulnerabilities, and new types of regulatory compliance configuration audits. By integrating with Nessus, Tenable.sc’s continuous network monitoring is able to track vulnerabilities and mitigations across the enterprise.
The following components are included in this dashboard:
- Verizon DBIR - Top 10 CVEs: The “Verizon DBIR - Top 10 CVEs” matrix component provides an overview of the top 10 CVEs which comprise the majority of exploitable vulnerabilities in the Verizon 2016 DBIR report.
- Verizon DBIR - Top 10 Detected CVE Details: The “Verizon DBIR - Top 10 detected CVE details” table component provides details of the top 10 CVEs, which comprise the majority of exploitable vulnerabilities in the Verizon 2016 DBIR report.
- Verizon DBIR - Vendor Vulnerabilities: The “Verizon DBIR - Vendor Vulnerabilities” matrix component provides an overview of the vulnerabilities by specific vendors called out in the Verizon 2016 DBIR report.
- Verizon DBIR - Vulnerabilities by Common Vendor (Past 25 Days): The “Verizon DBIR - Vulnerabilities by Common Vendor (Past 25 Days)” line chart component assists analysts by providing a trend line of the last 25 days in relation to specific vendor vulnerabilities.
- Verizon DBIR - Vulnerabilities with Patches Published Over 1 Year Ago: The “Verizon DBIR - Vulnerabilities with Patches Published Over 1 Year Ago” pie chart provides a quick snapshot of the vulnerabilities in the organization.
- Verizon DBIR - Top 25 SQLi and XSS Vulnerabilities: The “Verizon DBIR - Top 25 SQLi and XSS Vulnerabilities” table component details the detected SQL Injection and Cross-Site Scripting vulnerabilities in the organization.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success