by Cesar Navas
Organizations are expanding beyond a typical Windows only environment and allowing different computer operating systems and software. Administrators and analysts should be aware of what software operates in their environment, especially in light of shadow IT possibilities. This dashboard provides insight into the operating systems and software in the environment as well as their vulnerability risk.
Software helps organizations and people to accomplish tasks and goals across different operating systems. Being able to interoperate with different files and workflows across different software packages and operating systems is great for the end user. However, the flexibility to allow users to work with different software applications comes at a cost of having to manage different products that can accomplish the same task. For instance, a user can create a Microsoft Word document in Windows and give this to another user who uses a Mac with Apple’s Pages software. The two users have different operating systems and software packages, but they can work together. Administrators and analysts need to know about the vulnerabilities in the environment regardless of how the user gets their task accomplished. This dashboard gives the administrators and analysts the information necessary to remediate these OS and software vulnerabilities across the different ecosystems.
Most software packages and operating systems have vulnerabilities of varying degrees of severity. Attackers will use these software vulnerabilities to compromise data and/or environments. In some cases, attackers only need one or a few vulnerabilities to carry out their attacks. Analysts should know about the different vulnerabilities and their exploitation risk to the environment. This dashboard relates actionable information to administrators and analysts to help them to better protect the environment, remediate vulnerabilities, and mitigate risks.
The dashboard provides broad information across major operating systems and software packages. The analyst is presented with components in the dashboard that show specific vulnerabilities as well as counts of vulnerability across severity levels. Not only are vulnerabilities shown for operating systems, but also web browsers and web browser plugins. The ubiquitous nature of Adobe Flash across multiple operating systems and web browsers makes Flash an attractive target to attackers. Java enables rich and entertaining content in end user applications and is another piece of software that needs constant attention to remain updated. There are many applications that run in web browsers and require a specific web browser for optimal operability. Web browsers are also a constant source of vulnerabilities regardless of the underlying operating system. One of the components in this dashboard shows vulnerabilities for many popular and common web browsers. The web browsers monitored for vulnerabilities are from vendors such as Microsoft, Apple, Google, Mozilla and Opera. Administrators and analysts need to be mindful of the various vulnerabilities in the environment and their risk to the environment.
This dashboard is available in the Tenable.sc Feed, an app store of dashboards, reports and assets. This dashboard can be easily located in the Feed under the category Threat Detection. The dashboard requirements are:
- Tenable.sc 4.8.2
- Nessus 8.5.1
- NNM 5.9.1
Tenable provides continuous network monitoring to identify vulnerabilities, reduce risk and ensure compliance. Our family of products includes Tenable.sc Continuous View (CV), Nessus, and Nessus Network Monitor (NNM). Tenable.sc CV provides the most comprehensive and integrated view of network health. Nessus is the global standard in detecting and assessing network data. NNM provides deep packet inspection to continuously discover and track users, applications, cloud infrastructures, trust relationships, and vulnerabilities.
This dashboard contains the following components:
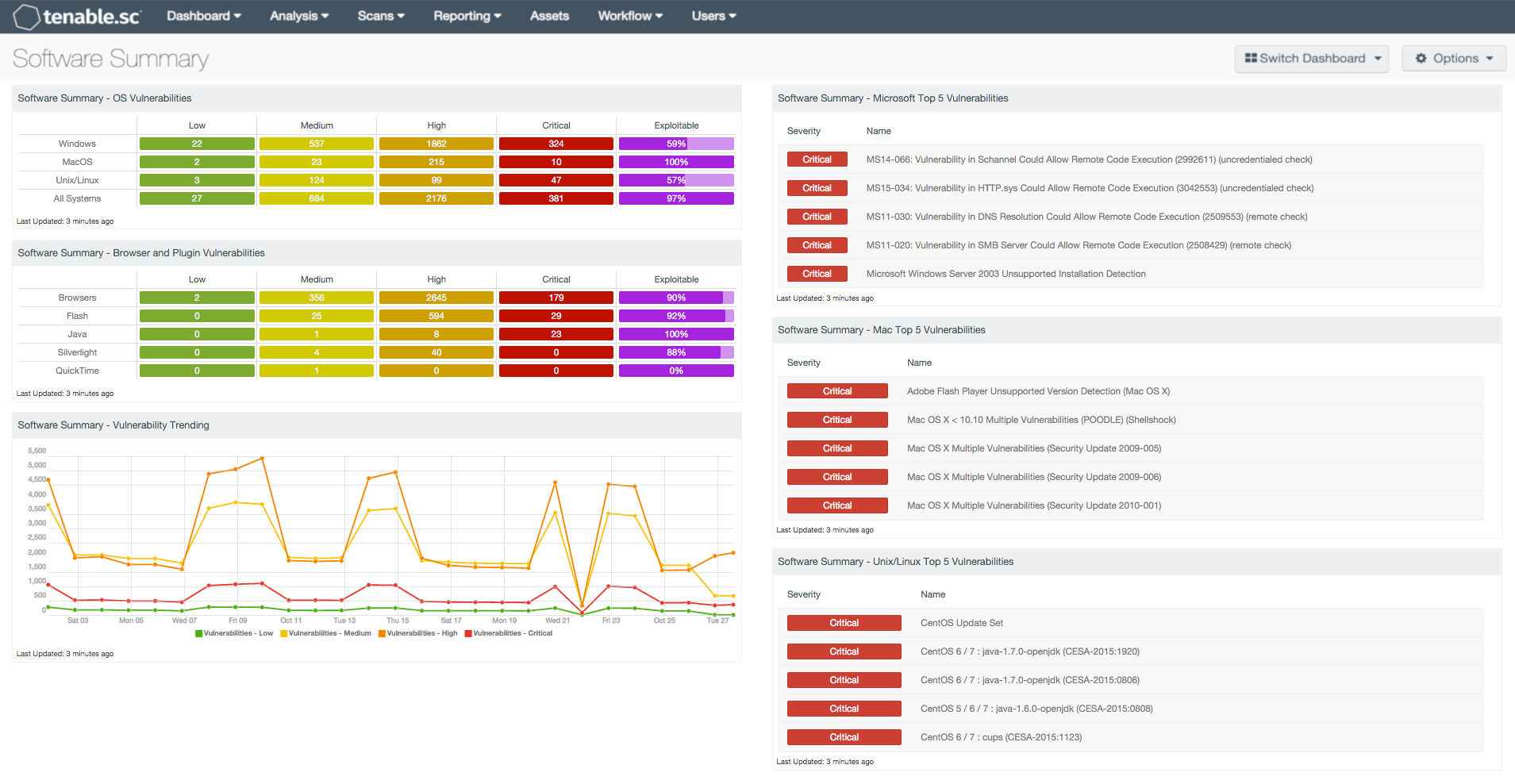
- OS Vulnerabilities: The “OS Vulnerabilities” matrix component displays four levels of vulnerability severity. This matrix also shows as a percentage how many hosts are exploitable.
- Browser and Plugin Vulnerabilities: The “Browser and Plugin Vulnerabilities” matrix component show a count of the vulnerabilities by four severity levels. The matrix component also shows as a percentage the number of exploitable hosts.
- Vulnerability Trending: The “Vulnerability Trending” line chart component shows over the last 25 days vulnerabilities of varying severity levels
- Microsoft Top 5 Vulnerabilities: The “Microsoft Top 5 Vulnerabilities” table is a quick look at the top five vulnerabilities relating to Microsoft technologies
- Mac Top 5 Vulnerabilities: The “Mac Top 5 Vulnerabilities” table is a quick look at the top five vulnerabilities relating to Mac OSX
- Unix/Linux Top 5 Vulnerabilities: The “Unix/Linux Top 5 Vulnerabilities” table is a quick look at the top five vulnerabilities relating to Linux and Unix technologies
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success