Social networks provide an avenue for organizations to connect and interact with customers across a variety of platforms. Many organizations use these sites to promote corporate news and inform customers on product releases. Unfortunately, these sites can negatively impact organizations due to employee usage. Monitoring these sites for inappropriate comments and excessive usage can help to reduce productivity issues and potential security risks that could leave an organization liable. Using this dashboard, organizations will be able to monitor social networking activity across the enterprise.
Employee usage of social networks can have negative repercussions for both organizations and employees. Without some type of policy in place that addresses social network usage, employees can leak confidential data, engage in illegal activities, and post negative comments that could result in legal action and employee termination. The popularity of social networking sites has also provided an avenue for social engineering attacks. When accessed on corporate systems, users can inadvertently inject malware into corporate networks through phishing attacks, malicious advertisements, and social engineering scams.
Some organizations have attempted to address these risks by fully or partially blocking access to social media on corporate networks. Unfortunately, employees can still access social networks through their mobile devices, so just blocking access may not prevent excessive or abusive behavior in the workplace. Implementing acceptable use policies that address social network usage on corporate networks can help to discourage and prevent usage within the workplace. Using this dashboard, organizations will obtain real-time information on social networking activity, which can be used to monitor and reduce overall security risks.
This dashboard presents an overview of social networking activity on the network. Activity from social networking sites are detected by the Tenable Passive Vulnerability Scanner (PVS) and forwarded to the Tenable Log Correlation Engine (LCE), which can help to identify and correlate events. Long term usage is also tracked that highlights hosts with excessive social networking activity. Passive scans will detect systems using social networking sites through mobile applications and other transient devices. Activity from popular social networking sites, discussion boards, media, and contact sites are also monitored. Components within this dashboard provide useful information for analysts in detecting hosts not adhering to policies and evading existing security controls. By monitoring social network activity, organizations can help to prevent inappropriate usage and safeguard critical data.
This dashboard is available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The dashboard can be easily located in the SecurityCenter Feed under the category Monitoring. The dashboard requirements are:
- SecurityCenter 5.4.0
- PVS 5.1.0
- LCE 4.8.1
Tenable Network Security transforms security technology for the business needs of tomorrow through comprehensive solutions that provide continuous visibility and critical context, enabling decisive actions to protect the organization. Tenable SecurityCenter Continuous View (CV) is continuously updated with information about advanced threats and zero-day vulnerabilities, and new types of regulatory compliance configuration audit files. Passive listening collects data to continuously monitor traffic and collect information about user activity, along with the discovery of additional vulnerabilities. Host data and data from other security products is analyzed to monitor for unauthorized and malicious activity on the network. SecurityCenter CV provides an organization with the most comprehensive view of the network and the intelligence needed to manage devices and users in order to safeguard critical assets and assist in ongoing security efforts.
The following components are included within this dashboard:
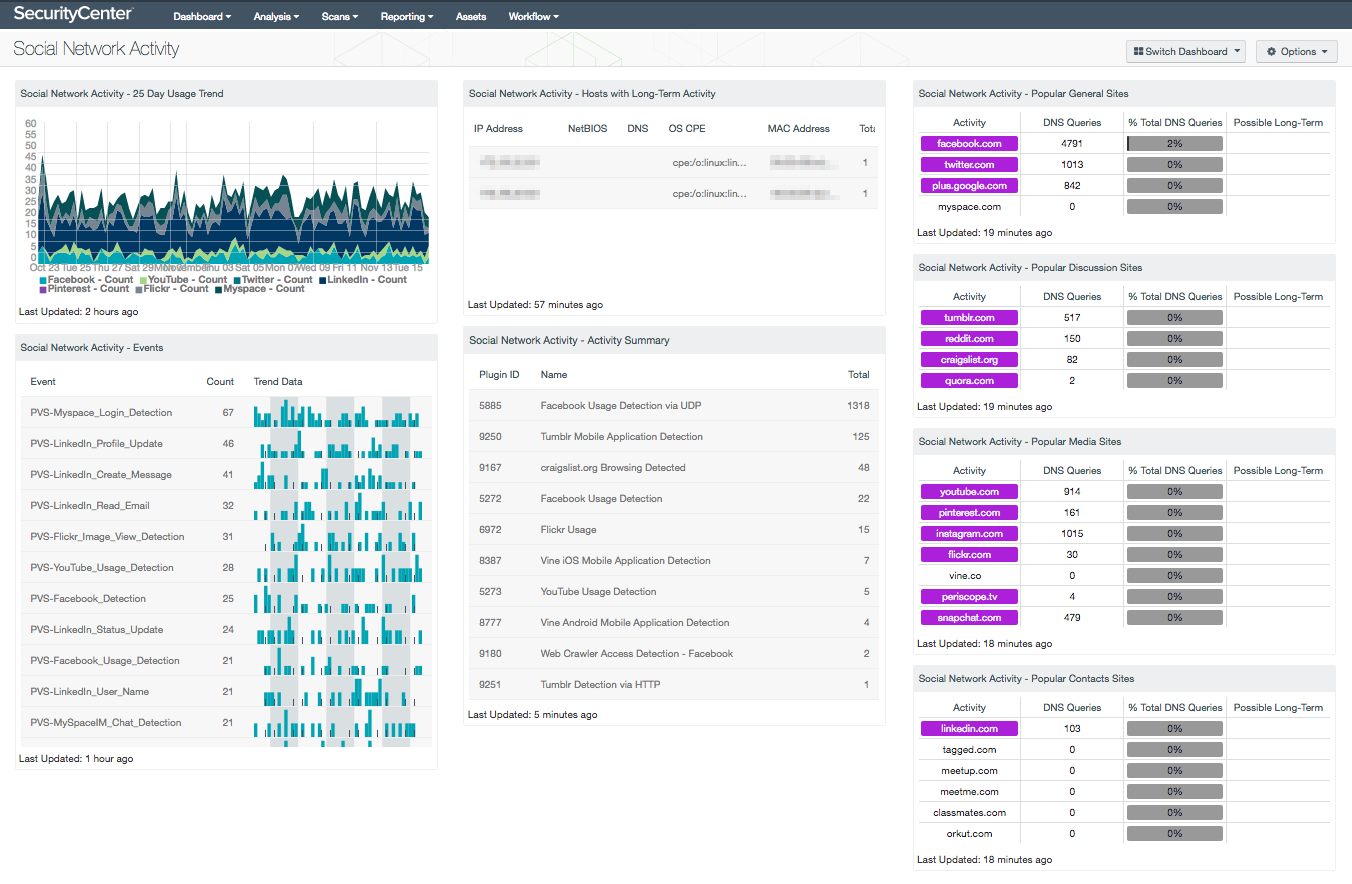
- Social Network Activity - 25 Day Usage Trend: This component presents a usage trend chart of several popular social networking sites over the last 25 days. Spikes within this component may indicate potentially excessive or unauthorized activity, and should be investigated by the analyst. LCE analyzes log data to passively detect and identify a variety of vulnerabilities. Note that this component relies on PVS detections being forwarded to the LCE. Organizations with end user agreement policies in place will find this information useful in monitoring employee activity.
- Social Network Activity - Events: This table presents social networking activity detected over the last 72 hours. Event data is collected by PVS and forwarded LCE, which can help to identify and correlate events. This component relies on PVS detections being forwarded to LCE, and is filtered by the 'social-networks' event type. Analysts can modify the information presented within this component per organizational requirements.
- Social Network Activity - Hosts with Long-Term Activity: This table presents information on hosts that have generated continuous social network events (such as visiting YouTube or Facebook) over the last 72 hours. Events are triggered when hosts have been detected using social network sites continuously for more than 20 minutes in a row. Information presented within this component can be useful in detecting excessive or unauthorized activity. Analysts should review corporate security guidelines or policies to determine whether the activity is authorized.
- Social Network Activity - Activity Summary: This component displays a list of social network activity detected on hosts by PVS. Hosts are continuously monitored by PVS and this component highlights accesses of social networking. PVS has the ability to monitor a wide variety of network traffic, which can be used by analysts to detect social networking activity missed during active scans. The table is filtered by specific social networking sites, discussion boards, social media, and social contact sites, and sorted by count. By clicking on the Browse Component Data icon, analysts can obtain additional information on the vulnerability such as IP address, MAC address, and date discovered.
- Social Network Activity - Popular General Sites: This matrix presents network activity in the last 72 hours related to several popular general social networking sites. This information can be used by analysts to detect hosts violating acceptable use policies, and evading security controls in an attempt to access unauthorized websites.
- Social Network Activity - Popular Discussion Sites: This matrix presents network activity in the last 72 hours related to several popular general social networking discussion sites. These social networking sites include blog sites and discussion boards. The site URL in the activity column is highlighted purple if any activity was detected.
- Social Network Activity - Popular Media Sites: This matrix presents network activity in the last 72 hours related to several popular general social networking media sites. This component specifically focuses on social networking image and video sharing sites.
- Social Network Activity - Popular Contacts Sites: This matrix presents network activity in the last 72 hours related to several popular general social networking contacts sites. This component specifically focuses on educational, personal, and career-oriented social networking sites.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success