by Josef Weiss
Questionable content can be defined as content that may be unauthorized, objectionable, or offensive. Many times questionable content may also be a path to phishing campaigns, in which attackers masquerading as other entities attempt to acquire sensitive information from end users.
For a detected web server, active web application scanning is no guarantee that all hosted web sites will be found. There may be no links between two web sites hosted on the same web server. Similarly, scanning a network for all ports to look for web servers that may have been installed as part of a botnet is difficult to do in real time. Because of this, malicious web servers are commonly found on university, home user, and any type of large network.
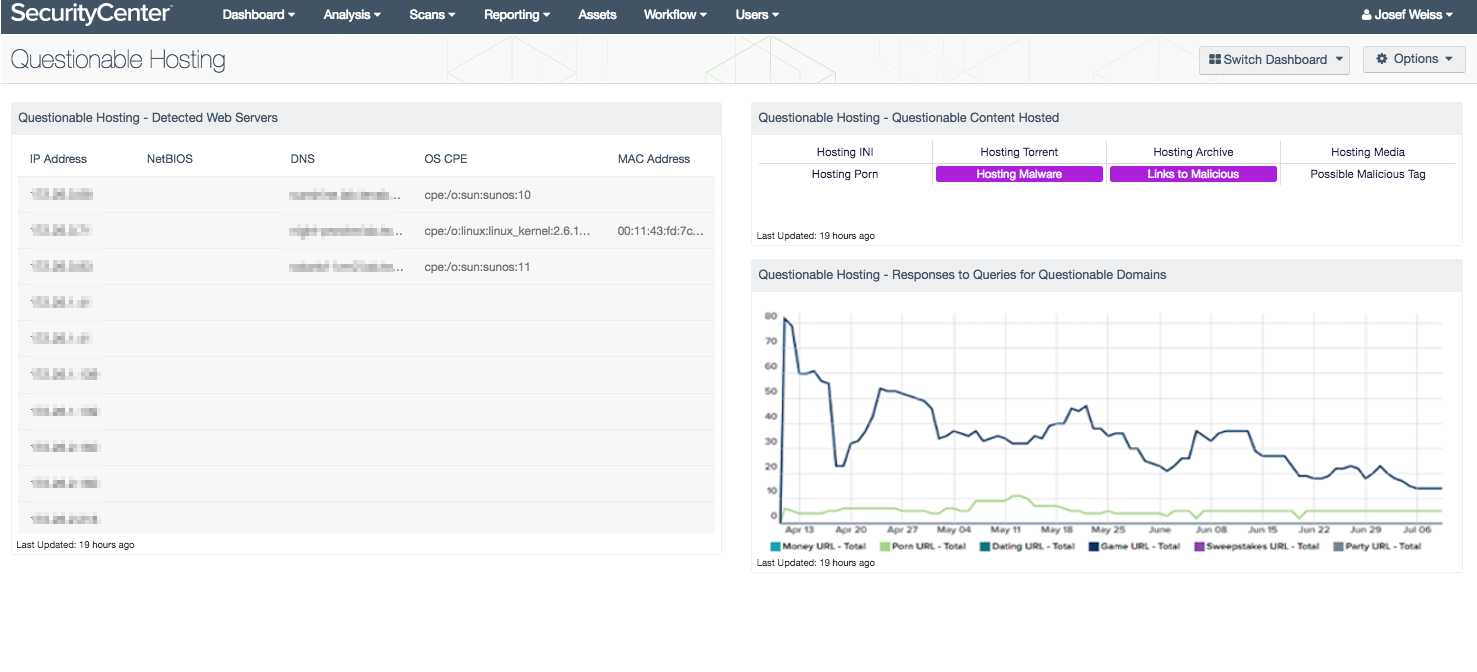
This dashboard presents all web servers passively detected on the network by the Tenable Passive Vulnerability Scanner (PVS), as well as questionable content that the web servers might be hosting and trend lines for detected web sites that contain keywords not expected for the local network. End users who visit websites that contain keywords related to money, porn, dating, games, sweepstakes, and parties are also displayed.
Using the active scanning, agent scanning, passive listening, and host data sensors, SecurityCenter Continuous View (CV) can provide a more comprehensive view of devices accessing the network. By practicing continuous monitoring, organizations can more effectively assess risk and identify authorized and unauthorized activity on their network.
The dashboard and its components are available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The dashboard can be easily located in the SecurityCenter Feed under the category Discovery & Detection.
The dashboard requirements are:
- SecurityCenter 4.8.2
- Nessus 6.7.0
- PVS 5.0.0
This dashboard requires “Full Text Search” to be enabled for each analyzed repository.
As hosts connect to network, the race begins to identify all the vulnerabilities and assess how each system will affect the network. Only Tenable can automatically analyze information from active scanning, intelligent connectors, agent scanning, passive listening, and host data. Active scanning periodically examines hosts to determine the level of risk posed to the organization. Intelligent connectors leverage other security investments in the environment to integrate security data in order to improve context and analysis. Agent scanning provides the ability to rapidly assess hosts without the need for credentials and to detect hosts that were offline during active scans. Passive listening provides real-time monitoring to collect information about hosts connected to the network and how the hosts are communicating. Host data uses logs, file system activity, and configuration changes to actively monitor host activities and events to identify malicious activity and anomalous behavior.
The dashboard contains the following components:
- Questionable Hosting - Detected Web Servers - This table presents all web servers passively detected on the network, including web servers detected by PVS plugins 1442 (detection of web servers that send a “Server:” string in their server response), 8166 (detection of web servers that do not send a “Server:” string in their server response), and 7034 (HTTP server vhost detection).
- Questionable Hosting - Questionable Content Hosted - This component presents indicators of possible questionable content hosted on web servers on the network, including hosting .ini files, torrent files, archive files (which might contain sensitive data), media files (which might be copyrighted), and malware, as well as linking to malicious content, and serving possibly malicious script and iFrame tags. A purple indicator means questionable content was detected. Questionable content should be further investigated to ensure compliance with organizational standards. Additional information can be obtained by clicking on the indicator to drill down and view the detailed vulnerability information.
- Questionable Hosting - Responses to Queries for Questionable Domains - This chart presents detections of questionable domain name requests that web servers on the network have responded to over the last three months. The lines show answered domain name requests for URLs containing keywords related to money, porn, dating, game, sweepstakes, and party. Note that these keywords will not find all questionable domains and there may be a high false-positive rate. Keywords can be added or removed as needed in the series’ filters. Domain groupings can also be added or removed as needed.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success