by Stephanie Dunn
July 20, 2017
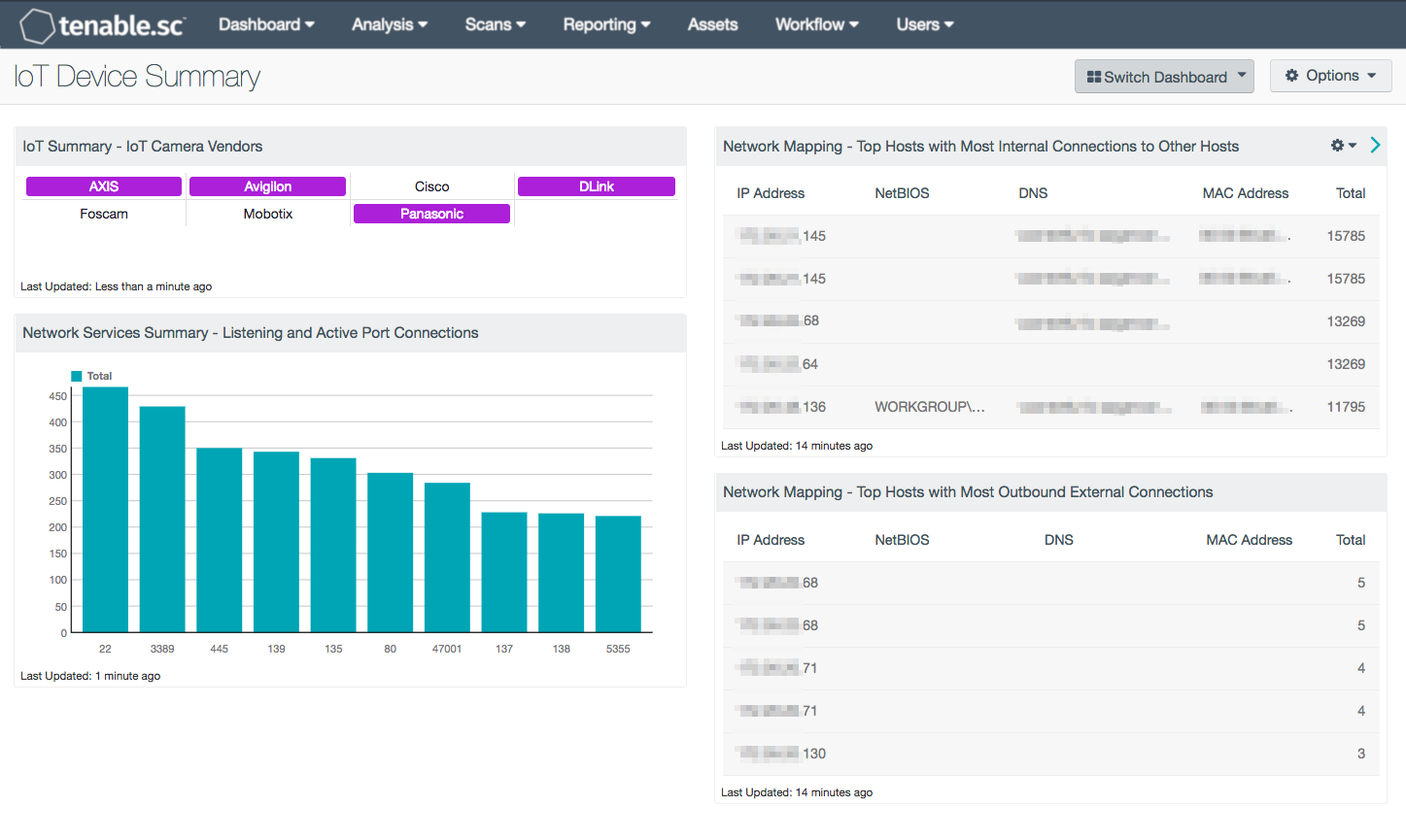
Despite lacking basic security features, devices that belong to the Internet of Things (IoT) are becoming increasingly present in enterprise settings. Without careful monitoring, IoT devices could be exploited by attackers seeking to infiltrate the organization. The IoT Device Summary dashboard presents important insight into the presence of IoT devices on the network by leveraging data from Tenable sensors.
In 2013, the Global Standards Initiative on Internet of Things (IoT-GSI) defined the IoT as “a global infrastructure for the information society, enabling advanced services by interconnecting (physical and virtual) things based on existing and evolving interoperable information and communication technologies.” IoT is seen in the consumer space as recently internet-enabled devices (appliances or electronics). In the commercial space, IoT devices are often related to security, such as cameras or door locks.
The IoT Device Summary dashboard highlights information useful to security teams looking to secure a network with IoT devices connected. A matrix component indicates the detection of a camera or video device from an Open Network Video Interface Forum (ONVIF) vendor. A bar chart tracks network port usage and two tables list the IP addresses with the most internal and external connections. A filter for a specific subnet, IP address list, or static asset could be added to focus the bar chart and tables on the IoT devices connected to the network.
This dashboard is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The dashboard can be easily located in the Tenable.sc Feed under the category Monitoring. The dashboard requirements are:
- SecurityCenter 5.4.3
- Nessus 8.4.0
- Nessus Network Monitor 5.8.1
Tenable.sc Continuous View (CV) is the market-defining continuous network monitoring solution and can assist in securing an organization’s internal network by effectively responding to intrusions and attacks. Tenable.sc CV is continuously updated with information about advanced threats, zero-day vulnerabilities, and new regulatory compliance data. Active scanning periodically examines systems to determine vulnerabilities and compliance concerns. Agent scanning enables scanning and detection of vulnerabilities on transient and isolated devices. Passive listening provides real-time discovery of vulnerabilities on operating systems, protocols, network services, wireless devices, web applications, and critical infrastructure. Host data and data from other security products are analyzed to monitor the network for malware, intrusions, and other forms of malicious activity. Tenable.sc CV provides an organization with the most comprehensive view of the network and intelligence needed to support proactive intrusion prevention efforts.
The following components are included within this dashboard
- IoT Summary – IoT Camera Vendors: This matrix presents an overview of IoT-based network camera devices by vendor. Each vendor listed includes network or IP-based cameras that are supported by the Open Network Video Interface Forum (ONVIF). ONVIF is an organization that supports the development of a global standard for IP-based security devices. An indicator will turn purple when a specific device has been detected. The analyst can click on the highlighted indicator, and drill down to obtain additional information on the detected device.
- Network Services Summary - Listening and Active Port Connections: This bar chart presents the top 10 ports detected on hosts that are listening or have active port connections. Nessus provides several plugins that leverage the “Netstat” command to determine all listening and enabled connections on hosts. This component can be modified to include specific port connections per organizational requirements.
- Network Mapping - Top Hosts with Most Internal External Connections: This table presents information on those hosts with the most passively detected internal connections to other hosts (Internal Client Trusted Connection). The table is sorted so that the host with the highest count of detections is at the top. This information can assist an organization in understanding who is talking to whom, as well as detecting any unauthorized or suspicious host connections.
- Network Mapping - Top Hosts with Most Outbound External Connections: This table presents information on those hosts with the most passively detected outbound external connections. The table is sorted so that the host with the highest count of detections is at the top. This information can assist an organization in understanding who is talking to whom, as well as detecting any unauthorized or suspicious host connections.