by Cody Dumont
In February 2014, the Australian Signals Directorate (ASD, formerly DSD) updated the publication “Strategies to Mitigate Targeted Cyber Intrusions” (available at http://www.asd.gov.au/infosec/top35mitigationstrategies.htm). The publication contains a list of 35 strategies to mitigate targeted cyber intrusions, ranked in order of overall effectiveness. According to ASD, over 85% of the cyber intrusions that ASD responds to could be prevented by following the top four mitigation strategies on the list.
According the ASD “Strategies to Mitigate Targeted Cyber Intrusions” publication, “The Top 4 mitigation strategies, when implemented as a package, provide a large reduction of risk for a relatively small investment of time, effort, and money. ASD recommends implementing these Top 4 mitigation strategies first on workstations of users who are most likely to be targeted by cyber intrusions, and then on all workstations and servers across the organisation.”
Tenable’s Tenable.sc Continuous View (CV) provides an organisation with a proactive method of discovering cyber intrusions, so the organisation will not have to just rely on individual products reporting partial findings. Tenable Security Center provides the unique ability to correlate vulnerabilities and configuration audits in a single location, enabling a proactive approach to continuous network monitoring. This dashboard provides an organisation with detailed information on the implementation of each of the ASD Top 4 mitigation strategies: application whitelisting, patch applications, patch operating system vulnerabilities, and restricting users with administrative privileges.
The dashboard and its components are available in the Security Center Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The dashboard can be easily located in the Security Center Feed under the category Compliance & Configuration Assessment.
The dashboard requirements are:
- Tenable Security Center 5.9.0
- Nessus 8.5.1
- NNM 5.9.0
Tenable Security Center’s ability to continuously monitor the network to identify vulnerabilities, reduce risk, and ensure compliance differentiates Tenable from the competition and provides organisations with the ability to be proactive while implementing the Strategies to Mitigate Targeted Cyber Intrusions. The ability of Nessus and NNM to detect vulnerabilities on the network is unmatched in the industry. Nessus actively scans the network for vulnerabilities and compliance issues, while NNM passively monitors network traffic.
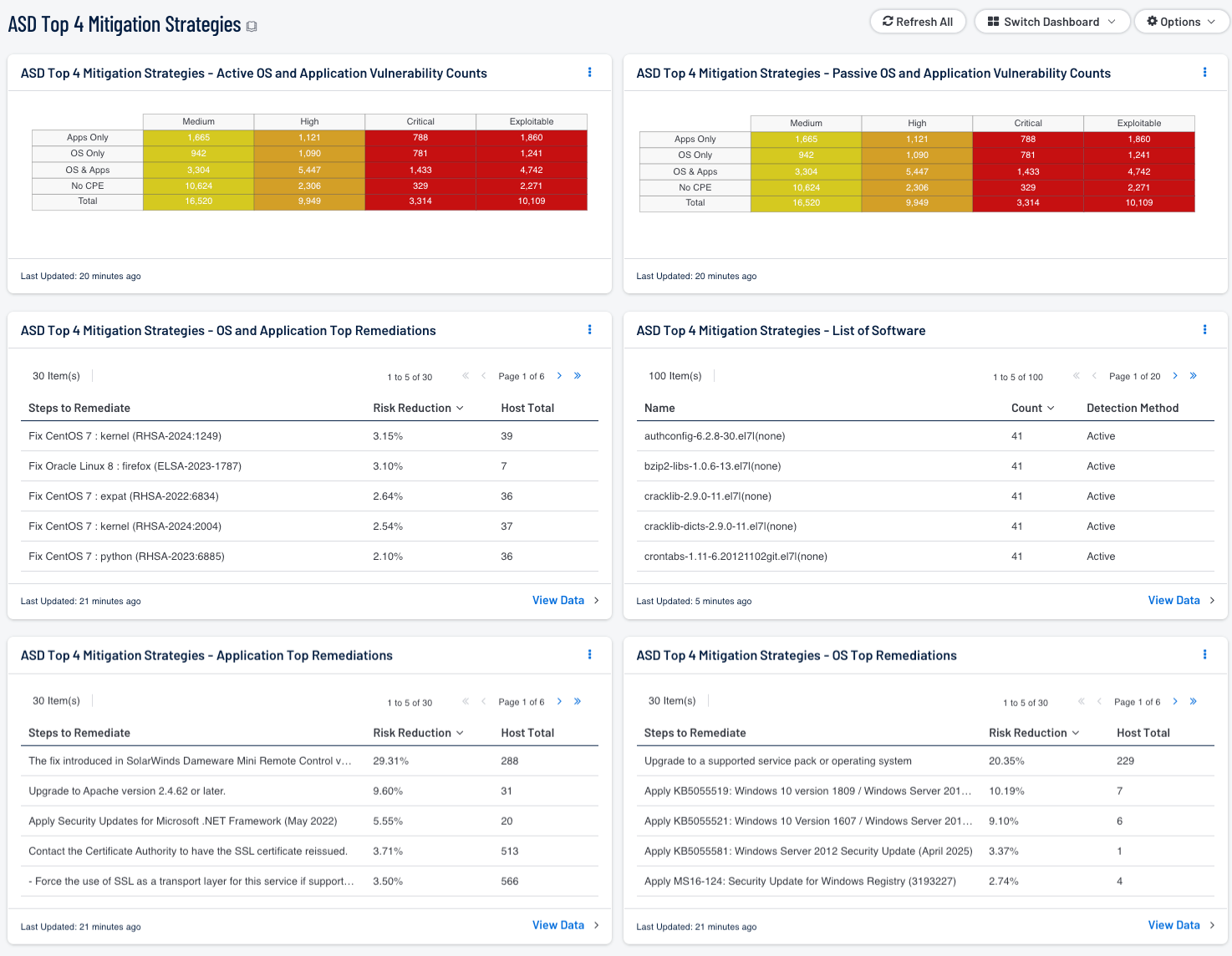
ASD Top 4 Mitigation Strategies - Active OS and Application Vulnerability Counts: This component provides a count of the active vulnerabilities discovered on the network based on if the vulnerabilities are for operating systems, applications, or a combination of both. This data shows analysts a comparison of applications versus operating systems.
ASD Top 4 Mitigation Strategies - OS & Application Top Remediations: This component provides a remediation summary for plugins that are classified as both application and operating system. The list shows remediation actions that may be taken to prioritize solutions that will mitigate several risks. The remediation summary provides the list of solutions to resolve security flaws of a particular application. The data provided includes the solution description, risk reduction percentage, and how many hosts are affected.
ASD Top 4 Mitigation Strategies - Application Top Remediations: This component provides a list of application-centric remediation actions which have the greatest effect in reducing risk. By applying the defined patches, other vulnerabilities will also be mitigated. The CPE regex “cpe:/a” is the prefix for application CPE strings. The remediation summary provides the list of solutions to resolve security flaws of a particular application. The data provided includes the solution description, risk reduction percentage, and how many hosts are affected.
ASD Top 4 Mitigation Strategies - OS Top Remediations: This component provides a list of operating system-centric remediation actions which have the greatest effect in reducing risk. By applying the defined patches, other vulnerabilities will also be mitigated. The CPE regex “cpe:/o” is the prefix for operating system CPE strings. The remediation summary provides the list of solutions to resolve security flaws of a particular application. The data provided includes the solution description, risk reduction percentage, and how many hosts are affected.
ASD Top 4 Mitigation Strategies - Passive OS and Application Vulnerability Counts: This component provides a count of the passive vulnerabilities discovered on the network based on if the vulnerabilities are for operating systems, applications, or a combination of both. This data shows analysts a comparison of applications versus operating systems.
ASD Top 4 Mitigation Strategies - List of Software: The foundation of application whitelisting is knowing what applications are installed within an organization. Security Center can collect information about installed applications using the List of Software tool, and by collecting logs from several sources such as workstations, servers, and enterprise whitelist applications. This component provides a detailed list of software currently discovered on the network. The best practice with this component is to create several copies of the component, and apply an asset or subnet to each component. Modifying the filters in this manner will provide the organization with the details for installed software for each targeted segment of the network.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success