The Weakest Link – Cloud Application Users and Administrators
Privileged users are a fact of life, but they pose an expanding opportunity to adversaries in the new IT landscape. There are two classes of privileged users on your network today: the users of your cloud-based applications such as SalesForce and NetSuite, and your system administrators. Any adversary who is able to compromise a desktop, laptop or mobile device of one of these users has unfettered access to your data.
Tenable helps organizations manage the risk posed from these users through automated detection and assessment as part of a continuous network monitoring program. SecurityCenter Continuous View (CV) identifies which cloud applications are in use, which systems are being leveraged by system administrators, and of all these systems, which ones can easily be exploited by client-side attacks. It’s the exploitable laptops and desktops of your cloud users and administrators that can be compromised and then used to steal data from your network.
The following dashboard is an example of the types of analytics that can be performed on the data collected by SecurityCenter Continuous View sensors:
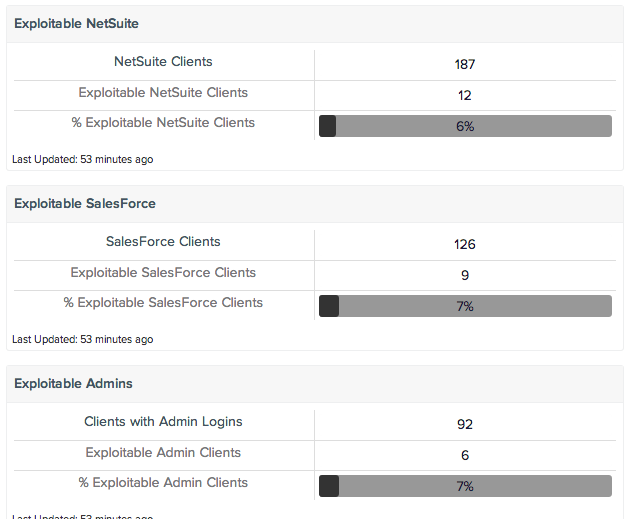
In this screen shot of a SecurityCenter dashboard from a live customer network, there were 187 systems identified as having accessed NetSuite, 126 systems as having accessed SalesForce and 92 systems that had an administrator account originate from them. For each of these groups, less than 10% also had at least one client-side application which had a known exploit available for it. I’ve seen other networks where these numbers were closer to 100%.
SecurityCenter Continuous View can produce this sort of report because of its unique sensors. Scanning, sniffing and log analysis allows SecurityCenter CV to classify systems based on their cloud applications, whether an administrator logs in from the cloud and whether a system has client-side exploits. For a more detailed explanation of how this dashboard was created, please consider this post to our Discussion Portal.
Scanning, sniffing and log analysis allows SecurityCenter CV to classify systems based on their cloud applications
Perhaps these systems should be patched before other systems. Perhaps these systems should have their network access restricted to only the cloud resources they use. Having this data at your fingertips can help you take the appropriate action to mitigate your risk.
If you’d like to learn more about continuous network monitoring and how SecurityCenter Continuous View identifies vulnerabilities, reduces risk and ensures compliance, please download a copy of “Continuous Monitoring for the New IT Landscape.” Readers of the paper will learn how mobile and on-premises users, as well as cloud and non-cloud applications, can have their risk and health measured so actions can be taken to secure their network.
Learn more
- Cloud
- SecurityCenter
- Vulnerability Management



Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success