Hold the Door: Why Organizations Need to Prioritize Patching SSL VPNs

Three critical SSL VPN vulnerabilities have become some of the most exploited by advanced persistent threat actors and ransomware groups.
To effectively prioritize remediation efforts, defenders must understand how attackers are targeting organizations and then act on that knowledge. Vulnerabilities in SSL VPN products are some of the most exploited by attackers for initial access to target networks, acting as a doorway for exploitation. Defenders need to hold the door — Game of Thrones fans will understand this reference. To defend distributed enterprise networks, teams must ensure their SSL VPN products are fully updated and properly configured to keep attackers out.
Earlier this year, the Tenable Security Response Team (SRT) published our Threat Landscape Retrospective (TLR) report examining major trends from 2020. One of those trends was the popularity of secure socket layer (SSL) virtual private network (VPN) vulnerabilities with threat actors. The TLR specifically highlighted the following three vulnerabilities in VPN products as part of the Top Five Vulnerabilities of the year.
| CVE | Affected Product | CVSS | VPR* |
|---|---|---|---|
| CVE-2019-19781 | Citrix Application Delivery Controller (ADC), Gateway and SD-WAN WANOP | 9.8 | 9.9 |
| CVE-2019-11510 | Pulse Connect Secure SSL VPN | 10.0 | 10.0 |
| CVE-2018-13379 | Fortinet Fortigate SSL VPN | 9.8 | 9.9 |
*Please note: Tenable’s Vulnerability Priority Rating (VPR) scores are calculated nightly. This blog post was published on August 25 and reflects VPR at that time.
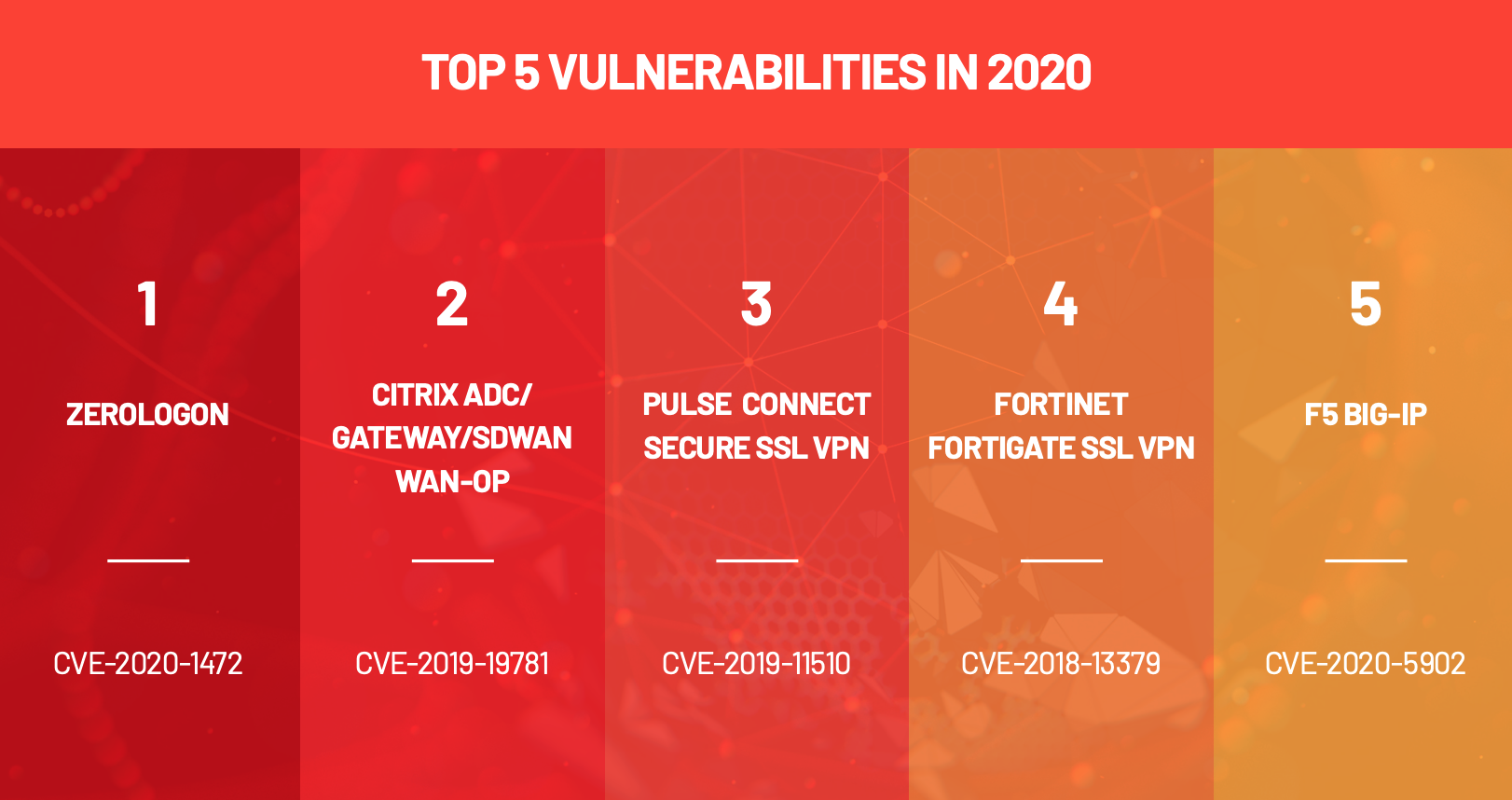
Source: Tenable 2020 Threat Landscape Retrospective, January 2021.
Although all three vulnerabilities were disclosed in 2019 and patched by January 2020, they continue to be routinely exploited more than halfway through 2021. According to a joint cybersecurity advisory from four international government agencies, these vulnerabilities were some of the most exploited in 2020. In fact, CVE-2019-19781 was named the most exploited vulnerability of 2020, according to government data.
Based on this information, we felt it was prudent to re-examine how attackers have historically been exploiting these vulnerabilities, along with new reports of attacks, in 2021. We hope collecting this information in a single place will illustrate the dire importance of patching these vulnerabilities for any organizations that have been lagging.
SSL VPNs: the doorway for attackers
To provide a more holistic picture, we also explore several other relevant CVEs in the three key SSL VPN products. The additional CVEs highlighted in the table below have been included in alerts alongside the three listed above or have been paired with other vulnerabilities as part of attack chains.
| Product | CVEs |
|---|---|
| Citrix ADC, Gateway and SD-WAN WANOP | CVE-2019-19781, CVE-2020-8193 CVE-2020-8195, CVE-2020-8196 |
| Pulse Connect Secure SSL VPN | CVE-2019-11510, CVE-2019-11539, CVE-2020-8260, CVE-2020-8243, CVE-2021-22893 |
| Fortinet Fortigate SSL VPN | CVE-2018-13379, CVE-2018-13382, CVE-2018-13383, CVE-2019-5591, CVE-2020-12812 |
Source: Tenable, August 2021
Citrix ADC, Gateway and SD-WAN WANOP
CVE-2019-19781 is a path or directory traversal vulnerability in Citrix ADC, Gateway and SD-WAN WANOP products disclosed on December 17, 2019. It received a CVSSv3 score of 9.8. At the time the vulnerability was disclosed, no patches were available. To exploit this vulnerability, an unauthenticated, remote attacker could send a specially crafted request containing a directory traversal string to a vulnerable Citrix endpoint. Successful exploitation would allow an attacker to execute arbitrary code.
Directory traversal flaws aren’t new, they have been around for decades, but they have seen a resurgence in recent years. As its name implies, exploitation of directory traversal flaws would allow an attacker to traverse file paths that would normally be inaccessible to a non-administrative user.
For weeks, there was an expectation that without patches, this vulnerability would be exploited in the wild. By January 10, 2020, and after extensive attention and analysis from researchers, exploit scripts were circulating publicly. On the following day, the SANS Internet Storm Center reported exploitation attempts using those scripts against its honeypots. Citrix finally released patches for CVE-2019-19781 on January 24, 2020. Based on the history of exploitation that continues well into 2021, it’s safe to presume many organizations still have not applied these patches a year-and-a-half after they were released.
Exploitation of CVE-2019-19781 began shortly after it was disclosed. Reports and alerts circulated throughout 2020, earning it the status of the most exploited CVE for the year. You wouldn’t expect a vulnerability this popular to fade into obscurity, and you’d be right. Attackers continue to exploit this vulnerability into 2021.
CVE-2019-19781 has been leveraged by several threat groups targeting the healthcare industry. Ransomware groups like Maze (now defunct) and Conti have a preference for attacking remote desktop protocol, but have also been observed exploiting CVE-2019-19781 in attacks against the healthcare sector. Additionally, advanced persistent threat (APT) groups have exploited this vulnerability against targets working on COVID-19 vaccine development.
Attackers have indicated their preference for this vulnerability in online forums between January 2020 and March 2021. CVE-2019-19781 was the top mentioned CVE on Russian and English-speaking dark web forums, according to Cognyte research. It was mentioned in 49 posts, the second highest number of posts.
In June 2021, researchers at Trend Micro published an analysis of the Nefilim ransomware group. This research revealed that this group uses CVE-2019-19781 as an initial attack vector. Trend Micro used Nefilim as a case study to illustrate behaviors of “modern ransomware attacks,” so it stands to reason that other ransomware groups are also using this vulnerability in their attacks.
Pulse Connect Secure
In April 2019, Pulse Secure released an out-of-band security advisory to address multiple vulnerabilities in its Pulse Connect Secure SSL VPN solution, including several flaws disclosed by researchers Meh Chang and Orange Tsai of the DEVCORE research team. The most notable vulnerability listed in the advisory was CVE-2019-11510, an arbitrary file disclosure vulnerability that was assigned the maximum CVSSv3 score of 10.0. An unauthenticated, remote attacker could exploit the vulnerability by sending an HTTP request containing a specially crafted directory traversal string.
Successful exploitation of CVE-2019-11510 would allow an attacker to read the contents of sensitive files on the vulnerable Pulse Connect Secure device. One file in particular, data.mdb, contains plain-text passwords for the SSL VPN. If an attacker is able to read this file, they can use the plain text passwords to authenticate to the vulnerable SSL VPN. By itself, the vulnerability is significant because it easily allows attackers to authenticate to an SSL VPN via simply sending requests to a vulnerable device. However when chained with CVE-2019-11539, a post-authentication command injection vulnerability in Pulse Secure, an attacker could gain access to a restricted environment, such as a corporate network.
Post-authentication flaws are exploited after an attacker has successfully authenticated to a vulnerable device, either using a separate pre-authentication vulnerability or using valid credentials obtained through theft or brute force.
In August 2019, following Chang and Tsai’s Black Hat and DEF CON 27 presentations regarding their research into several SSL VPNs, proof-of-concept (PoC) exploit scripts began circulating on GitHub. Soon after, researchers noticed an uptick in attempts to scan for and exploit vulnerable Pulse Connect Secure systems.
In addition to the sensitive plain-text passwords accessible by exploiting CVE-2019-11510, researchers also discovered that attackers could access Active Directory credentials that were encrypted using a static key that would allow for “easy decryption.”
In January 2020, attackers leveraged CVE-2019-11510 in order to deploy the REvil, or Sodinokibi, ransomware. In March, researchers at Palo Alto Network’s Unit 42 noted that CVE-2019-11510 was also used by the Maze ransomware group. It’s just one of the SSL VPN vulnerabilities used by ransomware groups to get their foot in the door before moving laterally in order to distribute ransomware payload across a network.
In the first quarter of 2021, a report from Nuspire showed an 1,527% increase in attempts to exploit CVE-2019-11510 against vulnerable Pulse Connect Secure SSL VPNs.
While much of the attention has been on CVE-2019-11510 for good reason, a zero-day in Pulse Connect Secure, identified as CVE-2021-22893, was disclosed in April 2021 that was exploited in the wild. Soon after this disclosure, researchers found that Chinese threat actors were leveraging CVE-2021-22893 as well as other post-authentication vulnerabilities in Pulse Connect Secure flaws in addition to CVE-2019-11539. These include CVE-2020-8260 and CVE-2020-8243, two flaws in the administrator web interface of Pulse Connect Secure devices that were patched in September and October 2020.
Fortinet FortiOS
In May 2019, Fortinet released Product Security Incident Response Team (PSIRT) advisory FG-IR-18-384 to address CVE-2018-13379, a directory traversal vulnerability in their FortiOS SSL VPN. The flaw allows an unauthenticated attacker to access arbitrary system files using crafted HTTP requests.
This vulnerability was described by Chang and Tsai of DEVCORE in the same 2019 Black Hat USA and DEF CON 27 presentations as the Pulse Secure vulnerability mentioned earlier. The pair detailed how CVE-2018-13379 could be utilized to obtain a session file which contains the username and plaintext password for a VPN user, very similar to CVE-2019-11510. This data would prove valuable to chain with additional vulnerabilities in the VPN, including CVE-2018-13383, a post-authentication heap overflow vulnerability which was utilized to gain a remote shell on affected versions of FortiOS SSL VPNs. CVE-2018-13383 was addressed in PSIRT advisory FG-IR-18-388 in April 2019 with additional affected release branches patched in May, August and November 2019.
Shortly after the Black Hat and DEF CON conferences, Fortinet released a blog post discussing the vulnerabilities and patches, urging customers to apply the patches as soon as possible. Within a month after the conference talks, attackers began exploiting vulnerable devices and released multiple PoCs for several CVEs in FortiGate SSL VPNs.
While CVE-2018-13379 was one of the most favored vulnerabilities for attackers and APT groups, additional flaws in FortiOS were identified and patched by Fortinet, including CVE-2019-5591 and CVE-2020-12812, which were also leveraged by threat actors.
CVE-2019-5591 is a default configuration vulnerability in the FortiGate SSL VPN due to a lack of verification of a Lightweight Directory Access Protocol (LDAP) certificate, which would allow the attacker to harvest sensitive information intended for a legitimate LDAP server.
CVE-2020-12812 is an improper authentication vulnerability in the FortiGate SSL VPN due to a misconfigured setting for two-factor authentication. This could be exploited if a legitimate user changes the case of their username, nullifying the second factor requirement, allowing an attacker to bypass two-factor authentication altogether.
According to Nuspire, attacks leveraging CVE-2018-13379 against Fortinet’s SSL VPNs increased 1,916% in the first quarter of 2021.
In an April report from Kaspersky ICS CERT, an incident response investigation revealed that CVE-2018-13379 was utilized as an initial entry point into an enterprise network by threat actors who later deployed Cring ransomware. The Cring ransomware is a relatively new ransomware variant which utilizes two forms of encryption and deletes backup files in attempts to force victims to pay the ransom.
With the public PoCs and ample unpatched devices for attackers to target, FortiGate SSL VPNs will remain highly valuable entry points for attackers unless action is taken to secure the devices and apply the necessary security updates. As attacks continue, Fortinet has attempted to reach out to its customers and release regular updates, including a blog post in June 2021 urging customers to take immediate action to apply the patches or mitigations outlined in their PSIRTs.
Threat actors target all three SSL VPNs
Nation-state actors have shown a preference for SSL VPN vulnerabilities. On April 15, 2021, the National Security Agency (NSA) and Federal Bureau of Investigation (FBI) published a joint alert about Russian Foreign Intelligence Service (SVR) activity leveraging all of these vulnerabilities. This followed alerts from 2020 pointing to state-sponsored attacks from China, Iran and Russia leveraging these vulnerabilities. These vulnerabilities were often leveraged in exploit chains leading to the takeover of domain controllers through the use of CVE-2020-1472, also known as Zerologon.
An additional advisory followed from the FBI in May 2021 urging the immediate patching of CVE-2018-13379, CVE-2020-12812 and CVE-2019-5591 while also providing indicators of compromise (IOCs) that had been observed with APT activity. CVE-2018-13379, CVE-2019-19781 and CVE-2019-11510 were all included in a joint advisory listing the Top Routinely Exploited Vulnerabilities of 2020 by the Cybersecurity and Infrastructure Security Agency (CISA), the U.K. National Cyber Security Center (NCSC), the Australian Cyber Security Center (ACSC) and the FBI.
Attackers won’t stop unless you hold the door
It may be common knowledge, but it bears repeating: threat actors habitually exploit older vulnerabilities for which exploit or PoC code is available. All of the products described in this post have been targeted by ransomware groups to gain initial entry to networks. Most modern ransomware groups operate as a ransomware-as-a-service, where they provide the malware and infrastructure but rely on affiliates to gain access to organizations in order to deploy their ransomware. Affiliates use a variety of methods to gain entry. Because SSL VPNs provide a doorway into organizations, ransomware affiliates will continue to target these unpatched flaws until organizations take steps to reinforce these entry points by patching vulnerabilities in SSL VPN products.
While our focus here is on a few specific vulnerabilities, the important lesson is that routine patching and maintenance for SSL VPNs is an absolutely critical aspect of cyber hygiene. Three other vulnerabilities in Citrix ADC, Gateway and SD-WAN (CVE-2020-8193, CVE-2020-8195 and CVE-2020-8196) were exploited by attackers last year, including Chinese threat actors that targeted the vulnerabilities we covered in detail here.
Multiple vulnerabilities in Pulse Connect Secure and Fortinet have also been exploited by threat actors, even if they showed a preference for a few specific vulnerabilities. Pulse Connect Secure vulnerabilities are particularly favored by threat actors. There are at least 16 malware families that have been developed to exploit vulnerabilities in Pulse Connect Secure, further solidifying the value of legacy flaws in SSL VPNs for cybercriminals and APT groups. With Fortinet, CVE-2018-13383 and CVE-2018-13382 could be valuable to attackers, particularly in exploit chains. Both of these vulnerabilities were exploited by APT groups.
Addressing these persistently exploited vulnerabilities in SSL VPNs is, perhaps, the easiest prioritization decision for all organizations. Patches have been available for these vulnerabilities for years; attackers of all kinds have been targeting them for just as long. Government agencies have issued multiple alerts advocating immediate action. Creating maintenance windows to update SSL VPNs can be difficult, especially with remote workers distributed across time zones. But if your organization uses one of these products and has not patched the relevant vulnerabilities yet, develop a plan right now to address it. The risk is hard to understate.
Identifying affected systems
A list of Tenable plugins to identify all of the vulnerabilities discussed in this post can be found here. In addition, many of these CVEs were included in our 2020 Threat Landscape Retrospective scan policy, which can be utilized for targeted scans of the CVEs covered in the TLR report.
The scan policy is accessible across Tenable products, including Nessus, Tenable.sc and Tenable.io.
Get more information
- Tenable Threat Landscape Retrospective
- Tenable Blog: Critical Vulnerability in Citrix ADC and Gateway Sees Active Exploitation
- Tenable Blog: Zero-Day Vulnerability in Pulse Connect Secure Exploited in the Wild
- Tenable Blog: FortiGate and Pulse Connect Secure Vulnerabilities Exploited In the Wild
- Joint Government Alert: Top Routinely Exploited Vulnerabilities
Join Tenable's Security Response Team on the Tenable Community.
Learn more about Tenable, the first Cyber Exposure platform for holistic management of your modern attack surface.
Get a free 30-day trial of Tenable.io Vulnerability Management.
Learn more
- Vulnerability Management



Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success