DOUBLEPULSAR Backdoor Detection with Nessus and PVS
Last week many of us in the industry were busy investigating a large cache of weaponized software exploits and payloads released by the ShadowBrokers group. One particular payload that received much attention was the DOUBLEPULSAR implant.
DOUBLEPULSAR is a covert command and control channel that can be used to control a compromised target. While many of the exploits that were released by the Shadow Brokers dump allow attackers to compromise a target, DOUBLEPULSAR can be used to maintain control of that compromised target in a covert manner. Attackers communicate with compromised targets using the Transaction 2 Subcommand Extension SMB feature, a feature that has not officially been used in SMB so far. If a system is compromised, an attacker can gather sensitive data, execute commands, or use the system to launch attacks against other systems in your network.
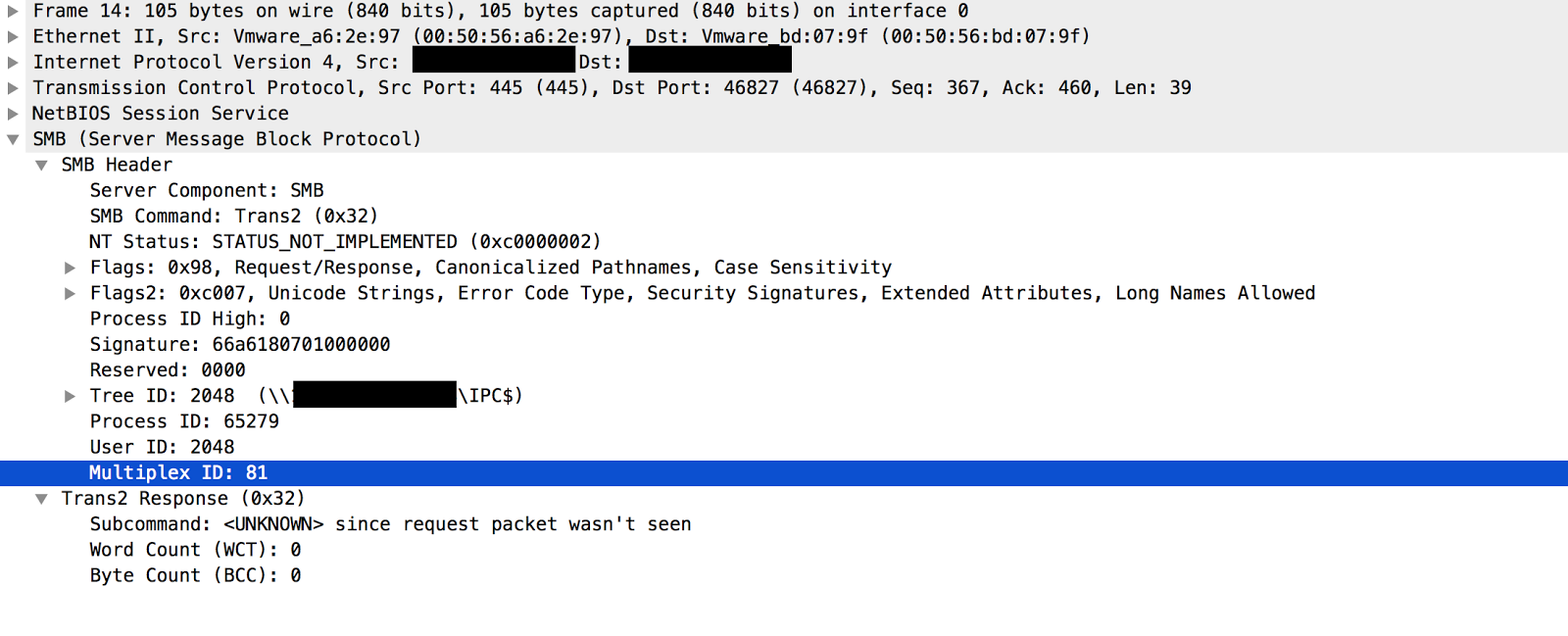
Systems that are compromised by DOUBLEPULSAR will respond to a trans2 SESSION_SETUP with a Not Implemented message that contains a Multiplex ID of 81 while a system that is not compromised will respond with the same message and a Multiplex ID of 65.
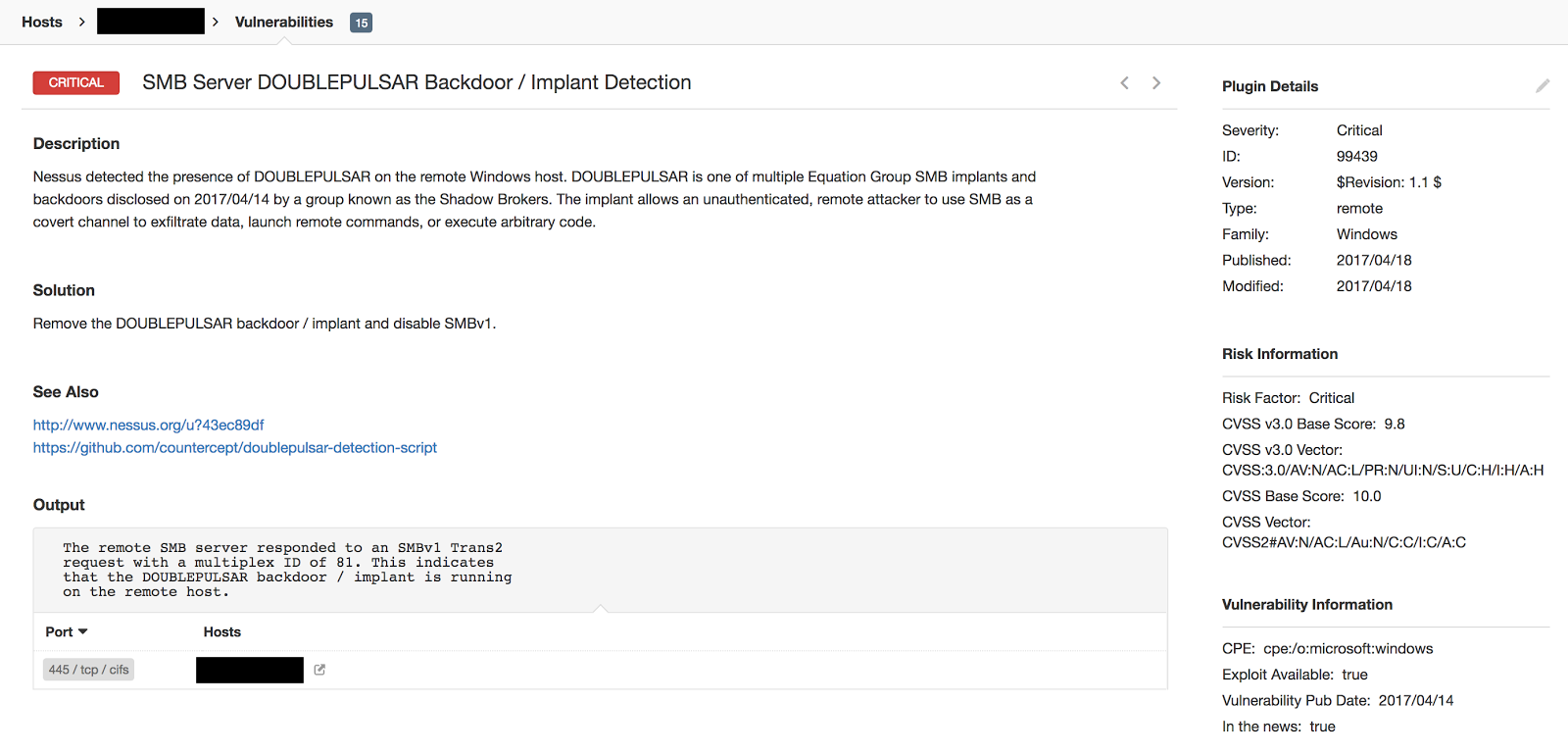
DOUBLEPULSAR can be identified by both Nessus® and PVS™. Tenable customers can use Nessus plugin ID 99439 to actively scan their networks for any hosts that are compromised.
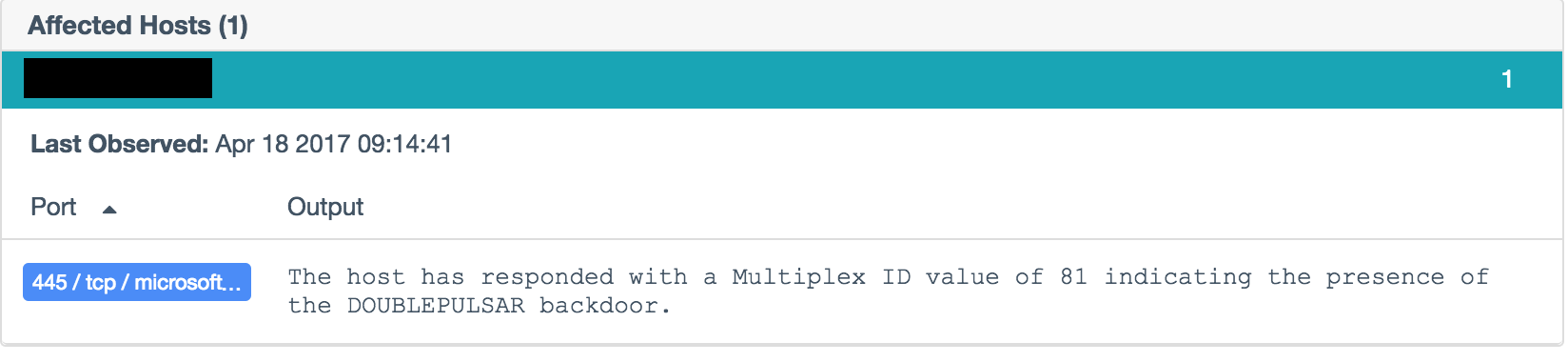
In addition to actively scanning for DOUBLEPULSAR, PVS customers can leverage Plugin 700059 to listen for connections to compromised targets.
Note: Passive Vulnerability Scanner (PVS) is now Nessus Network Monitor. To learn more about this application and its latest capabilities, visit the Nessus Network Monitor web page.
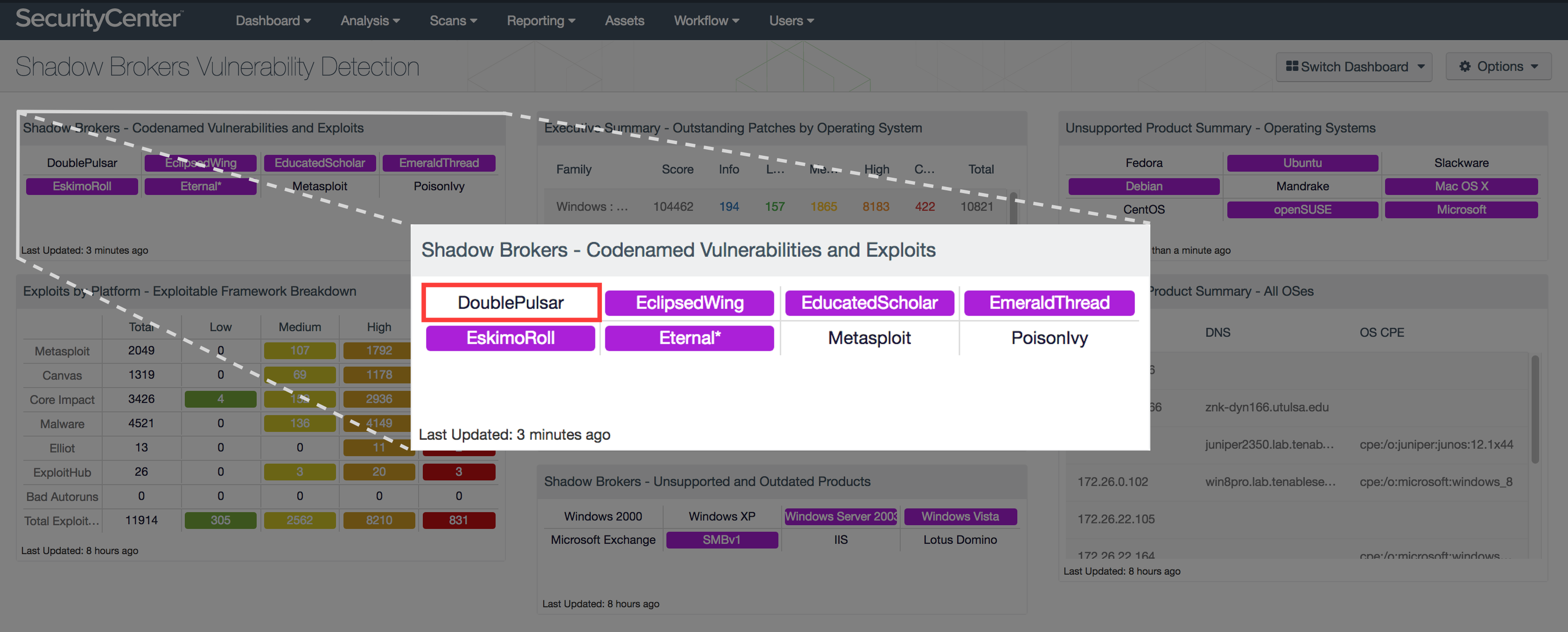
SecurityCenter® users can quickly identify all hosts compromised by DOUBLEPULSAR by leveraging the Shadow Brokers Vulnerability Detection dashboard. This dashboard was updated to include DOUBLEPULSAR, please re-download the dashboard to get the updated matrix.
The presence of DOUBLEPULSAR is not just a potential vulnerability on a system in your network. It means that the target is compromised and can be potentially used to exfiltrate highly sensitive data or run arbitrary commands on the system. There have been reports of scripts actively scanning the internet looking for the existence of this backdoor. By using Nessus and PVS, you can identify any compromised hosts and cut off access.
Many thanks to Andrew Orr and Ian Parker for their contributions to this blog.
Learn more
- Plugins
- Vulnerability Scanning




Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success