CVE-2019-0211: Proof of Concept for Apache Root Privilege Escalation Vulnerability Published
Researcher publishes proof of concept (PoC) for local root privilege escalation bug patched by Apache last week.
Background
Last week, Apache published a security update to address six vulnerabilities in HTTP Server versions 2.4.17 to 2.4.38. This release includes a fix for CVE-2019-0211, a local root privilege escalation vulnerability that could lead to arbitrary code execution.
Analysis
The vulnerability, dubbed CARPE (DIEM), exists in Apache Multi-Processing Modules (MPMs) such as mod_prefork, mod_worker and mod_event. Charles Fol, the researcher who discovered and named the vulnerability, targeted mod_prefork for his breakdown and subsequent PoC.
According to Fol, Apache uses a shared-memory area known as scoreboard to keep tabs on worker processes (lower privileges) managed by mod_prefork (root privileges). Exploitation of this vulnerability requires an attacker to gain read/write access to a worker process (through a separate exploit) in order to manipulate the scoreboard to point to a rogue worker before an Apache graceful restart is initiated by logrotate.
In their advisory, Apache noted that non-Unix systems are unaffected by CVE-2019-0211. This is likely due to the fact that the vulnerability is triggered by an Apache graceful restart (apache2ctl graceful), which is normally executed by logrotate every morning on *Nix systems.
Proof of Concept
Fol published his PoC to Github on April 8. In his blog, he notes this exploit is “between a POC and a proper exploit.” The expectation is now that the PoC is publicly available, it will most likely be refined further and ultimately leveraged by attackers in the wild. This is of great concern on shared hosting environments, where a malicious user could leverage this exploit to gain root access on the host and access files shared by other users on the host environment.
Solution
CVE-2019-0211 is patched in Apache HTTP Server version 2.4.39. *Nix distributions including Ubuntu, Debian, and SuSE have package updates available for install. FreeBSD posted an advisory, but there is no security update available for it yet. Users are encouraged to install these updates as soon as possible.
Additionally, cPanel released a security update for EasyApache 4 that addresses this vulnerability.
Identifying affected systems
A list of Nessus plugins to identify these vulnerabilities will appear here as they’re released.
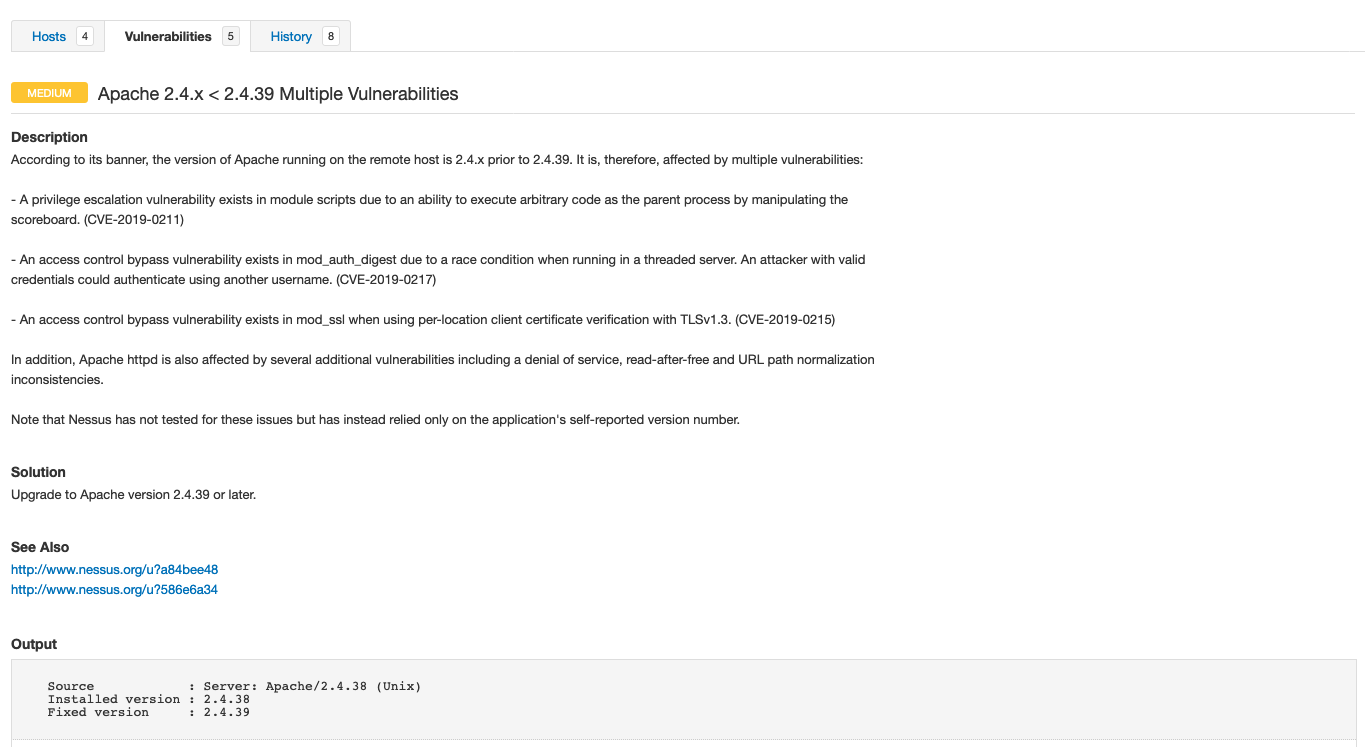
Nessus users scanning for vulnerable versions of Apache HTTP Server will see the following scan output.
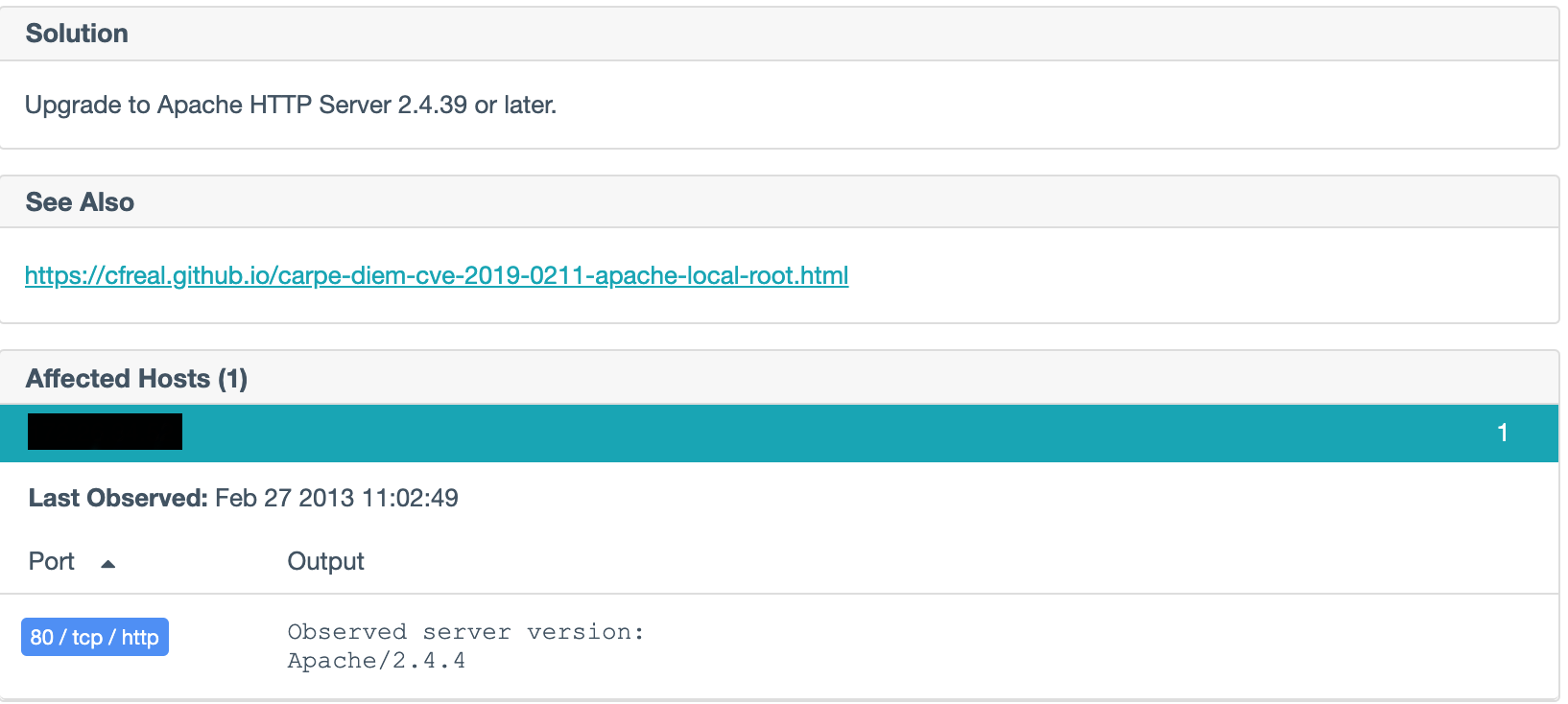
Continuous monitoring via Nessus Network Monitor will result in the following output:
Get more information
- Apache Security Advisory
- Charles Fol's description of CARPE (DIEM)
- Ubuntu Security Advisory
- Debian Security Tracker for CVE-2019-0211
- SuSE: CVE-2019-0211
- FreeBSD: Apache -- Multiple vulnerabilities
- EasyApache 4 Apr 3 Release
Join Tenable's Security Response Team on the Tenable Community.
Learn more about Tenable, the first Cyber Exposure platform for holistic management of your modern attack surface.
Get a free 60-day trial of Tenable.io Vulnerability Management.
Learn more
- Vulnerability Management




Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success