CISA / NSA Alert AA20-205A

Today’s joint alert from the NSA and CISA about malicious activity targeting operational technology (OT) and critical infrastructure should be taken very seriously. Don’t be fooled — this isn’t a warning about the possibility of attacks. This is a warning that attacks have occurred and are ongoing as we speak.
OT is foundational to absolutely everything we do — from the energy we rely on, to the factories manufacturing medical devices, to the water we drink. The country runs on OT. And while our reliance on OT has only increased, so too has the convergence of IT and OT. Internet accessible OT devices are significantly more exposed to outside threats than the near-extinct air-gapped systems of old.
Earlier this year, MITRE updated their framework for Adversarial Tactics, Techniques, and Common Knowledge (ATT&CK) to include ICS and OT Systems. And it is not surprising. Increasingly, OT systems are being targeted by attacks that sometimes originate on the OT side of the house and in other cases traverse from IT to OT as was the case with some of the more recent attacks.
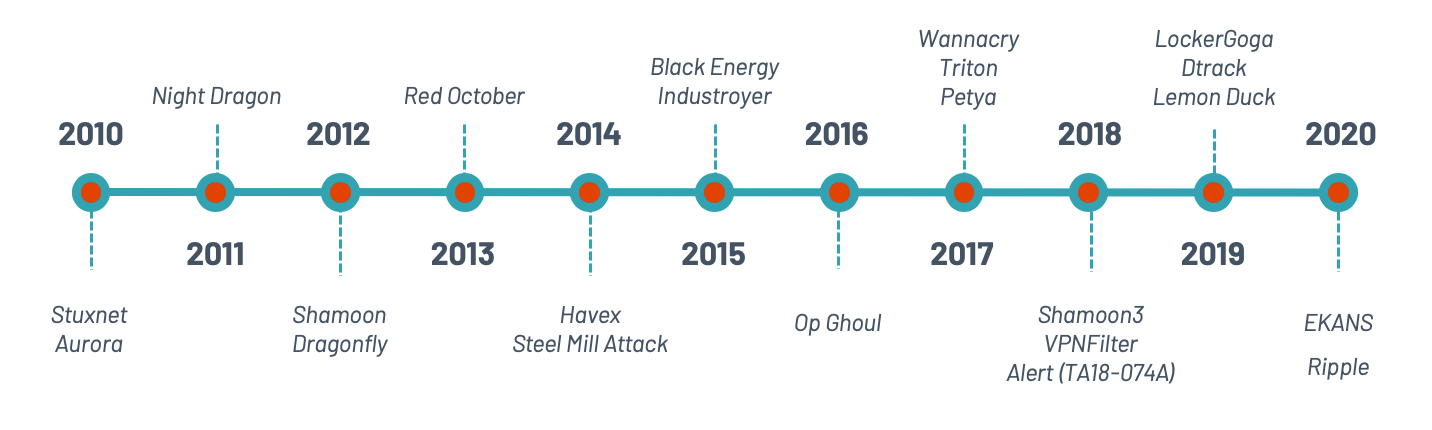
A sample of notable OT attacks over the last decade
The agencies advised that there has been an increase in activity by cyber actors targeting critical infrastructures by exploiting OT assets. The DHS enumerates 16 critical infrastructure (CI) verticals, often referred to as the “DHS-16” in which OT assets play a key role in the operating of these systems. They also play a key role with the Department of Defense (DoD), Defense Industrial Base (DIB) and National Security Systems (NSS).
The evolution of attack surfaces and the increase in attack vectors due to converging IT and OT networks and the rapid adoption of IoT technology has exposed OT networks to cyber exposure in ways they were never designed to defend against. Combining that with a more decentralized workforce and increased targeting of OT systems by criminals, nation states and miscreants puts OT in the crosshairs for attacks.
Some of the more common attack methods include spearfishing, ransomware, and unauthorized changes to PLC logic amongst others.
The alert goes on to recommend specific mitigation techniques broken into 6 key areas:
- Have a resilience plan for OT
- Exercise your incident response plan
- Harden your network
- Create an accurate “as-operated” OT network map immediately
- Understand and evaluate cyber-risk on “as-operated” OT assets
- Implement a continuous and vigilant system monitoring program
To address all of these requirements can sound pretty daunting. The good news is that large portions of the attack surface identified in the alert can be easily addressed with the right OT security system in place. Check out the attached document where we break down the key elements of this directive and show how compliance is within reach.
Save your spot for our August 19th webinar
Hear directly from Tenable’s OT security experts, Marty Edwards and Barak Perelman, on our upcoming August 19th webinar. The session will include a live Q&A and cover immediate actions you can take to strengthen your industrial cybersecurity practice in light of the AA20-205A advisory. You can register here.
Michael Rothschild, contributing author
Learn more
- OT Security



Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success