Adopt The Australian Signals Directorate’s “Strategies To Mitigate Targeted Cyber Intrusions” With Tenable SecurityCenter Continuous View
Today, Tenable Network Security’s Research team announced the release of the latest SecurityCenter Continuous View (SC CV) dashboard to address the Australian Signals Directorate’s (ASD) updated security publication, “Strategies to Mitigate Targeted Cyber Intrusions.”
The Australian Signals Directorate’s updated publication contains a list of 35 strategies to prevent the onslaught of cyber attacks and resulting intrusions into Australian federal and state defence targets. These strategies are widely adopted by commercial organisations as well. The complete publication lays out broadly encompassing guidelines on how to prevent cyber intrusions including:
- Restricting the applications running on devices
- Finding vulnerabilities and applying related patches in a timely manner
- Applying “extreme risk” patches quickly
- Several controls around user access, local user accounts and administrative accounts
- Strict configuration controls for hardware and software assets
- Network segmentation and NIDS
- Email security
While the ASD’s recommended strategies cover a broad range of security techniques, they recognise that using just the Top 4 recommendations can prevent at least 85% of the targeted intrusions.
How Tenable Can Help
The ASD’s Top 4 cyber intrusion mitigation recommendations can help prevent a vast majority of targeted attacks against Australian federal and state targets. The Top 4 is now mandatory for the majority of Australian federal government agencies. The Top 4 strategies are as follows:
- Application Whitelisting – only allow permitted programs to prevent execution of malicious and unknown executables, including DLLs, scripts and installation routines.
- Patch Applications – including MS Office, Java, PDF viewers, Flash and browsers. Apply patches for “extreme risk” vulnerabilities within two days.
- Patch Operating Systems Vulnerabilities – ensure the use of a fully updated OS, and apply patches for “extreme risk” OS vulnerabilities within two days.
- Restrict Administrative Privileges – Only allow privilege access based on user duties and separate non-administrative tasks like email, web browsing, etc. to lower privilege accounts.
Tenable has provided a SecurityCenter CV dashboard for the ASD’s Top 4 mitigation strategies, with critical components that give security analysts an instantaneous view of their security findings. This dashboard leverages SC CV’s abilities to continuously monitor network health, identify vulnerabilities, reduce risk and ensure compliance via SC CV’s unique scanning, network sniffing and log correlation functions. The components in the dashboard include:
- Active OS and Application Vulnerability Counts
- OS & Application Top Remediations
- Application Top Remediations
- OS Top Remediations
- Passive OS and Application Vulnerability Counts
- Group Membership Indicators
- Software Modification Events
- List of Software
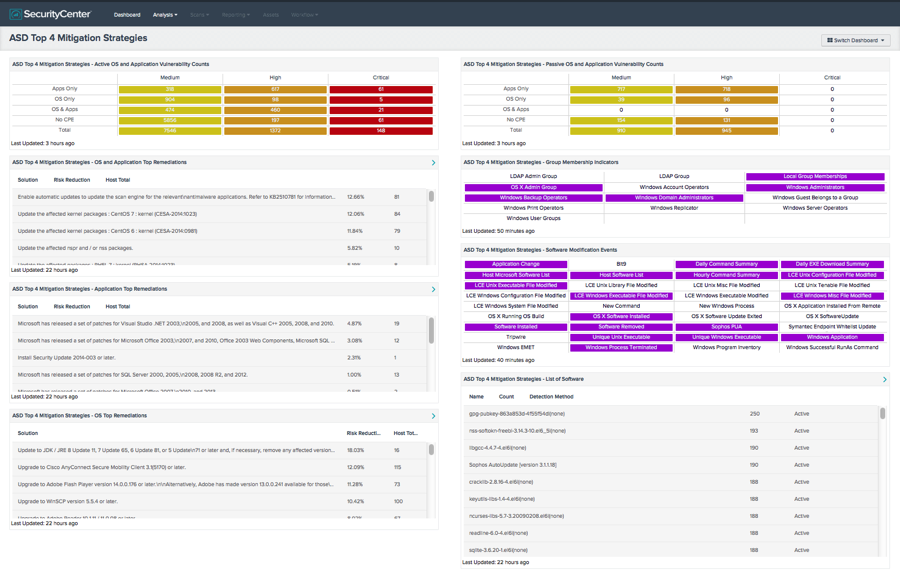
Each of these components provides insight into one of the Top 4 ASD strategies. As with any other SecurityCenter dashboard, analysts can “drill down” and immediately find extremely detailed information. Additionally, the dashboards can be further customised to meet any unique customer-specific requirements.
The ASD publication “Strategies To Mitigate Targeted Cyber Intrusions” can be accessed at the ASD website, and for a more detailed discussion of how Tenable can help, please download the Tenable paper titled “SecurityCenter Continuous View And The Australian Signals Directorate’s Strategies To Mitigate Targeted Cyber Intrusions”. The paper includes the mapping of the majority of the 35 strategies to the capabilities, dashboards and reports included in SecurityCenter CV.
- APAC
- Dashboards
- SecurityCenter
- Standards



