Managing user access and group changes across the enterprise can be a challenging and complex task for any analyst to undertake. Access to internal systems and applications can change due to shifts in user roles and responsibilities, yet users can also retain excessive privileges that can result in data loss. This Assurance Report Card (ARC) will report on user statistics, administrative accounts, and user and group changes that can be used to determine whether current account provisioning policies are effective.
Organizations today are seeing a drive in consumer demand to adopt mobility solutions more than ever before. In order to meet these changes, organizations may need to support access to additional services and applications, allowing end users access to data, systems, and applications from anywhere. As organizations incorporate new devices and technologies, organizations have to manage privileges for hundreds of thousands of user accounts. Managing a large and diverse set of privileges can be complex, and leave privileged users with unnecessary access. Organizations should establish granular control policies to allow users appropriate access quickly, while maintaining the confidentially and integrity of confidential data. This ARC aligns with the access protection controls of the ISO/IEC 27002 framework, which can help to strengthen principles of least privilege and separation of duties across the enterprise.
Attackers routinely target system misconfigurations and other vulnerabilities to elevate system privileges and gain control over systems on a network. Privileged accounts can provide attackers the ability to move laterally, and pivot deeper inside a network. Once a domain or local administrator account is compromised, attackers can move laterally inside the network and access hundreds of other systems within a short period of time. Once inside, confidential data can be exfiltrated, and critical systems can be compromised. To help prevent these attacks, organizations should first assess how users are accessing systems, both internally and externally. Eliminating the number of privileged or unused accounts will help to slow down an attacker’s ability to move through the network. This information will help to increase awareness, and allow organization to defend against persistent attackers.
This ARC provides a baseline that can be used to measure if current user access control policies in place are effective. Several policy statements focus on accounts that have never been logged on or have been disabled. Best practice suggests deleting unused accounts to reduce security risks. Systems that are connected to administrative account activity should be continuously monitored to ensure authorized access.
Additional policy statements will alert analysts to user accounts with passwords that do not expire. Attackers can harvest and crack passwords using readily available tools. Having password changing, complexity, and expiration policies in place can help organizations reduce the chance of potential security breaches.
This ARC is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The ARC can be easily located in the Feed under the category Compliance. The ARC requirements are:
- Tenable.sc 5.3.2
- Nessus 8.5.1
- LCE 6.0.0
- NNM 5.9.1
Tenable's Tenable.sc Continuous View (Tenable.sc CV) is the market-defining continuous network monitoring platform. Tenable.sc CV includes active vulnerability detection with Tenable Nessus and passive vulnerability detection with Tenable Nessus Network Monitor (NNM), as well as log correlation with Tenable Log Correlation Engine (LCE). Tenable.sc CV can help an organization continuously monitor and measure the effectiveness of security controls. Using Tenable.sc CV, an organization will obtain the most comprehensive and integrated view of its network devices and user access controls.
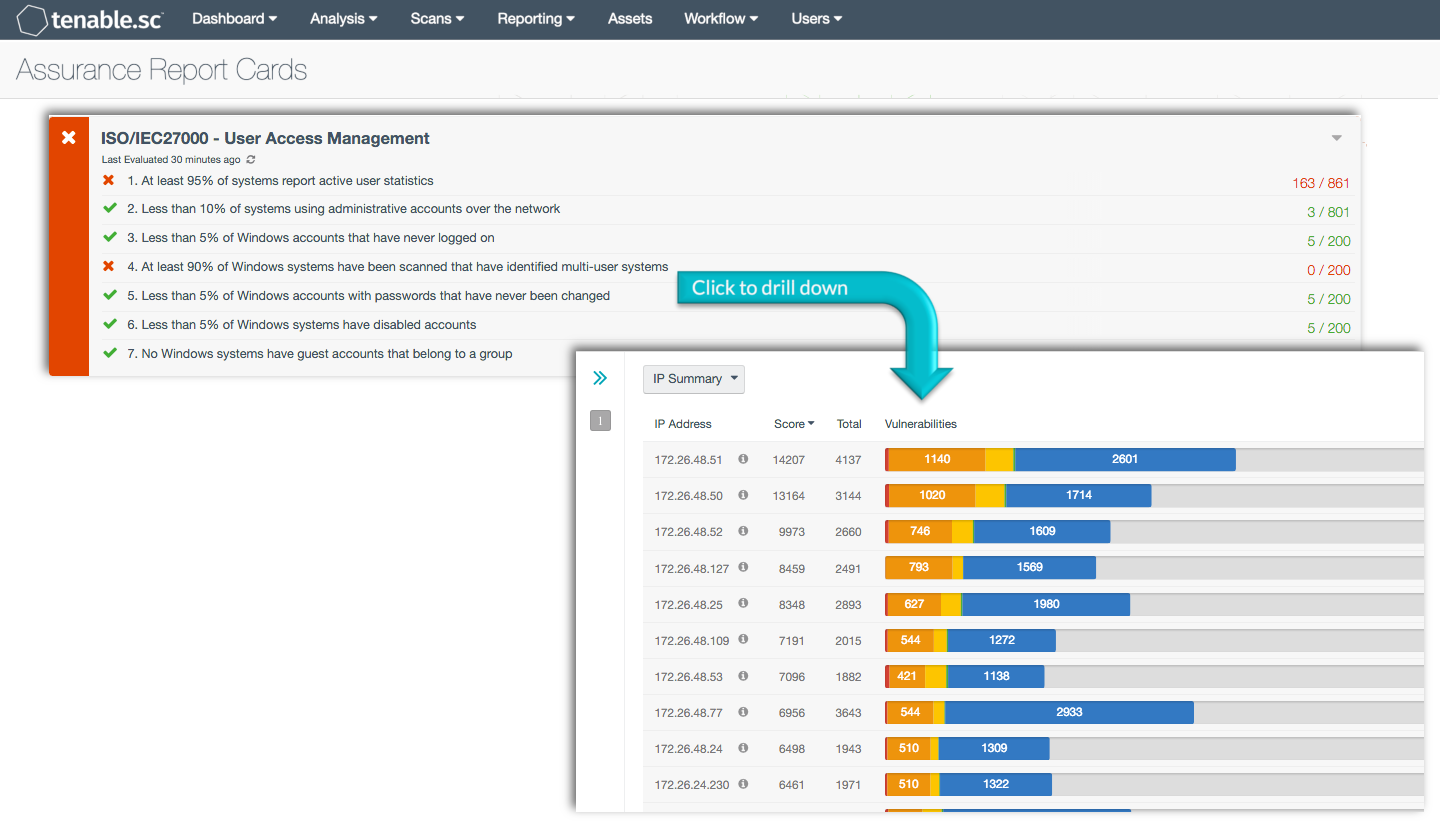
ARC Policy Statements:
At least 95% of systems report active user statistics: This policy statement displays the number of systems that report active user statistics compared to total systems. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. LCE can gather user statistics from systems on a network. All systems should be reporting user statistics to LCE to ensure that access controls can be effectively implemented and monitored.
Less than 10% of systems are using administrative accounts over the network: This policy statement displays the number of systems using administrative accounts over the network compared to total systems. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. This policy monitors systems for the use of administrative accounts over the network, which should be limited to a defined list of systems. Any unexpected systems using administrative accounts over the network should be considered suspicious.
Less than 5% of Windows accounts that have never logged on: This policy statement displays the number of Windows accounts that have never logged on compared to total Windows systems. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. User accounts that have never been used could be used by attackers to gain access to the network. Organizations should review both local and domain accounts that have never been used, as this may indicate the presence of unauthorized accounts on the network.
At least 90% of Windows systems have been scanned that have identified multi-user systems: This policy statement displays the number of Windows systems that are reporting multiple users compared to all Windows systems. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. Many organizations allow users to access and share data on a system. Organizations should review user rights on a regular basis to determine if the user is authorized to access the system.
Less than 5% of Windows accounts with passwords that have never been changed: This policy statement displays the number of Windows accounts with passwords that have never been changed compared to all Windows systems. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. Accounts with passwords that do not expire, or have never been changed can present serious security risks to the organization. Organizations should review current security policies to determine if password expiration and complexity policies are being enforced.
Less than 5% of Windows systems have disabled accounts: This policy statement displays the number of Windows systems that have disabled accounts compared to all Windows systems. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. Systems with disabled accounts are potentially vulnerable to exploitation. The disabled accounts should be deleted in order to ensure that they are not used for malicious purposes.
No Windows systems have guest accounts that belong to a group: This policy statement displays the number of Windows systems reporting guest accounts that belong to a group compared to all Windows systems. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. Systems that have guest accounts belonging to a local or domain group may indicate the presence of malicious or unauthorized users on the network. Guest users should not have any access to local or domain groups. Best practice is to edit local and/or domain policies to restrict and prevent access rights for all guest accounts.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success