by Cody Dumont
June 20, 2016
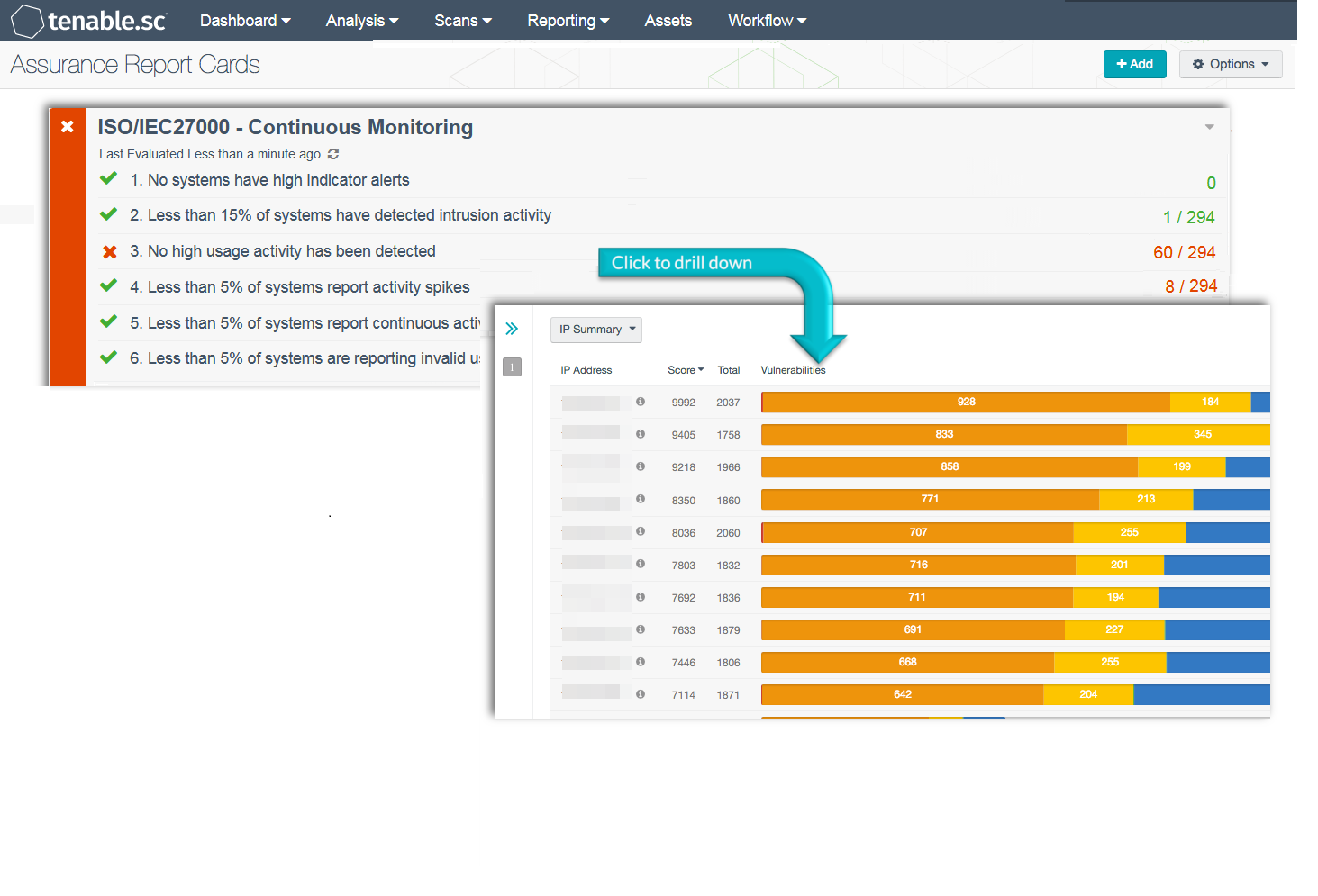
As organizations deploy more devices on a network, many of these devices are intermittently scanned or missed all together. Unknown and unscanned devices can be missed between scans, which can allow malware to infiltrate critical systems across the enterprise. This Assurance Report Card (ARC) provides information from devices reporting high utilization and intrusion events, which can be useful in detecting blind spots and improving an organization’s continuous monitoring efforts.
Continuous monitoring can provide a comprehensive assessment of an organization’s current security posture and insight into whether existing security controls are effective. Organizations will be able to quickly identify new assets, remove unauthorized assets, and remediate detected vulnerabilities. This ARC aligns with the logging and monitoring controls of the ISO/IEC 27002 framework, which will monitor changes and event spikes on an organization’s most critical assets.
Organizations cannot afford to rely on traditional security devices and tools to protect against attacks and breaches. Shifting to a continuous monitoring strategy will help organizations to understand how attackers are gaining access to network resources. One of the first steps organizations can implement as part of an effective continuous monitoring strategy is utilizing Tenable Log Correlation Engine (LCE). LCE provides a centralized location to analyze user and network activity from any device within a network. Log management can be enhanced further by installing LCE Clients on servers, and if possible on workstations. Events can alert analysts to malicious activity, unexpected behavior, or systems with problems that need immediate attention.
The information provided in this ARC provides a summary of suspicious activity and high utilization events on network devices. Policy statements will report on intrusion events, network anomalies, password guessing attempts, and hosts that may have been compromised. Additional policy statements will report on performance issues with hosts, port scanning, and repeated login failure attempts. Policy statements included within this ARC are guides that can be customized as necessary to meet organizational requirements. Using this ARC, organizations will be able to detect issues in near real time and proactively address incidents before critical systems are impacted.
This ARC is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The ARC can be easily located in the Feed under the category Compliance. The ARC requirements are:
- Tenable.sc 5.3.0
- Nessus 8.5.1
- LCE 6.0.0
- NNM 5.9.0
Tenable.sc Continuous View (CV) is the market-defining continuous network monitoring platform. Tenable Log Correlation Engine (LCE) performs automatic discovery of users, infrastructure, and vulnerabilities across more technologies than any other vendor including operating systems, network devices, hypervisors, databases, tablets, phones, web servers, and critical infrastructure. Tenable Nessus is continuously updated with information about advanced threats and zero-day vulnerabilities, and new types of regulatory compliance configuration audits. Tenable.sc CV’s proactive continuous monitoring identifies your biggest risk across the entire enterprise.
ARC Policy Statements:
No systems have high indicator alerts: This policy statement displays the number of systems with high indicator alert events to total systems. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. High indicator alert events indicate that a suspicious sequence of 10 or more events occurred. Events could also be the result of denial of service attacks, suspicious network connections, or malicious code being executed.
Less than 15% of systems have detected intrusion activity: This policy statement displays the number of systems on which intrusion activity has been detected to total systems. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. Intrusion events include password guessing, IDS events, and network sweeps, among other things. Intrusion events could indicate ongoing attacks or hosts that have been compromised.
No high usage activity has been detected: This policy statement displays the number of systems reporting high usage activity to total systems. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. High usage events are detected by LCE and include events such as high memory, high CPU, or high disk usage. High usage on systems could indicate potential attacks, malicious activity, or performance issues with the host. High usage can affect performance and overwhelm critical systems on a network and should be further investigated to determine the cause.
Less than 5% of systems report activity spikes: This policy statement displays the number of systems reporting activity spikes to total systems. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. Activity detected by LCE for the current hour is compared to the same hour in all previous days for each IP address. Any large anomalies (spikes) in activity will be automatically reported by LCE. Activity spikes could indicate malicious behavior or network issues and should be investigated further by the organization to determine the cause.
Less than 5% of systems report continuous activity: This policy statement displays the number of systems reporting continuous activity to total systems. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. Continuous activity is activity occurring over a long period of time. The activity may be legitimate, or it may be activity such as port scanning, server issues, repeated login failures, or potential malware activity. The organization should further investigate any systems with continuous activity.
Less than 5% of systems are reporting invalid user login attempts: This policy statement displays the number of systems reporting invalid user login attempts to total systems. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. Invalid login attempts can indicate brute force attacks by attackers using invalid usernames. Organizations should review all unauthorized or invalid login attempts to determine the source and prevent future attacks.