by Cody Dumont
June 10, 2014
The OpenSSL ChangeCipherSpec vulnerability is a Man-in-the-Middle vulnerability that can allow an attacker to eavesdrop or modify the traffic between a client and a server. This vulnerability was published in 2014 and affects all versions of OpenSSL prior to 0.9.8y, OpenSSL 1.0.0 through 1.0.0l, and OpenSSL 1.0.1 through 1.0.1g. Security professionals and administrators within an organization must be alerted to these OpenSSL ChangeCipherSpec vulnerabilities so they can take appropriate corrective actions. Upgrading OpenSSL to version 1.0.1h or newer is the best approach to resolve this vulnerability.
Man-in-the-Middle (MitM) vulnerabilities allow an attacker to insert himself into a communication channel. While each of the endpoints assumes they are communicating directly with each other, in reality all the traffic is flowing through the attacker. This allows the attacker to eavesdrop on or even modify the traffic being sent back and forth, resulting in a loss of data confidentiality and integrity.
Typically MitM attacks are difficult to achieve, but they are becoming more prevalent in today's world of open WiFi. In general, the best practice to prevent MitM attacks is to ensure that all communications are encrypted and that users only accept certificates from trusted servers. Accepting only trusted certificates prevents a user from accepting communications from a MitM attacker posing as the server. Keeping all infrastructure and applications fully updated and patched ensures that attackers cannot exploit any communication channel vulnerabilities.
This report makes use of the following CVEs to present active, passive and host event-based detections of OpenSSL ChangeCipherSpec vulnerabilities on the network:
- CVE-2014-0224 - SSL/TLS MITM Vulnerability
- CVE-2014-0221 - DTLS recursion flaw
- CVE-2014-0195 - DTLS invalid fragment vulnerability
- CVE-2014-0198 - SSL_MODE_RELEASE_BUFFERS NULL pointer dereference
- CVE-2010-5298 - SSL_MODE_RELEASE_BUFFERS session injection
- CVE-2014-3470 - Anonymous ECDH Denial of Service
In addition, this report presents general OpenSSL vulnerabilities so that these vulnerabilities can be mitigated.
The report is available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards and assets. The report can be easily located in the SecurityCenter Feed under the category Security Industry Trends. The report requirements are:
- SecurityCenter 4.8.1
- Nessus 6.11.2
- Nessus Network Monitor 5.4.0
- LCE 5.0.2
Tenable SecurityCenter Continuous View® (SecurityCenter CV™) provides continuous network monitoring, vulnerability identification and security monitoring. SecurityCenter CV is continuously updated with information about advanced threats, zero-day vulnerabilities and new types of regulatory compliance. Information from Tenable's unique sensors is constantly analyzed, delivering continuous visibility and critical context, and enabling decisive action that transforms a security program from reactive to proactive. Active scanning periodically examines systems to determine vulnerabilities and compliance concerns. Passive listening collects data to continuously detect devices and monitor network connections and activity. Host data and data from other security investments is collected and analyzed to monitor activity, identify new assets, and detect anomalies and malicious behavior. SecurityCenter CV provides an organization with the most comprehensive view of the network and the intelligence needed to most effectively reduce risk within the enterprise.
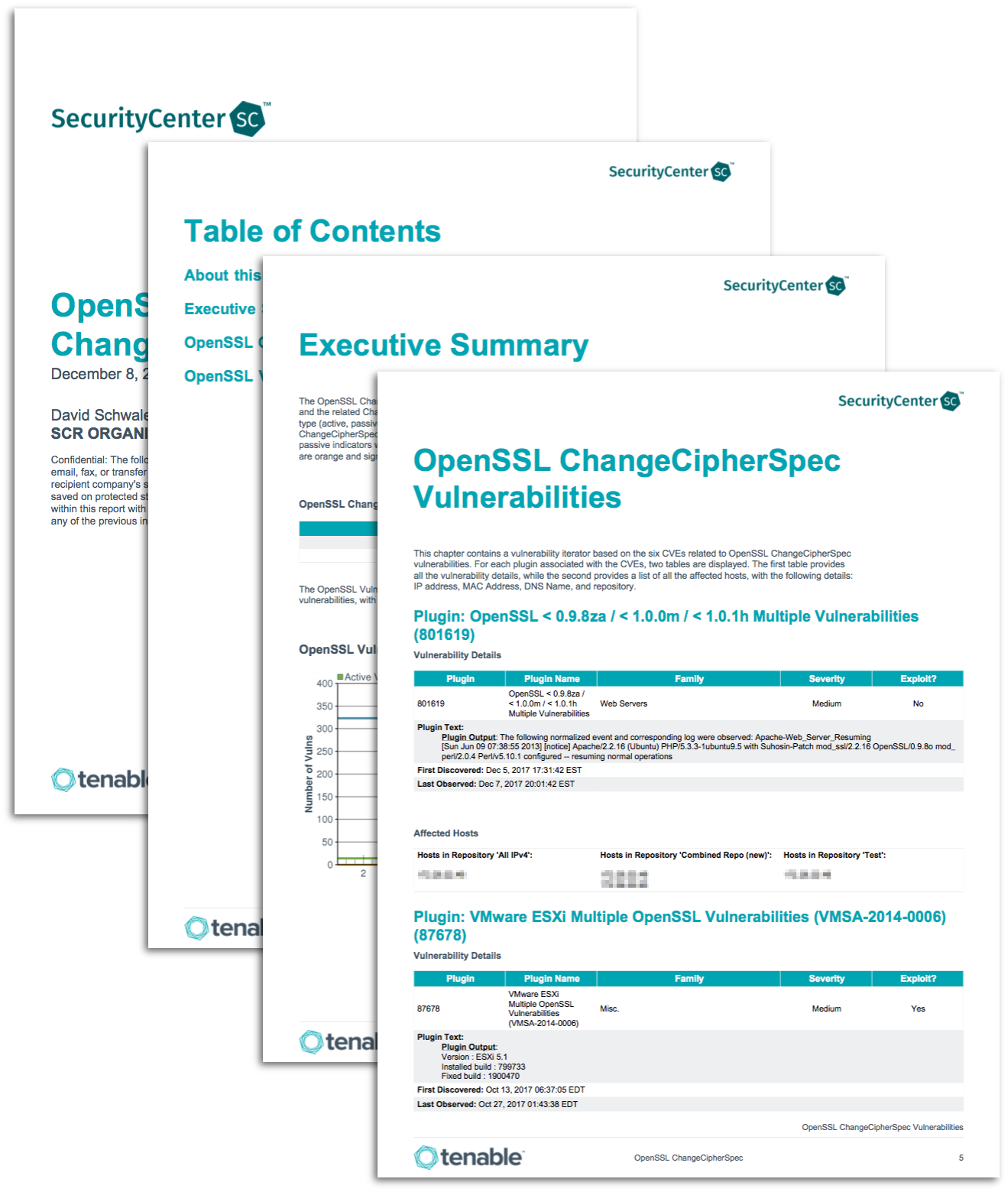
This report contains the following chapters:
Executive Summary: This chapter contains an executive level overview of current OpenSSL ChangeCipherSpec and general OpenSSL vulnerabilities on the network.
OpenSSL ChangeCipherSpec Vulnerabilities: This chapter provides a list of vulnerability detections associated with the six CVEs related to the OpenSSL ChangeCipherSpec vulnerability. For each detection, the vulnerability details and a list of affected systems are provided.
OpenSSL Vulnerabilities: This chapter provides a list of vulnerability detections associated with general OpenSSL vulnerabilities. For each detection, the vulnerability details and a list of affected systems are provided.