Oracle Critical Patch Update for July 2020 Tops Previous Record with 443 Security Updates
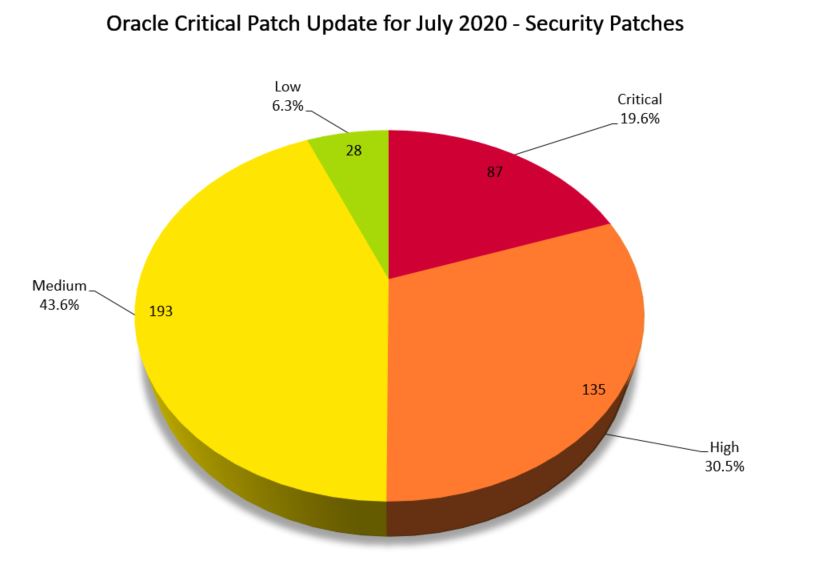
Oracle’s third Critical Patch Update of 2020 contains a record-breaking 443 security patches addressing 284 CVEs, including critical vulnerabilities in Oracle Communications Applications and Oracle Fusion Middleware products.
Update July 20, 2020: A proof of concept script has become publicly available for CVE-2020-14645. The proof of concept section of our blog has been updated accordingly.
Background
On July 14, Oracle released the Critical Patch Update (CPU) Advisory for July 2020 as part of their quarterly release of security patches. This update contains fixes for 284 CVEs in 443 security patches across 29 Oracle product families. This quarter’s update continues an upward trend, overtaking the previous Oracle CPU patch record set by April 2020's update.
Analysis
This quarter’s CPU includes more than 30 critically rated CVEs across a wide range of Oracle products. The following is the full list of product families with vulnerabilities addressed in this month’s release along with the number of patches released and vulnerabilities that are remotely exploitable without authentication.
| Oracle Product Family | Number of Patches | Remote Exploit without Auth |
|---|---|---|
| Oracle Communications Applications | 60 | 46 |
| Oracle Fusion Middleware | 52 | 48 |
| Oracle Retail Applications | 47 | 42 |
| Oracle MySQL | 40 | 6 |
| Oracle Financial Services Applications | 38 | 26 |
| Oracle E-Business Suite | 30 | 24 |
| Oracle Virtualization | 25 | 0 |
| Oracle Supply Chain | 22 | 18 |
| Oracle Construction and Engineering | 20 | 15 |
| Oracle Database Server | 19 | 1 |
| Oracle Enterprise Manager | 14 | 10 |
| Oracle Java SE | 11 | 11 |
| Oracle PeopleSoft | 11 | 9 |
| Oracle Systems | 7 | 1 |
| Oracle Insurance Applications | 6 | 4 |
| Oracle JD Edwards | 6 | 6 |
| Oracle Siebel CRM | 5 | 5 |
| Oracle Commerce | 4 | 3 |
| Oracle Food and Beverage Applications | 4 | 0 |
| Oracle GraalVM | 4 | 3 |
| Oracle Health Sciences Applications | 4 | 4 |
| Oracle Berkeley DB | 3 | 0 |
| Oracle GoldenGate | 3 | 1 |
| Oracle Hyperion | 3 | 0 |
| Oracle Global Lifecycle Management | 1 | 0 |
| Oracle TimesTen In-Memory Database | 1 | 0 |
| Oracle Hospitality Applications | 1 | 1 |
| Oracle iLearning | 1 | 1 |
| Oracle Utilities Applications | 1 | 1 |
Notable Vulnerabilities
Considering the large number of patches released in this quarter’s CPU, it may be hard to digest, filter and prioritize these vulnerabilities. However, a few notable vulnerabilities stand out due to their criticality and potential for being targeted by attackers.
CVE-2020-14701 and CVE-2020-14706 | Oracle Communications Applications SD-WAN Aware / Edge Vulnerabilities
CVE-2020-14701 and CVE-2020-14706 are vulnerabilities in the User Interface component of the Oracle Communications Applications SD-WAN Aware and SD-WAN Edge products respectively. Oracle has highlighted these vulnerabilities as “easily exploitable” as they allow an unauthenticated attacker with network access via the Hypertext Transfer Protocol (HTTP) to compromise SD-WAN Aware and SD-WAN Edge.
Successful exploitation of these vulnerabilities would result in a complete takeover of SD-WAN Aware and SD-WAN Edge. While the vulnerabilities are in these products, Oracle has noted that “attacks may significantly impact additional products.” These are the only details currently available from Oracle, though the company has assigned both vulnerabilities a CVSSv3.1 score of 10.0, the highest score possible, suggesting easy exploitability with potentially significant impact, making them important vulnerabilities to prioritize.
CVE-2020-14625, CVE-2020-14644, CVE-2020-14645 and CVE-2020-14687 | Oracle Fusion Middleware WebLogic Server Vulnerabilities
CVE-2020-14625, CVE-2020-14644, CVE-2020-14645, and CVE-2020-14687 are vulnerabilities in the Core component of the Oracle WebLogic product of Oracle Fusion Middleware. Oracle has highlighted these vulnerabilities as “easily exploitable” as they allow an unauthenticated attacker with network access via Oracle’s T3 and Internet Inter-ORB Protocol (IIOP) to compromise the server.
Successful exploitation of these vulnerabilities would allow an attacker to gain full control over the Oracle WebLogic Server. Given their ease of exploitation, Oracle has assigned these vulnerabilities a critical CVSSv3.1 score of 9.8. Oracle WebLogic vulnerabilities regularly appear in the quarterly CPU advisories and historically have been prime targets for exploitation. Less than one month after the April 2020 CPU, CVE-2020-2883, an Oracle WebLogic vulnerability, was reported as exploited in the wild. This prompted Oracle to release a separate alert urging people to patch as soon as possible.
Proof of Concept
Security researcher “Y4er” published a PoC to a GitHub repository on July 19 for CVE-2020-14645. Y4er is also responsible for publishing a PoC for CVE-2020-2883 on May 10, less than two weeks after it was reported as exploited in-the-wild.
Solution
Customers are advised to apply all relevant patches provided by Oracle in this CPU. Please refer to the July 2020 advisory for full details.
Identifying affected systems
A list of Tenable plugins to identify these vulnerabilities will appear here as they’re released.
Get more information
- Oracle Critical Patch Update Advisory - July 2020
- Oracle Advisory to CVE Map
- Oracle July 2020 CPU Risk Matrices
Join Tenable's Security Response Team on the Tenable Community.
Learn more about Tenable, the first Cyber Exposure platform for holistic management of your modern attack surface.
Get a free 30-day trial of Tenable.io Vulnerability Management.
Learn more
- Vulnerability Management



Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success