Microsoft Data Sharing Service Zero-Day Exploit Released on Twitter (CVE-2018-8584)
Researcher discloses privilege escalation zero-day in Microsoft’s Data Sharing Service on Twitter and provides a proof-of-concept that could be used to deploy attacks in the wild.
Background
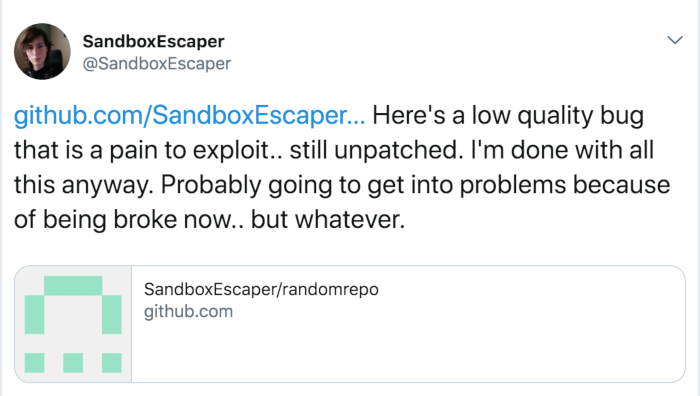
On October 23, a privilege escalation zero-day vulnerability in Microsoft’s Data Sharing Service (dssvc.dll), a broker for sharing data between applications, was published to Twitter. The researcher who published this vulnerability also released a zero-day exploit in Microsoft’s Windows Task Scheduler on Twitter in August 2018. As with the Task Scheduler vulnerability disclosed previously, the researcher shared a proof-of-concept (PoC) on GitHub.
Vulnerability details
The PoC shared by the researcher deletes files on the system that normally require administrative privileges. By deleting these files, the PoC demonstrates the bug is capable of elevating privileges. The PoC could be modified by an attacker to perform other tasks that require elevated privileges.
Please be advised that the PoC deletes a critical system file which can render the system inoperable.
According to initial reports, this vulnerability affects Windows 10, Windows Server 2016 and Windows Server 2019 systems. Also note this vulnerability requires that a malicious actor already have presence on an infected system (using malicious software) or utilize a separate vulnerability to establish a presence on a targeted system.
Urgently required actions
It is unclear if Microsoft will issue a patch for this vulnerability in time for the next Security Update in November 2018. Until a patch is available, we strongly encourage utilizing best security practices. This includes mitigation strategies, as attackers are likely to use malware when deploying this vulnerability. Additionally, ensure proper access control and network segmentation is in place.
Updated November 14: It appears Microsoft has patched this vulnerability in the November 2018 Security Update. It received a CVE identifier of CVE-2018-8584. While the information does not reference the Data Sharing Service, several indicators including the affected Operating Systems and the impact of successful exploitation lead us to believe that this CVE addresses the vulnerability reported in this blog.
Identifying affected systems
A list of Tenable plugins to identify this vulnerability can be found here.
Get more information
Learn more about Tenable.io, the first Cyber Exposure platform for holistic management of your modern attack surface. Get a free 60-day trial of Tenable.io Vulnerability Management.
Learn more
- Vulnerability Management




Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success