Microsoft’s April 2020 Patch Tuesday Addresses 113 CVEs Including Adobe Type Manager Library Zero-Day Flaws (CVE-2020-0938, CVE-2020-1020)
Microsoft's April 2020 Patch Tuesday includes 113 CVEs, including a patch for two zero-day flaws (CVE-2020-0938 and CVE-2020-1020) in Adobe Type Manager Library.
Update April 14, 2020: This post has been updated to reflect changes regarding the number of vulnerabilities exploited in the wild as well as updates to the Adobe Type Manager Library and Scripting Engine sections.
Microsoft addressed 113 CVEs in the April 2020 Patch Tuesday release, marking the second month in a row that Microsoft has patched over 100 CVEs; the March 2020 Patch Tuesday contained fixes for 115 CVEs. Of the 113 CVEs, 19 were rated as critical. Two vulnerabilities were publicly disclosed prior to Patch Tuesday. Initially, we reported that four vulnerabilities were exploited in the wild. However, Microsoft updated the exploit status for one of those vulnerabilities, decreasing the count to three.
This update contains patches for 39 remote code execution flaws as well as 38 elevation of privilege vulnerabilities, including fixes for Microsoft Windows, Microsoft Edge, Microsoft Office, Internet Explorer, ChakraCore, Windows Defender, Visual Studio, Microsoft Office Services and Web Apps and Microsoft Dynamics. The following is a breakdown of the most important CVEs from this month’s release.
CVE-2020-1020 and CVE-2020-0938 | Adobe Type Manager Library Remote Code Execution Vulnerabilities
CVE-2020-0938 and CVE-2020-1020 are vulnerabilities in the way that Windows parses OpenType fonts. Successful exploitation would require an attacker to convince a victim to open a malicious document or visit a malicious page that exploits the WebClient service, which is normally listening for WebDAV file shares. On March 23, Microsoft issued an advisory, ADV200006, due to a report of in-the-wild exploitation. At the time, Microsoft had not yet assigned a CVE identifier. As part of Patch Tuesday, it has since confirmed that ADV200006 applies to CVE-2020-1020. Get more information in our blog post for this advisory.
CVE-2020-0687 and CVE-2020-0907 | Microsoft Graphics Remote Code Execution Vulnerabilities
CVE-2020-0687 and CVE-2020-0907 are both remote code execution vulnerabilities in Microsoft Graphics and Microsoft Graphics Components, which could allow an attacker to take control of a system and execute arbitrary code. CVE-2020-0687 is the result of the Windows font library improperly handling specially crafted embedded fonts. CVE-2020-0907 exists due to how Microsoft Graphics Components handles objects in memory. In each of these cases, an attacker would need to convince a victim to either open a specially crafted file or visit a specially crafted webpage. Microsoft gives these CVEs a rating of ‘exploitation less likely’ due to the user interaction required to successfully exploit these flaws.
CVE-2020-0935 | OneDrive for Windows Elevation of Privilege Vulnerability
CVE-2020-0935 is an elevation of privilege vulnerability in OneDrive for Windows due to the desktop application improperly handling symbolic links. An attacker who logs on to the system could execute a specially crafted application to exploit this vulnerability to overwrite a targeted file. This vulnerability has been publicly disclosed and Microsoft’s advisory notes that most customers are protected because OneDrive has its own updater. However, customers who have an air-gapped network will need to update the OneDrive binary from Microsoft to be protected.
CVE-2020-0968 | Scripting Engine Memory Corruption Vulnerability
CVE-2020-0968 is a memory corruption vulnerability in Internet Explorer due to the improper handling of objects in memory by the scripting engine. Initially, Microsoft reported that this vulnerability had been exploited in the wild, but it has since updated the exploit status for this advisory, clarifying that it had not been exploited. However, there are multiple scenarios in which this vulnerability could be exploited. An attacker could convince a victim to visit a website containing malicious code, whether or not that website is owned by the attacker, or a compromised website with malicious code injected into it. Another scenario would require the attacker to embed the malicious code into a Microsoft Office document and convince the victim to open it.
CVE-2020-0948, CVE-2020-0949 and CVE-2020-0950 | Media Foundation Memory Corruption Vulnerabilities
CVE-2020-0948, CVE-2020-0949 and CVE-2020-0950 are memory corruption vulnerabilities that exist when Windows Media Foundation improperly handles objects in memory. Successful exploitation of this vulnerability could allow the installation of programs, the reading, alteration or deletion of data or the creation of new accounts with full user rights. To exploit these vulnerabilities, an attacker would need to convince a victim to open a specially crafted file or visit a malicious website.
CVE-2020-0953, CVE-2020-0988, CVE-2020-1008, CVE-2020-0995, CVE-2020-0994, CVE-2020-0992, CVE-2020-0999, CVE-2020-0889, CVE-2020-0959 and CVE-2020-0960 | Jet Database Engine Remote Code Execution Vulnerabilities
CVE-2020-0953, CVE-2020-0988, CVE-2020-1008, CVE-2020-0995, CVE-2020-0994, CVE-2020-0992, CVE-2020-0999, CVE-2020-0889, CVE-2020-0959 and CVE-2020-0960 are remote code execution vulnerabilities that exist when the Windows Jet Database Engine improperly handles objects in memory. Successful exploitation of these vulnerabilities could allow an attacker to execute arbitrary code on a vulnerable system. To exploit them, an attacker would need to convince a victim to open a specially crafted file.
CVE-2020-0910 | Windows Hyper-V Remote Code Execution Vulnerability
CVE-2020-0910 is a remote code execution vulnerability that exists when Windows Hyper-V on a host server fails to properly validate input from an authenticated user on a guest operating system. Exploitation of this vulnerability allows an attack on a guest operating system to execute a crafted application that could cause the Hyper-V host operating system to execute arbitrary code. While this vulnerability could be mitigated by restricted rights by access controls, CVE-2020-0917 and CVE-2020-0918, a pair of privilege escalation vulnerabilities in Windows Hyper-V, could be used to gain elevated privileges on a target operating system due to the way in which Windows Hyper-V handles objects in memory.
CVE-2020-0920, CVE-2020-0929, CVE-2020-0931, CVE-2020-0932, CVE-2020-0971 and CVE-2020-0974 | Microsoft SharePoint Remote Code Execution Vulnerabilities
CVE-2020-0920, CVE-2020-0929, CVE-2020-0931, CVE-2020-0932, CVE-2020-0971 and CVE-2020-0974 are remote code execution vulnerabilities that exist in Microsoft SharePoint when the software fails to check the source markup of an application package. Successful exploitation of these vulnerabilities could allow an attacker to run arbitrary code with the permissions of the SharePoint application pool and SharePoint server farm account. To exploit them, an attacker, with administrator privileges, would need to upload a specially crafted SharePoint application package to a vulnerable version of SharePoint.
CVE-2020-1022 | Dynamics Business Central Remote Code Execution Vulnerability
CVE-2020-1022 is a remote code execution vulnerability in Microsoft Dynamics Business Central. To exploit the vulnerability, an authenticated attacker would need to convince a victim to connect to a malicious client. Exploitation of this vulnerability could allow an attacker to execute shell commands on the vulnerable Dynamics Business Central server.
CVE-2020-0913, CVE-2020-1000, CVE-2020-1003 and CVE-2020-1027 | Windows Kernel Elevation of Privilege Vulnerabilities
CVE-2020-0913, CVE-2020-1000, CVE-2020-1003 and CVE-2020-1027 are elevation of privilege flaws due to the Windows kernel failing to properly handle objects in memory. CVE-2020-0913, CVE-2020-1000 and CVE-2020-1003 can be exploited to execute arbitrary code in kernel mode, but would require an attacker to first log on to the system. CVE-2020-1027 could allow a locally authenticated user to execute code with elevated privileges. This vulnerability was reported to Microsoft by Google Project Zero, after it was discovered being exploited in the wild.
We discovered CVE-2020-1027 being exploited in the wild and reported it on 23 March under a 7-day deadline (used only for actively exploited bugs). Microsoft asked for an extension due to current global circumstances and we agreed. Patch details at https://t.co/VF3SqXHYV9 (1/2)
— Tim Willis (@itswillis) April 14, 2020
Tenable solutions
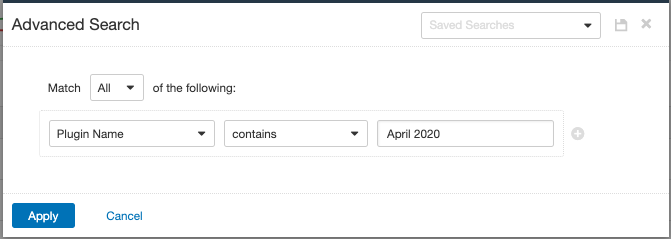
Users can create scans that focus specifically on our Patch Tuesday plugins. From a new advanced scan, in the plugins tab, set an advanced filter for Plugin Name contains April 2020.
With that filter set, click the plugin families to the left and enable each plugin that appears on the right side. Note: If your families on the left say Enabled, then all the plugins in that family are set. Disable the whole family before selecting the individual plugins for this scan. Here’s an example from Tenable.io:
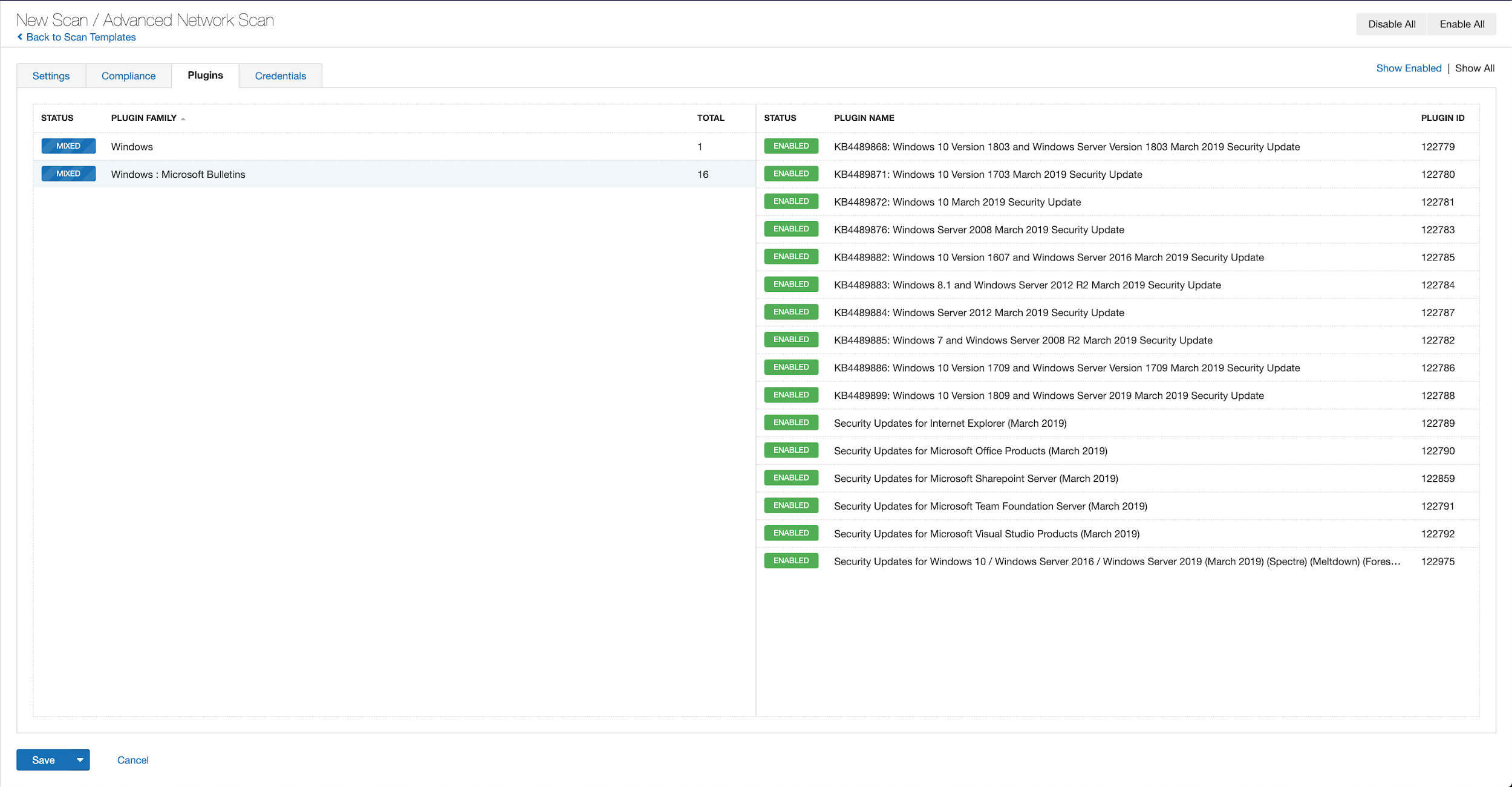
A list of all the plugins released for Tenable’s April 2020 Patch Tuesday update can be found here. As always, we recommend patching systems as soon as possible and regularly scanning your environment to identify those systems yet to be patched.
Get more information
- Microsoft's April 2020 Security Updates
- Tenable plugins for Microsoft April 2020 Patch Tuesday Security Updates
Join Tenable's Security Response Team on the Tenable Community.
Learn more about Tenable, the first Cyber Exposure platform for holistic management of your modern attack surface.
Get a free 30-day trial of Tenable.io Vulnerability Management.
Learn more
- Vulnerability Management



Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success