Master Your Security Foundation: Control the Use of Administrative Privileges

What did the Sony and Anthem breaches have in common with an estimated 60-80% of all breaches? They all involve the use of compromised privileged (administrative) accounts.
Attackers using administrative credentials can move laterally across your network to conduct internal reconnaissance, maintain a presence, and ultimately accomplish their missions. Last year, The Forrester Wave™: Privileged Identity Management, Q3 2016 estimated that 80% of security breaches involve privileged credentials. It stated, “Privileged credentials provide greater scope for stealing data en masse than individual accounts do: With privileged credentials, attackers can dump the entire database, bypass network traffic limitation, delete logs to hide their activity, and exfiltrate data easier.”
The Cybersecurity Frameworks and Foundational Security Controls survey, sponsored by Tenable and the Center for Internet Security, uncovered a significant gap between organizations’ policies to control use of administrative privileges and the implementation of controls needed to enforce those policies. For example, 67% of respondents said they have implemented policies to change all default passwords for applications, operating systems, routers, firewalls, wireless access points and other systems. However, fewer than 45% have implemented automated or even manual controls to enforce their policies.
Let that sink in. One third of organizations do not have policies to change default administrative passwords. And that even when policies exist, they are not widely enforced. Clearly, many organizations need to up their game.
Human nature being what it is, we are prone to take shortcuts and share administrative credentials across systems and across multiple administrators, as well as grant administrative privileges to users so they can install software themselves without troubling IT.
True story: I once worked with a small company that used the same shared administrative credentials across all of their enterprise applications. To make matters worse, the credentials were written down and kept on the lead administrator’s desk. If a disgruntled insider or an outside attacker got hold of credentials, he could anonymously access everything. Perhaps this is why the Center for Internet Security included “Controlled Use of Administrative Privileges” in the top five Foundational Cyber Hygiene Controls.
Tenable can help
SecurityCenter Continuous View® includes multiple reports, dashboards and Assurance Report Cards® that can help you monitor and evaluate the use of administrative privileges. For example, the CIS CSC Account Monitoring and Control dashboard is quite useful.
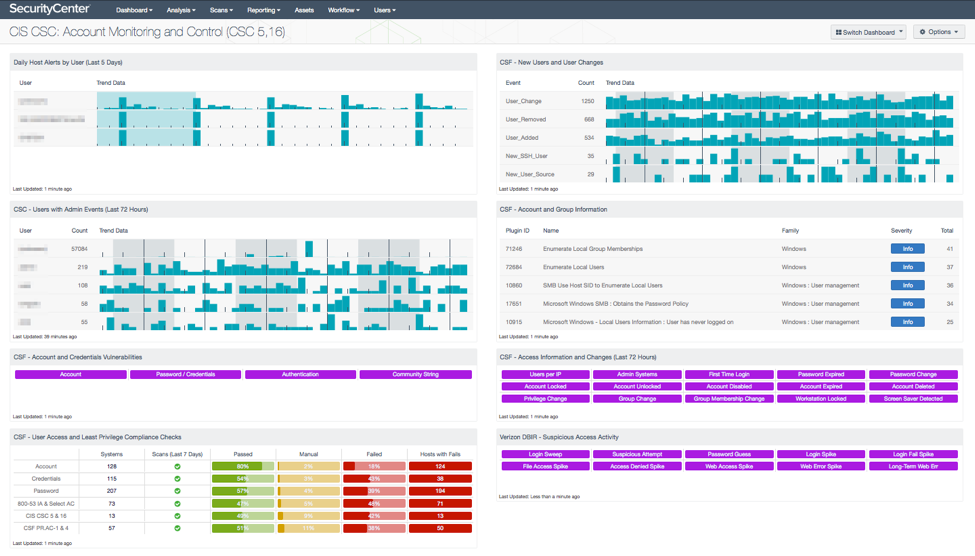
Two components in the lower left of the dashboard are especially useful:
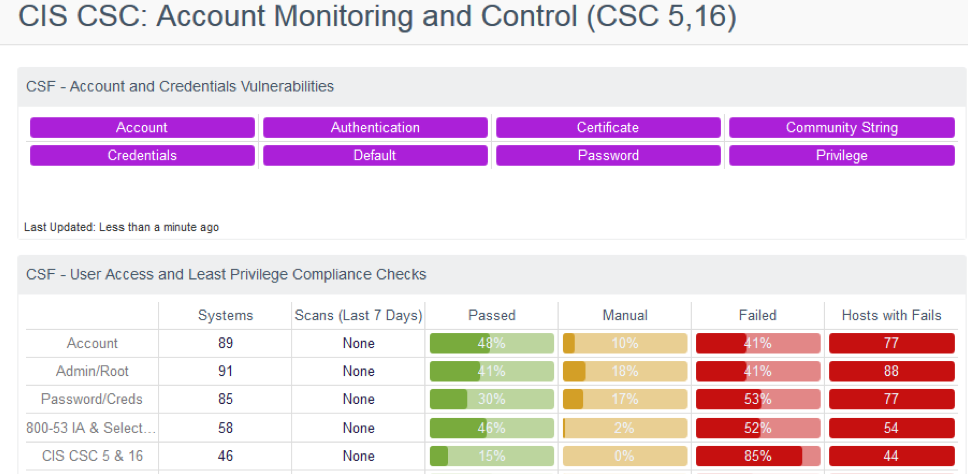
The CSF - Account and Credential Vulnerabilities component displays warning indicators for vulnerabilities related to accounts and credentials. A purple indicator means that one or more vulnerabilities contain the specified keyword. You can drill in to investigate the specifics. I clicked on the Account indicator and discovered that one of my hosts had a guest account with excessive privileges. When I looked at the details, I was informed by plugin 10907 that “Using the supplied credentials, Nessus was able to determine that the 'Guest' user belongs to groups other than 'Guests' (RID 546) or 'Domain Guests' (RID 514). Guest users should not have any additional privileges.
The CSF - User Access and Least Privilege Compliance Checks component displays results of compliance checks pertaining to areas such as password requirements, lockout policy after failed logins, and controlled use of administrative privileges. You can click on a highlighted indicator in the Host with Fails column to investigate the systems with failed audit checks.
Learn more
Tenable is hosting a webinar on July 12th where we will dive into the CIS control details and show you how Tenable can help. This webinar is the last of a five-part series that explores each of the CIS Foundational Cyber Hygiene controls. Brian Ventura, a SANS community instructor, will be our expert guest presenter. Brian teaches a 2-day course, Critical Security Controls: Planning, Implementing and Auditing. He has also taught a 5-day course, Implementing and Auditing the Critical Security Controls – in Depth. A CyberArk representative will show you how they can help you manage privileged credentials. We will also reserve time for questions and answers.
Please register even if you can’t attend so we can send you a link to the recorded webinar to view at your convenience.
Learn more
- Active Directory
- Center for Internet Security (CIS)
- Risk-based Vulnerability Management
- Security Frameworks
- Threat Management
- Vulnerability Management



Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success