How to Audit Microsoft Exchange 2013 and 2016 with CIS and DISA Guidance

Tenable Research Release Highlights are posted for significant new releases or updates to existing plugins or audit files that are important for early customer notification. Here, we discuss new audit guidance for Microsoft Exchange.

Microsoft Exchange remains one of the most widely adopted email and calendar solutions. Establishing a secure baseline configuration for Exchange, based on industry leading guidance, is essential but the complexity in deployments can present a challenge. The Center for Internet Security (CIS) and Defense Information Systems Agency (DISA) have issued guidance on hardening and auditing these deployments. Tenable released plugin enhancements and audits to help customers implement this guidance on July 1.
CIS Benchmarks for Microsoft Exchange
- CIS Microsoft Exchange Server 2016 Benchmark v1.0.0
- CIS Microsoft Exchange Server 2013 Benchmark v1.1.0
DISA STIGs for Microsoft Exchange
- Microsoft Exchange 2013 Client Access STIG - Ver 1, Rel 2
- Microsoft Exchange 2013 Edge Transport Server STIG - Ver 1, Rel 5
- Microsoft Exchange 2013 Mailbox STIG - Ver 1, Rel 4
- Microsoft Exchange 2016 Edge Transport Server STIG Ver 1, Rel 2
- Microsoft Exchange 2016 Mailbox Server STIG Ver 1, Rel 2
Usage Overview
Tenable customers can audit an MS Exchange server with all of the same check types as in our Windows Compliance Plugin, as well as with a new check type, AUDIT_EXCHANGE. This new check type leverages the Exchange-specific cmdlets suggested for use in the audit steps of DISA and CIS recommendations.
The following is an example check using AUDIT_EXCHANGE:
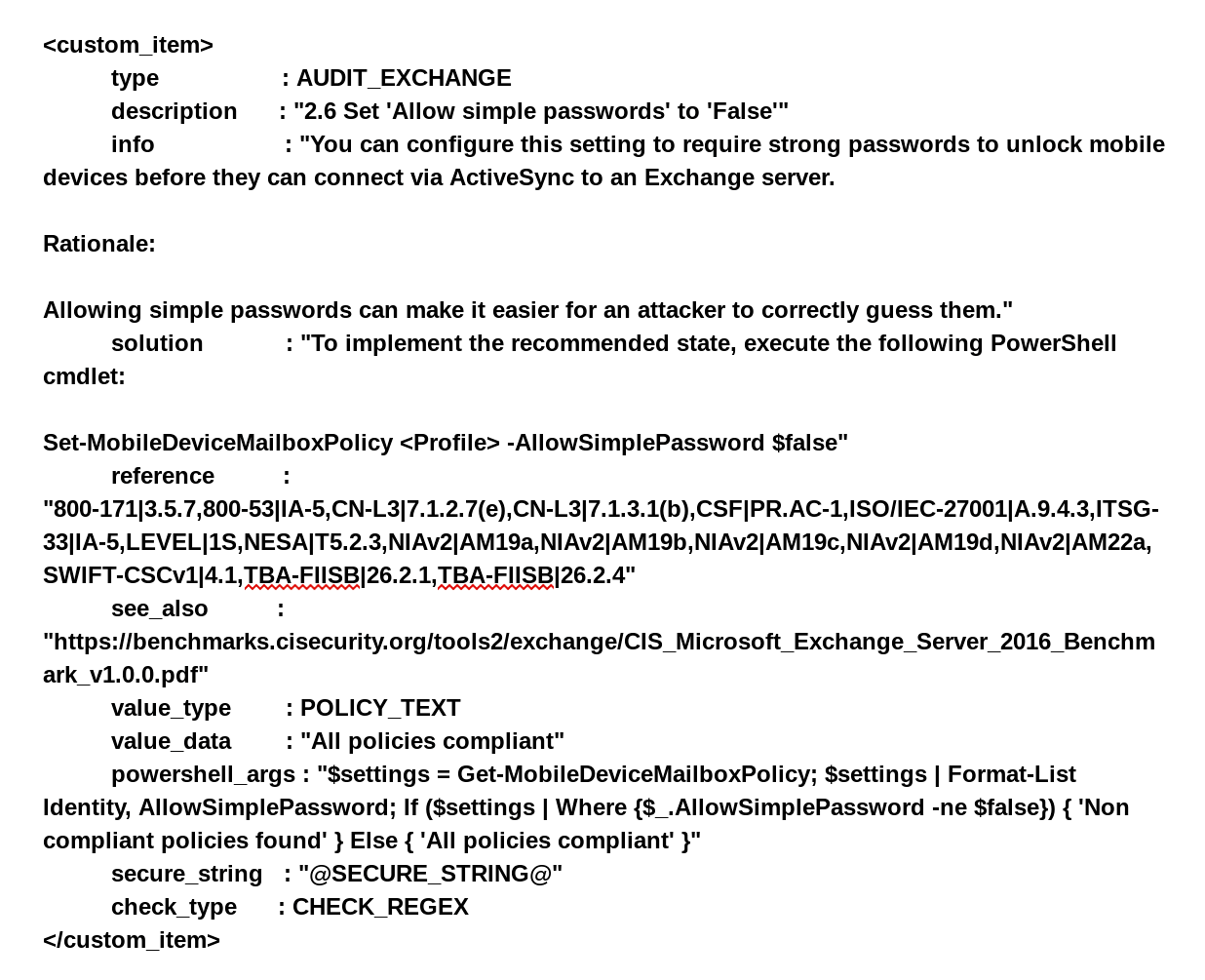
The powershell_args tag contains the core of the audit functionality, with the plugin itself connecting and exposing Exchange specific cmdlets. As a result, the EMS/Exchange cmdlet import is seamless to the user, who can instead focus on writing good powershell.
How to get started
A byproduct of the session setup and cmdlet import is that we need to work with powershell credential objects. In order to avoid unintended disclosure of credential information via powershell logs, users are required to use a pregenerated encrypted password string for each target of the audit as part of what we require in the Exchange Auditing scan setup.
Password/Secure String Generation
In order to generate an encrypted password for use with our Exchange audits, run the following powershell while logged in on the target with the account that will be used for scanning:
Read-Host -AsSecureString | ConvertFrom-SecureString
While logged into the account you’ll be using to scan, type in the password for the account. The output will look like this:
01000000d08c9ddf0115d1118c7a00c04fc297eb010000005ad58de852cc4646b0d9dfa96c67f2100000000002000000000003660000c0000000100
00000d8b09ba7e13918c19d776cc7dfcac82a0000000004800000a0000000100000003654a47ae8a4da017657d57f0706989e180000004acd2fe799
0e1243ed84c380e5d0e8a95a01f12f5662574714000000e5b4783976f1ad76065cf6f91a3b1bebbcf4b169
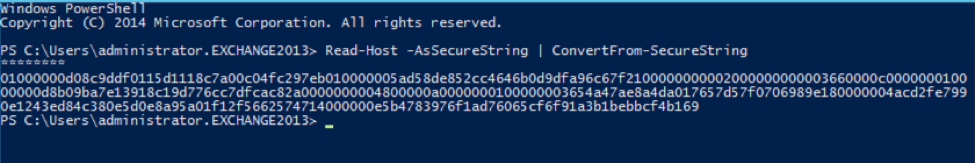
Reminder: An encrypted password is required for each target being scanned.
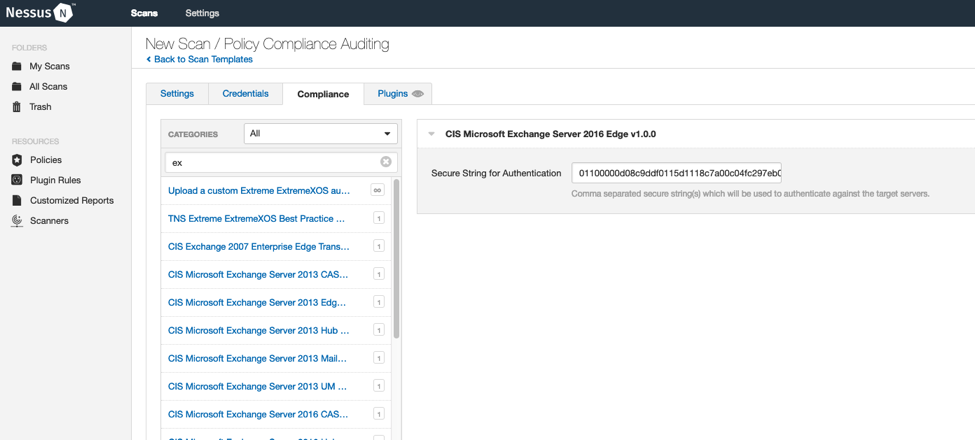
After creating the string from the instructions, make sure to select the audit under the Windows category and populate the secure string variable (separating multiple targets with commas). The plugin will determine which string to use on which target. Add your usual credential information on the credential tab and save the policy.
Once the configuration is saved, run the scan and review the results.
Example Scan output
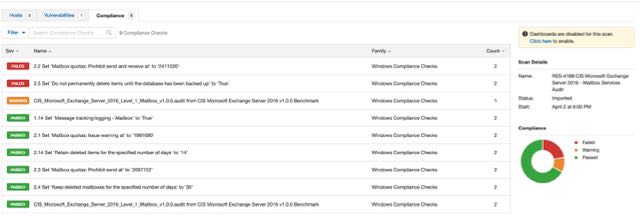
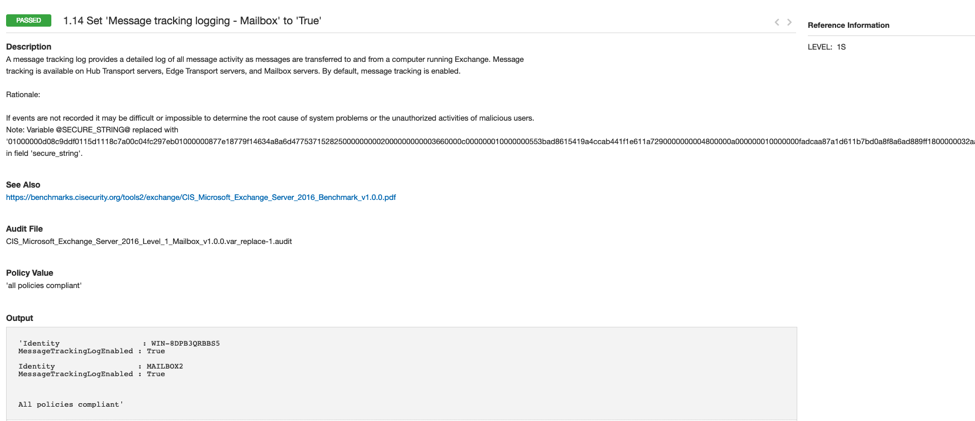
Below is a closer view of one of the results. This page shows:
- Pass/fail status
- Remediation steps, if necessary
- Individual results from the systems scanned
Summary
Auditing an Exchange Environment with Tenable.io and Nessus requires a little bit of extra setup but allows for a secure and automated method for evaluating your organization’s compliance. Exposing Exchange specific cmdlets allows for much more accurate auditing of the environment, with a direct correlation to industry guidance. At Tenable, we regularly update our policy compliance audits to match the newest versions by CIS and DISA to ensure our customers are able to keep pace with the latest best practices.
Follow Tenable Research Release Highlights on the Tenable Community.
- Security auditing
- Security Frameworks
- Security Policy
- Standards
- Threat hunting
- Threat Intelligence
- Threat Management
- Vulnerability Management
- Vulnerability Scanning
